Recon MGT
Challenge 15. What is the domain of the users of the wifi-regional network
In MGT networks misconfigured users can send their Identity (username) in clear text before performing the TLS tunnel, so with “airodump-ng” we can passively obtain this information. For this we simply use “airodump-ng” on the correct channel and wait for the clients to connect.
Put card into monitor mode
sudo airmon-ng Start a network capture
sudo airodump-ng --band abg --manufacturer --wps wlan0mon
BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH WPS ESSID MANUFACTURER
F0:9F:C2:71:22:16 -25 4 0 0 44 54e WPA2 CCMP MGT 0.0 wifi-regional Ubiquiti Netw
now I have the channel, filtering for that and the bssid
sudo airodump-ng --band abg --manufacturer --wps wlan0mon --bssid F0:9F:C2:71:22:16 -c44 -w scanThen I want to open that pcap in wireshark and filter by eap
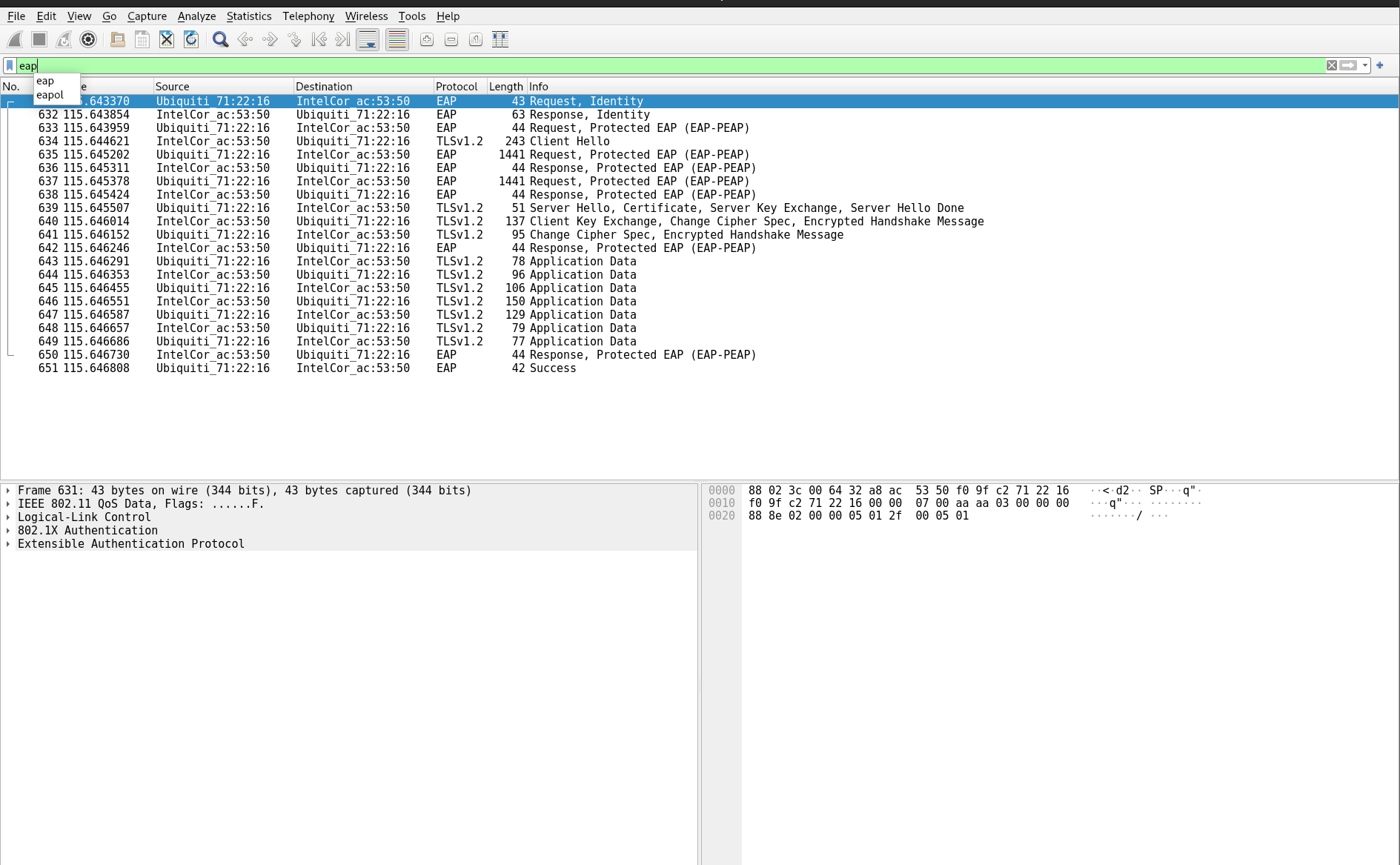
Expanding the extensible authentication protocol tab and clicking through the packets that say response identity I can find the domain of the users
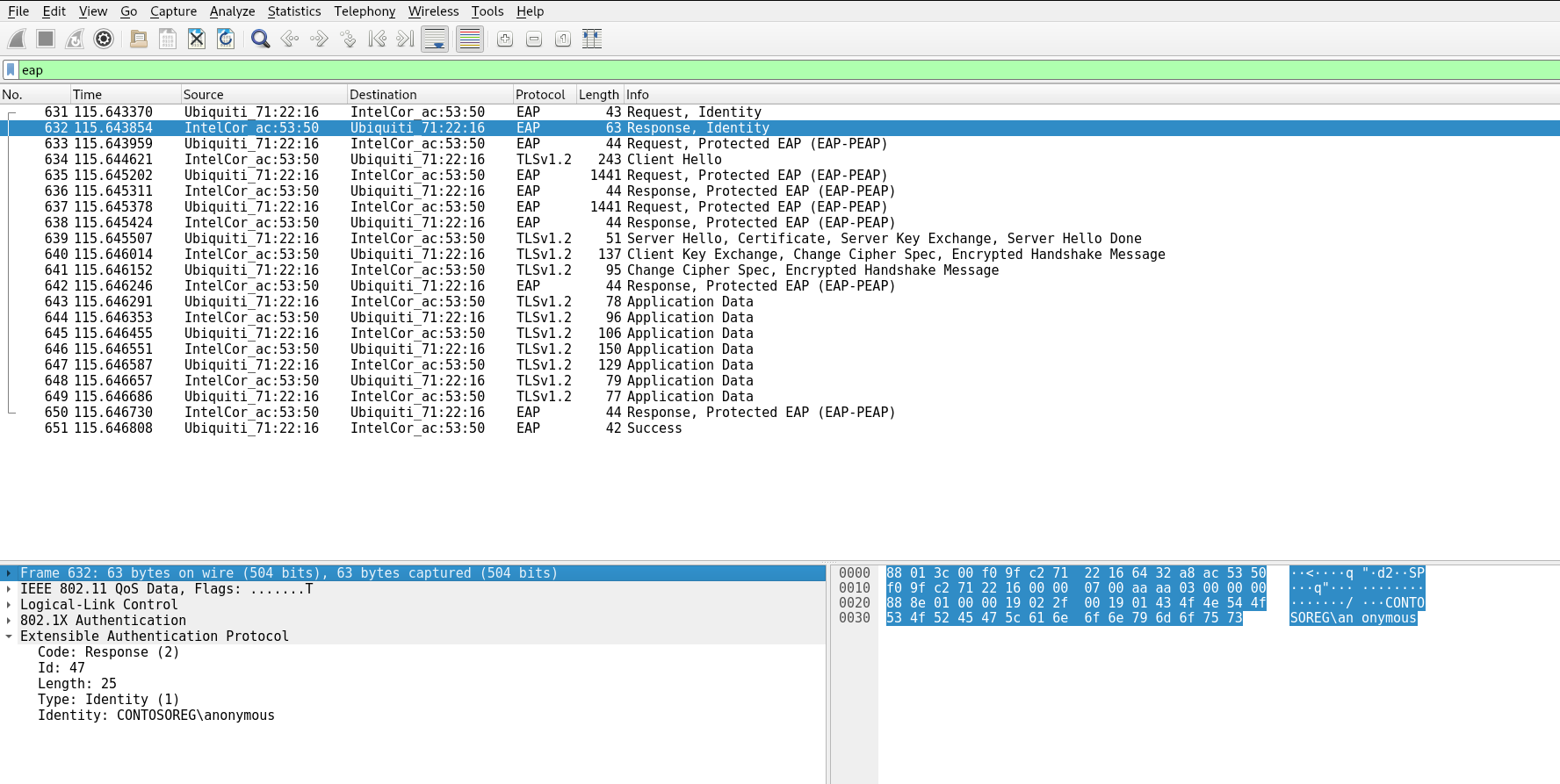
/CONTOSOREG\anonymous
ContosoregChallenge 16. What is the email address of the servers certificate?
