Ffuf Web Enumeration Skills Assessment
Target: 94.237.54.42:34587
Run a sub-domain/vhost fuzzing scan on '*.academy.htb' for the IP shown above. What are all the sub-domains you can identify? (Only write the sub-domain name)
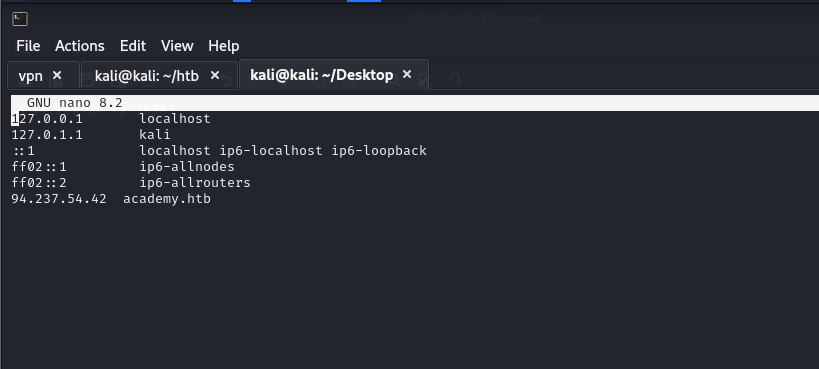
Add new IP to /etc/hosts file for the academy.htb domain
Running subdomain fuzzing scan on *.academy.htb
ffuf -u http://FUZZ.academy.htb:34587 -w /usr/share/wordlists/seclists/Discovery/DNS/subdomains-top1million-5000.txtat the same time running vhost fuzzing using the host header on the *.academy.htb end point
ffuf -u http://academy.htb:34587/ -H 'Host: FUZZ.academy.htb' -w /usr/share/wordlists/seclists/Discovery/DNS/subdomains-top1million-5000.txt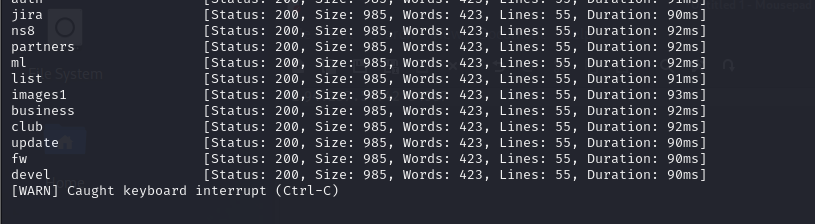
ffuf -u http://academy.htb:34587/ -H 'Host: FUZZ.academy.htb' -w /usr/share/wordlists/seclists/Discovery/DNS/subdomains-top1million-5000.txt -fs 985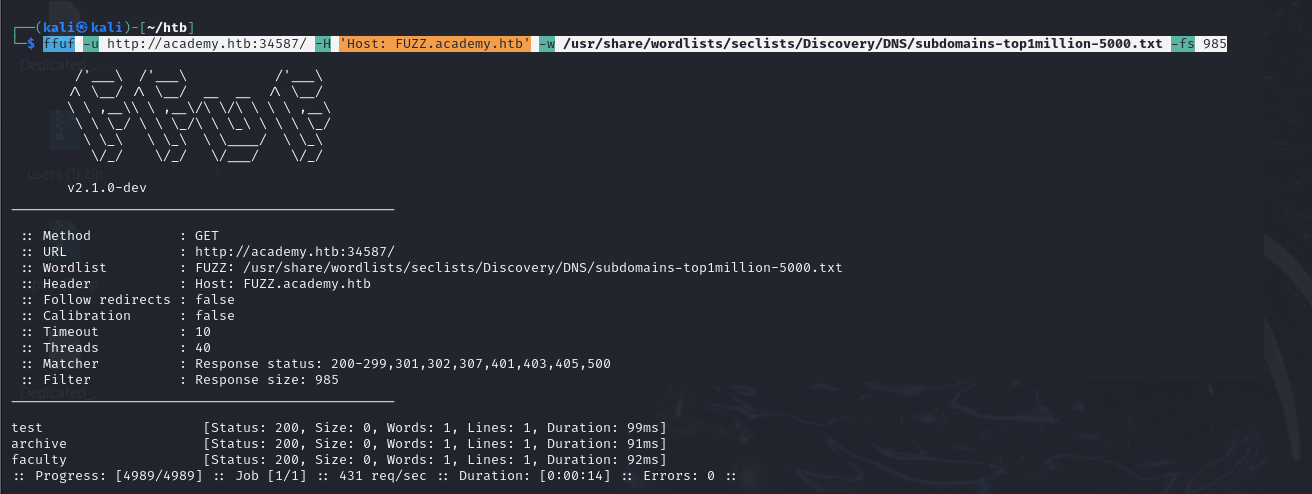
There we find: test, archive, faculty
My subdomain scans didn’t find these. I also ran the subdomain fuzzing scan with gobuster. That didn’t either.
