My background going into the CRTO after the OSCP+
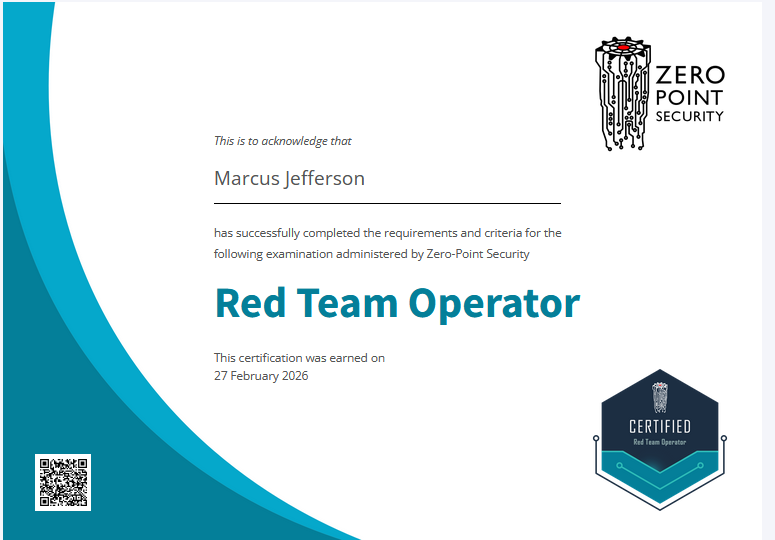
After finishing the OSCP+ exam a few months ago, I was looking for a new challenge and I’ve seen many offensive security practitioners recommend Zero Point Security’s Certified Red Team Operator course.
Prior to beginning the exam I had very little to no experience working with command and control (C2). I also had very little knowledge of windows internals, how malware functionally works, and anti-virus evasion techniques. This course did a great job of providing me with a solid background in all of these topics but didn’t bog me down too much in theory.
Evading anti-malware software is an unending cat and mouse game so its impossible to learn timeless techniques; however the CRTO course blended actionable techniques I could currently use to bypass modern windows defender with enough foundational knowledge that you leave the course with an understanding of what you may need to do in the future to bypass AV and what to look for in new techniques as they come out.
The course is also of course an amazing way to gain experience using cobalt strike if you don’t have access to a license. I imagine the knowledge garnered from using cobalt strike will translate well to other C2 frameworks like mythic or silver which people commonly use for the OSEP.
The Exam taking Experience
The conditions that you’re able to take the CRTO exam in are rather generous and pleasant. The ability to do the exam over the course of 7 days with as many pauses was a much better experience than the 24 hours proctored OSCP+ exam. It is also really nice knowing that if you fail you can simply try again without incurring a large cost (as of unlimited retakes policy currently).
The Exam itself
The CRTO exam itself was rather fun and pleasant. The current course doesn’t provide a large playground for testing out a full red team engagement from start to finish so it can definitely be intimidating at first, but once you get the infrastructure stuff out the way (configuring your malleable C2 profile, tweak your artifact and resource kits, generate new payloads, setup listeners, etc) and start attacking the environment its a good time. There aren’t too many rabbit holes which was another nice change of pace from the OSCP+ exam. With proper enumeration the path forward is clear, you just need to stay calm and execute given the information from the course.
Exam Tips
- Have a good understanding of core concepts: Make sure that you have a great understanding of the Kerberos and forest and domain trust topics in the course. They are very important for active directory exploitation and play a strong role in the exam as such. I would also spend some extra time looking at the defense evasion and AppLocker sections.
- Pay close attention to the Opsec notes in the course and in the exam information page. Some general Opsec tips include the following:
- Make sure to set up your malleable C2 profile before setting up your listeners and then inevitably generating your payloads. At the point where you are adding the artifact and resource cna files you might as well add the BOFs you like using. I made sure to add the kerbeus, sql, and scshell BOFs.
- When setting up your listeners, following the lab instructions in the cobalt strike primer section are a good bet. Particularly make sure to change the SMB beacon named pipe to something that may blend into the target environment as the default will be heavily signatured by defender.
- Enumerate applocker closely
- Avoid injecting your beacon into a users process, steal their token instead of look at the kerberos tickets on the system once you have system
- Use the recommended lateral movement method to move quietly. At the time of me taking the exam that is scshell64.
- Have your lab notes handy: Following the steps from the defense evasion lab to setup your infrastructure stuff should be good enough, but feel free to mess around and tweaks things to your own liking.
- Take breaks: I struggled with taking breaks. There we’re many times I’d be slamming my head against the wall looking for something for an hour or two then begrudgingly take a break and after I came back I’d suddenly know the answer. The exam format is designed to not be stressful, so don’t torture yourself ceaselessly. For me at least, taking little or big breaks helped a lot to approach the problem with fresh mind and new perspective.
- Don’t over think the toolkit: Everything you need will be available to you!
- Check out the discord: The Zero Point Security discord community seems pretty friendly, and if you’re having a problem in one of the labs chances are someone else has already had that problem and you can search up the solution in the discord.
- Leverage cheat sheets: If you don’t have a compendium of commands you’ll commonly run I’d recommend making your own, using mine, or one of the many other great ones online. I’ll link mine and another one I liked below!