Going through the wireshark capture from the above question the obvious place to look for the email address of the server certificate is the packet with the word certificate in the INFO column.
See screenshot
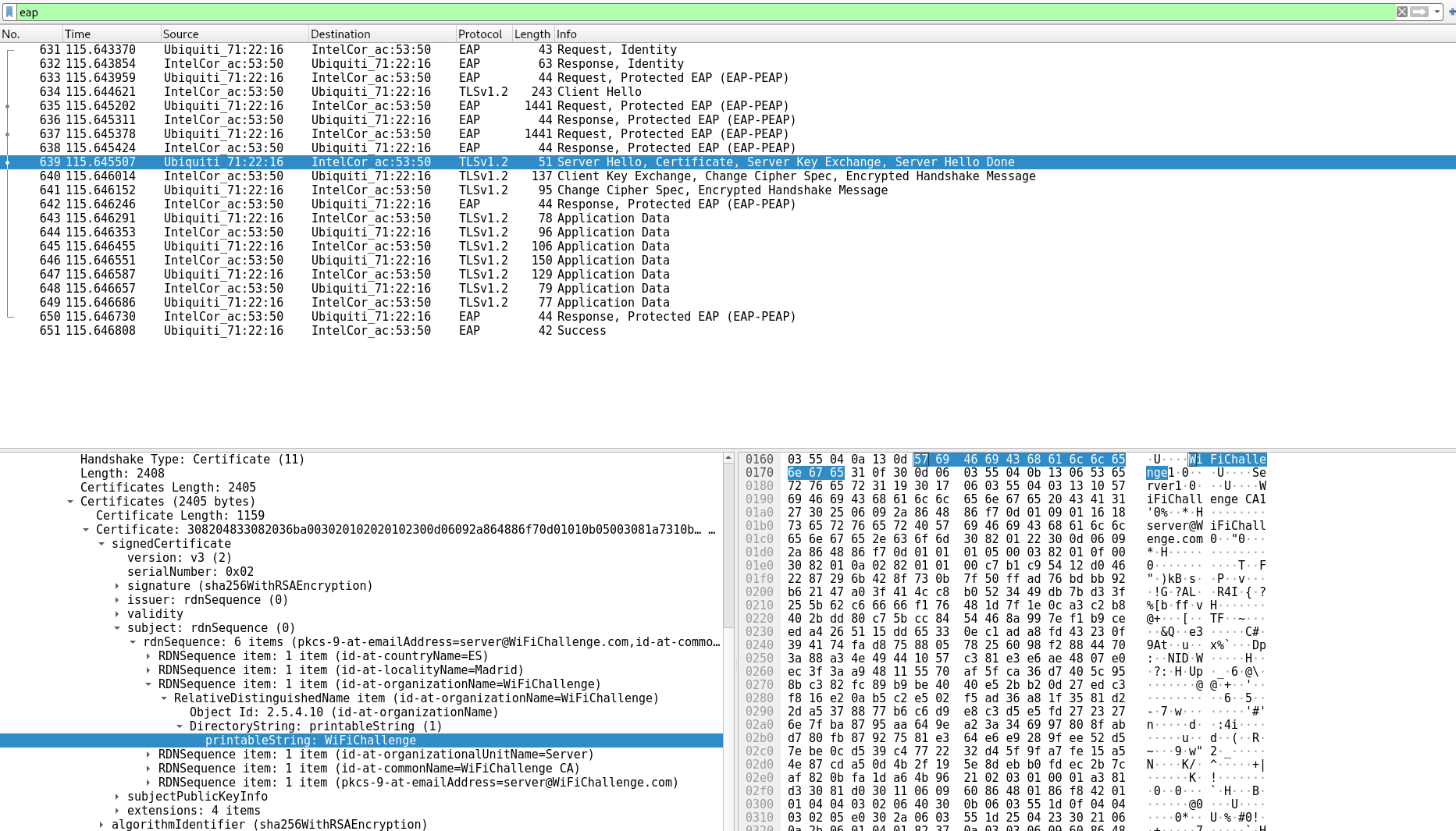
Expanding the RDN sequence item tab
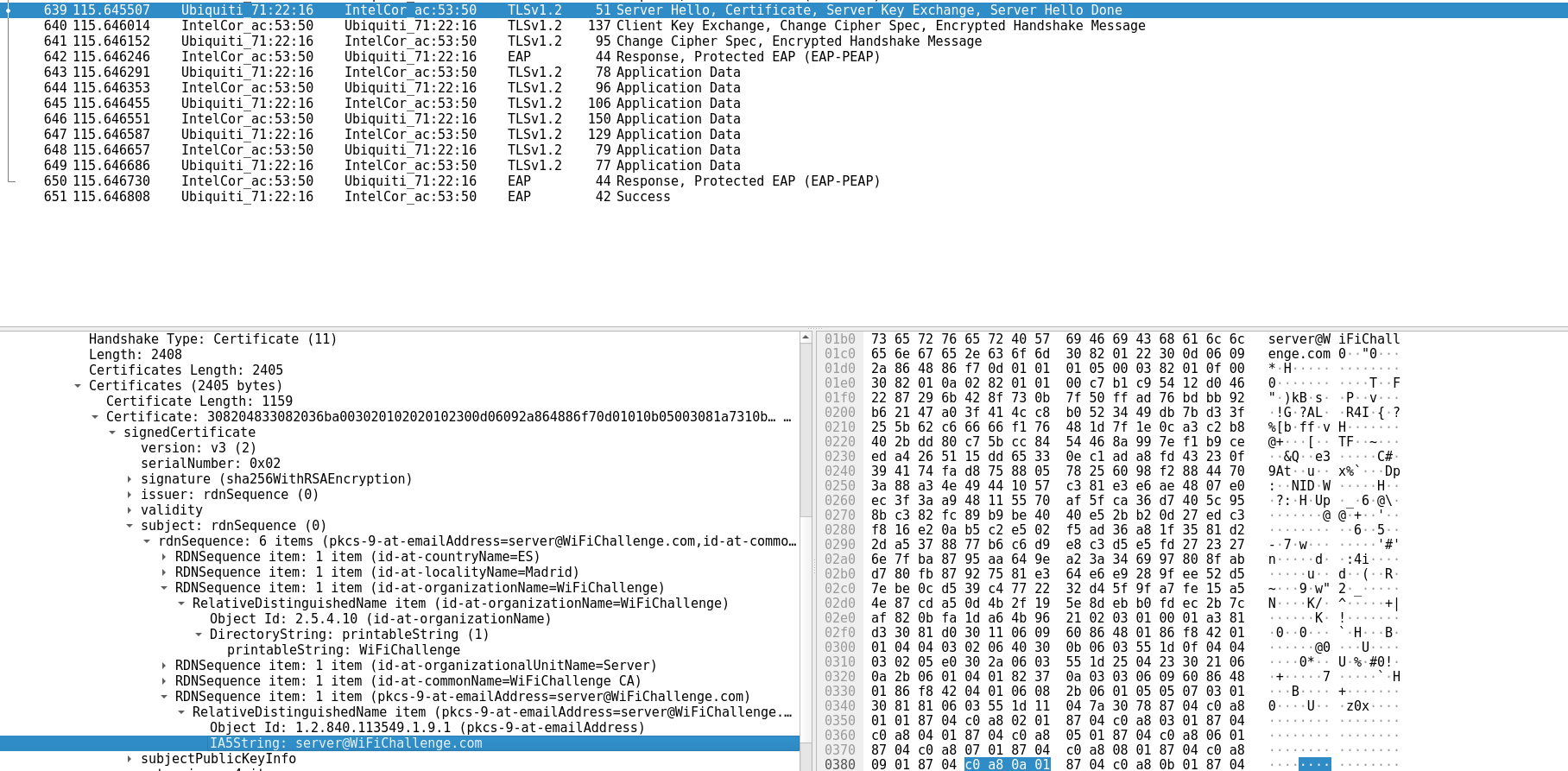
server@WiFiChallenge.com
Challenge 17. What is the EAP method supported by the wifi-global AP
sudo airodump-ng --band abg --manufacturer --wps wlan0mon
BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH WPS ESSID MANUFACTURER
F0:9F:C2:71:22:17 -25 6 6 0 44 54e WPA2 CCMP MGT 0.0 wifi-global Ubiquiti Networks Inc.