Before you run your page fuzzing scan, you should first run an extension fuzzing scan. What are the different extensions accepted by the domains?
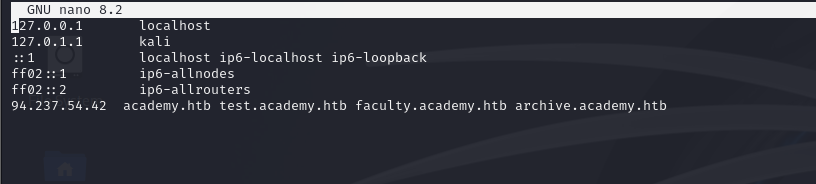
Add the discovered subdomains to etc/hosts
Fuzzing the test page for web extension types
ffuf -u http://test.academy.htb:34587/index.FUZZ -w /usr/share/wordlists/seclists/Discovery/Web-Content/web-extensions.txt
Doing the same for archive and faculty gave the same result: .phps, but the responses are 403 error
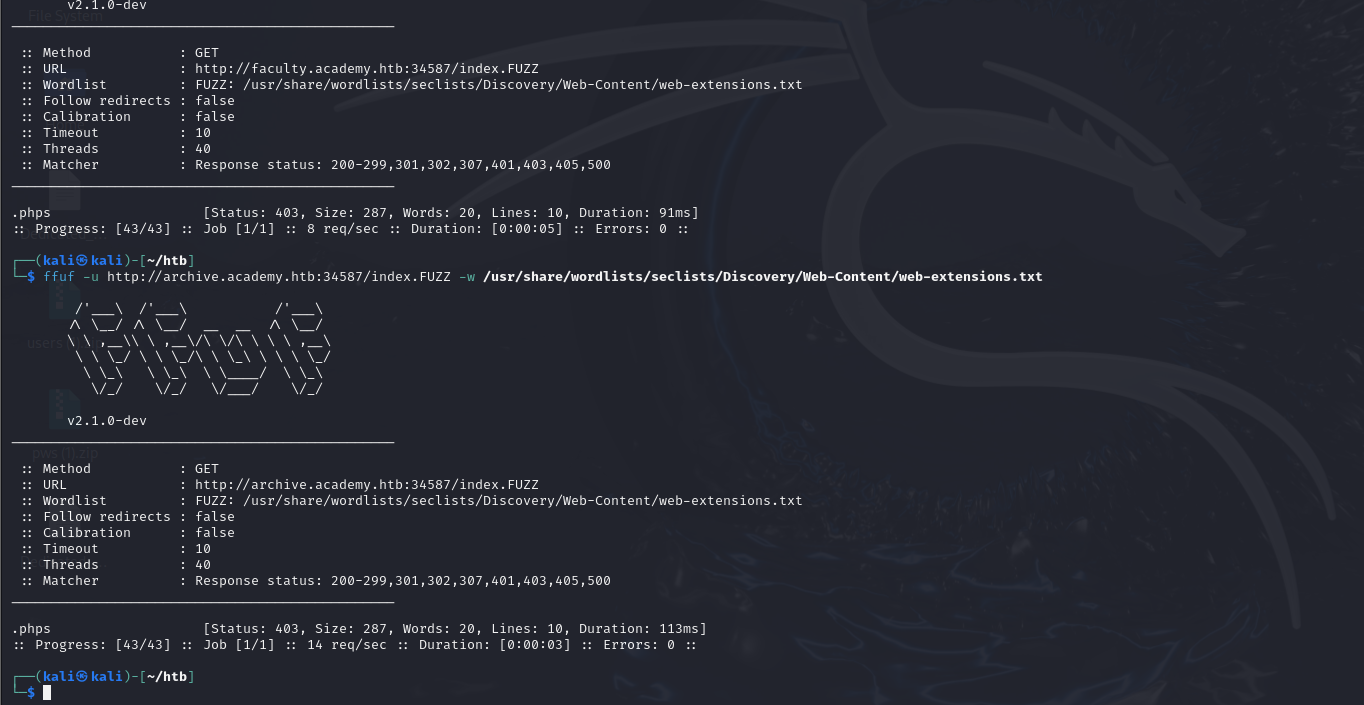
Looking back after some trouble shooting I realized I appended a . to the end point in my command which was giving some problems because my word list has a . before the extension already!
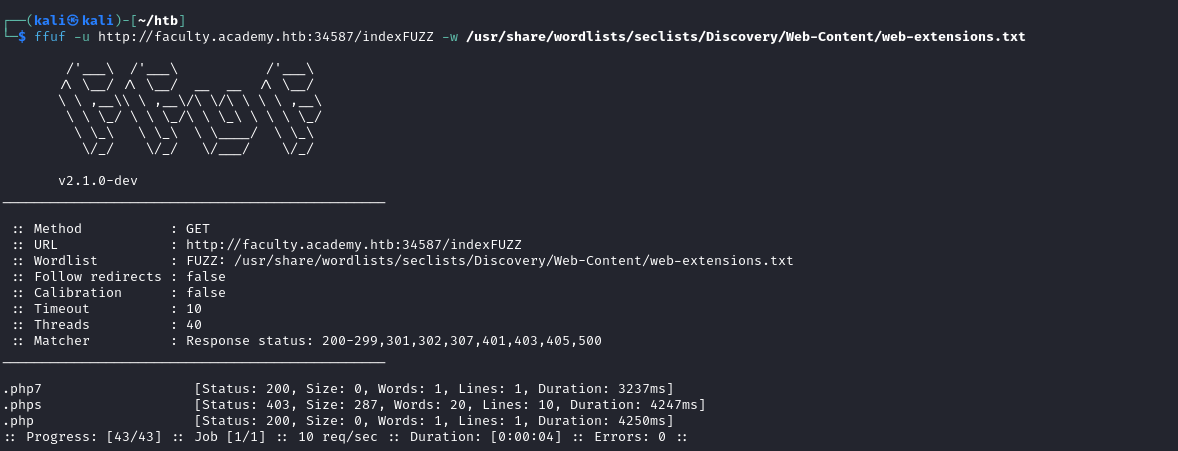
ffuf -u http://test.academy.htb:34587/indexFUZZ -w /usr/share/wordlists/seclists/Discovery/Web-Content/web-extensions.txtNow we get 2 web extensions: .php and .phps (with phps still giving a 403)
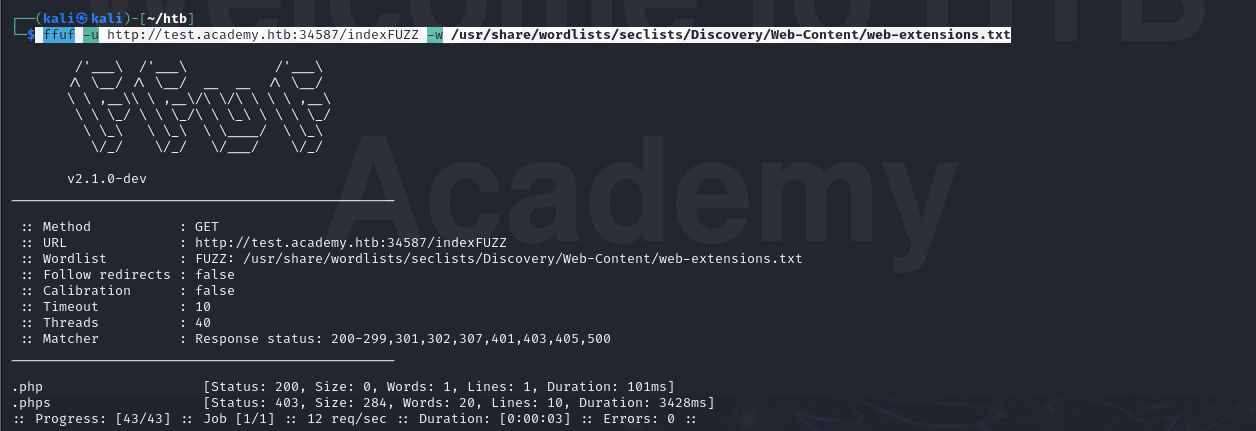