Using wifidb to enumerate access points
python3 wifi_db.py -d wifichallenge.SQLITE <directory you output scans in>open the db
sqlitebrowser wifichallenge.SQLITEbrowse data —> identity AP
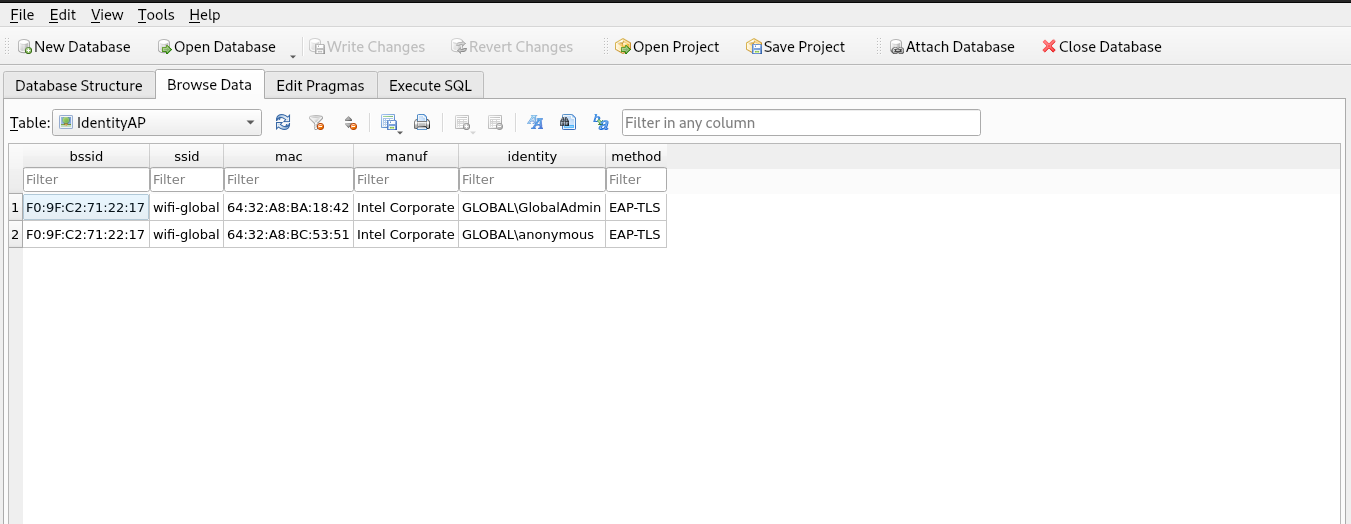
in the identity tab I get two usernames I can use with eapbuster to determine the eap method
GLOBAL\anonymous
GLOBAL\GlobalAdminrun eap buster this can produce false positives, be sure to run a airmon-ng check kill before hand
sudo airmon-ng check kill
root@WiFiChallengeLab:~/tools/EAP_buster# bash ./EAP_buster.sh wifi-global 'GLOBAL\GlobalAdmin' wlan1
eventually it will tell us EAP-TLS is the method