Running the scan on the other end points faculty shows a php7 extension being allowed as well
I decreased the transparency of the terminal after seeing the bold academy in the background of that last screen shot lol
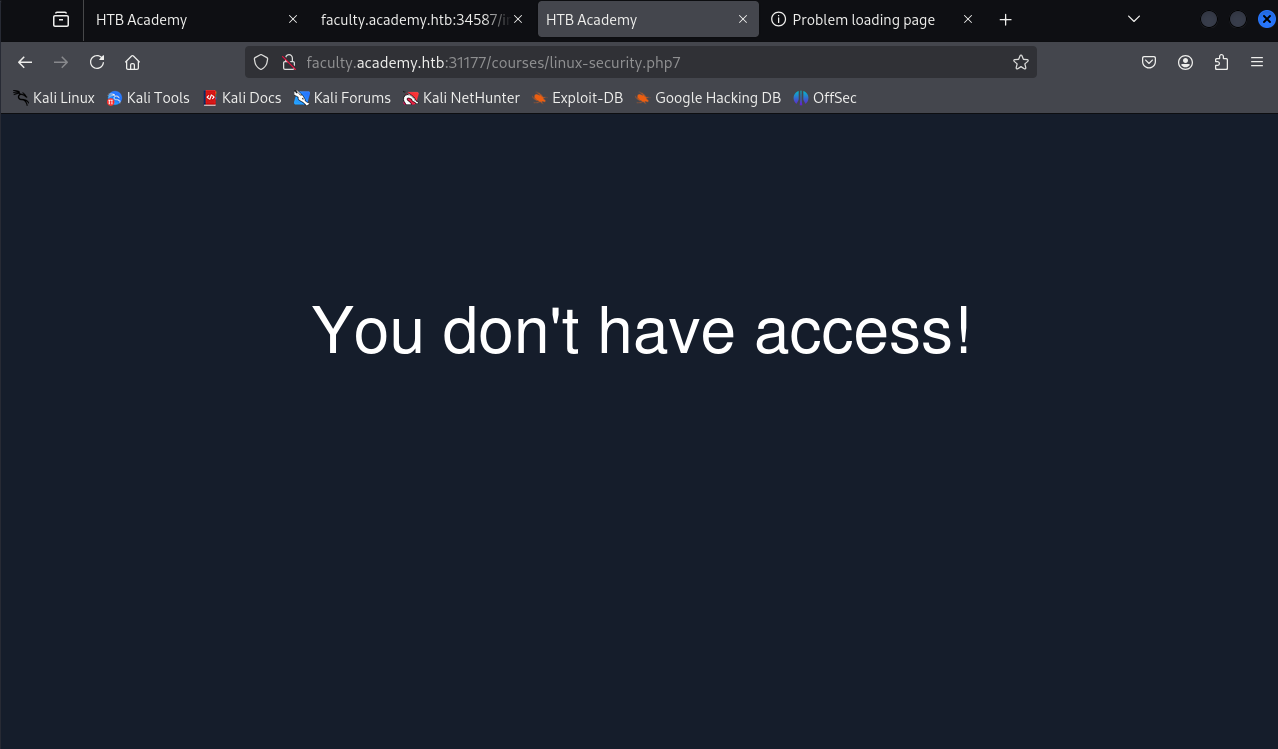
One of the pages you will identify should say 'You don't have access!'. What is the full page URL?
Going to the end points themselves (i.e. faculty.academy.htb, test, archive) just shows a white page. So I’m assuming they now want me to perform directory fuzzing on the subdomains discovered to find pages.
Now that I have some file extensions, fuzzing for pages
ffuf -u http://faculty.academy.htb:34587/FUZZ.php -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-small.txt -ic -t 200
Running this on all 3 end points didn’t find anything besides index
So at this point I took the hint, but it should’ve been clear to begin recursive scanning.
Make a file list of the discovered extensions
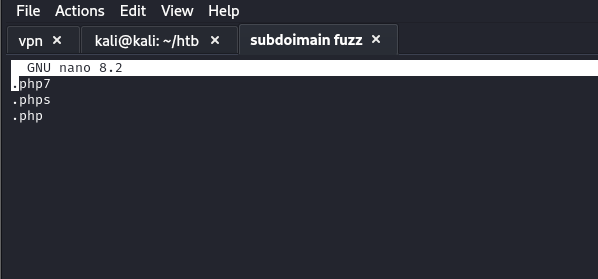
My first idea was using that list (after removing the . actually) so setup a command that would look the directory and the file extensions dynamically, but this failed because I didn’t realize that in Ffuf the end of the URL needs to be the FUZZ keyword when you are doing recursion. Technically not useful, but this is what it looked like, and the error.
ffuf -u http://faculty.academy.htb:34587/list1.list2 -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-small.txt:list1 -ic -t 200 -w extensions.list:list2 -recursion -recursion-depth 1
Encountered error(s): 1 errors occurred.
* When using -recursion the URL (-u) must end with FUZZ keyword.
So my next strategy was to use recursion, and just change out the file extension manually. Starting with .php as it seemed the most common.
Running the faculty fuzz scan I find http://faculty.academy.htb:34587/courses and the recursive fuzzing didn’t find anything past that
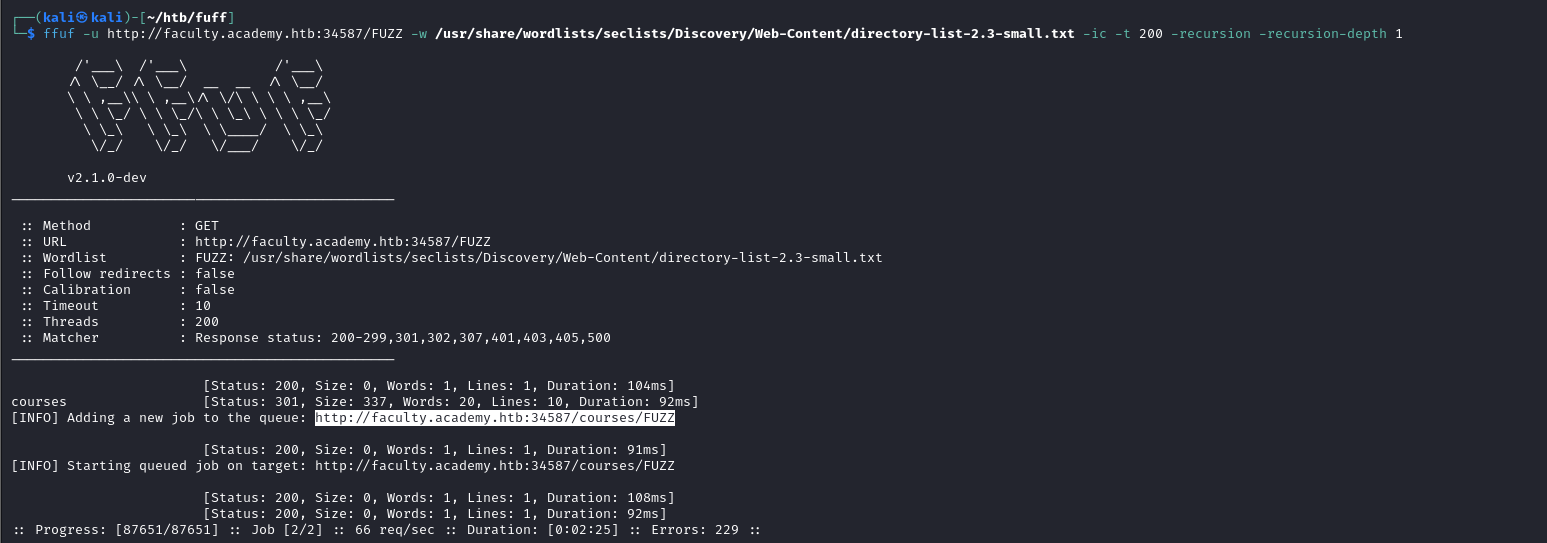
The Archive recursive also found the courses site.
At this point I had to run some errands so, the port is updated as is the IP in my hosts file
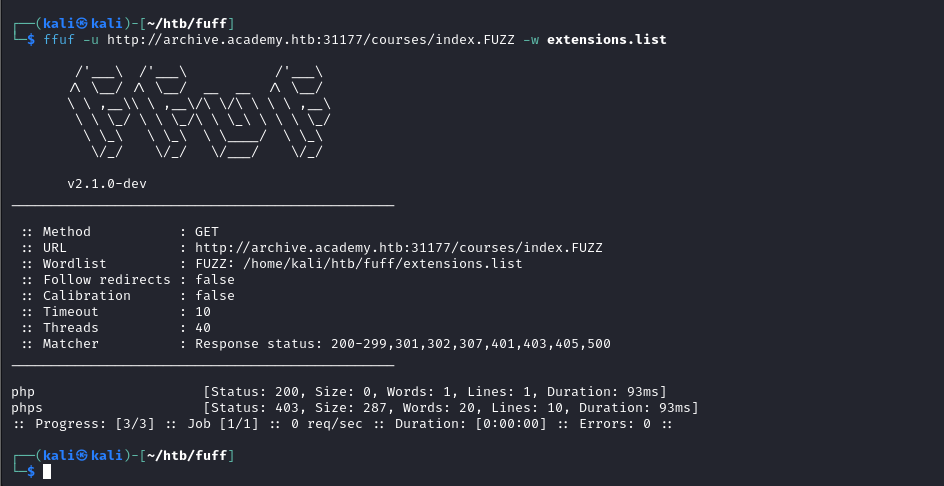
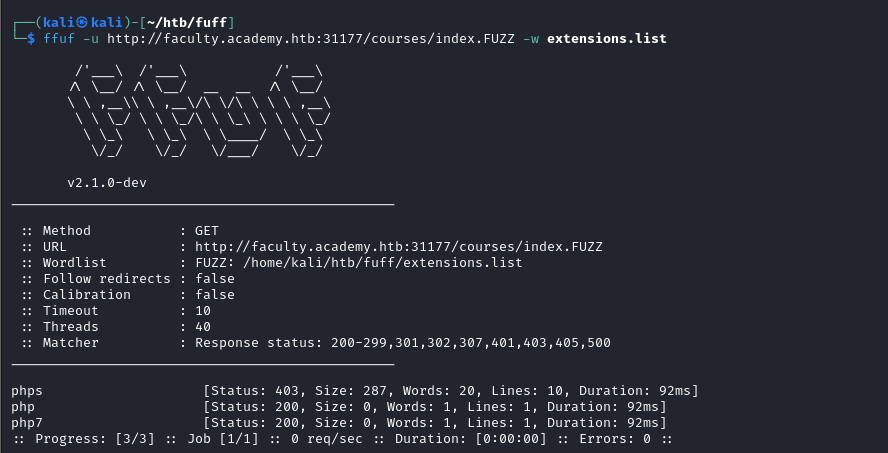
Having found the achive.academy.htb/courses and faculty.academy.htb/courses I think fuzzing those for index.FUZZ for different file extensions could be valuable
Fuzzing the file extension types for index on archive we find php:
Fuzzing the file extension types for index on faculty we find php and php7
Looking back at the question at this point I realize a 403 is a forbidden. So perhaps the 403 errors that I got fuzzing for file extensions under phps is the answer. That was not the case.
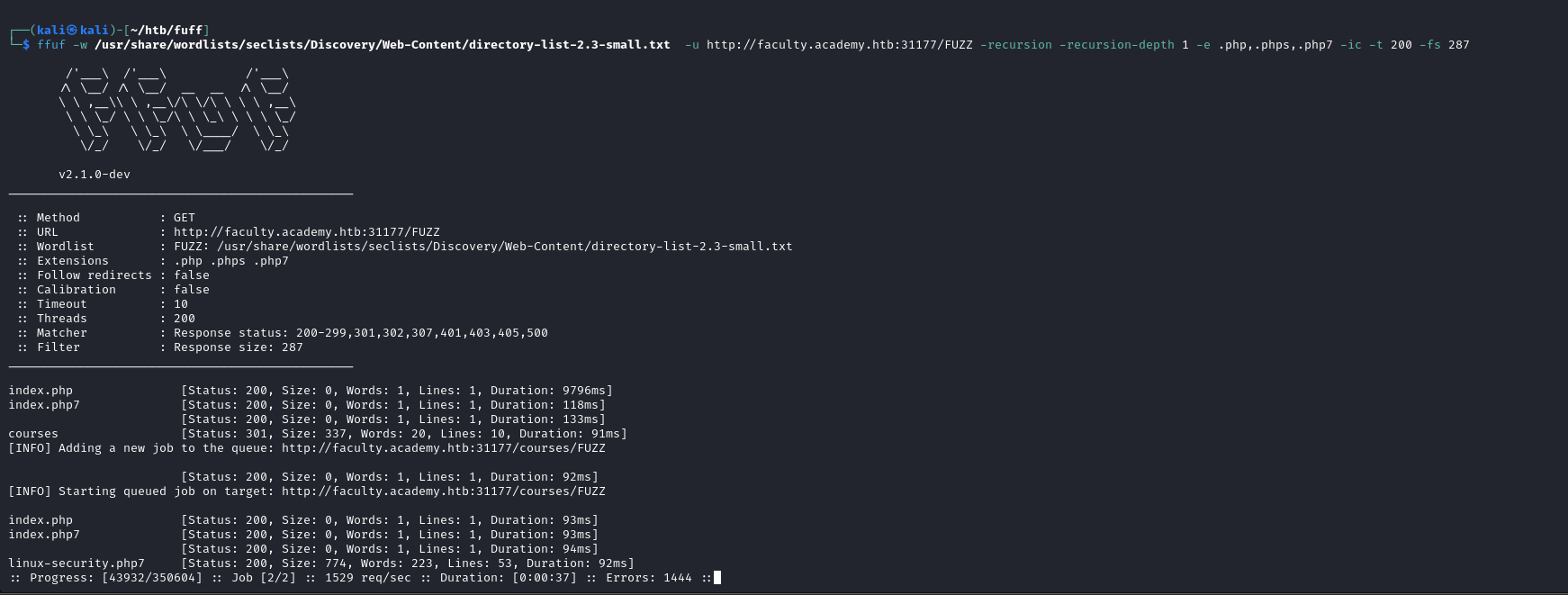
Taking a step back and doing some research I find that I can specify extension types using the -e flag. So I reperformed my recursive scans utilziing that feature on each of the 3 vhost
ffuf -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-small.txt -u http://test.academy.htb:31177/FUZZ -recursion -recursion-depth 1 -e .php,.phps,.php7 -fs 284 -ic -t 200
filtering for 284 here as it was the repetitive one the first time I ran thisI think repeating this step helped reframe my mind and goals after taking a step away from the lab. Eventually after much trial and error above I find: http://faculty.academy.htb:31177/courses/linux-security.php7
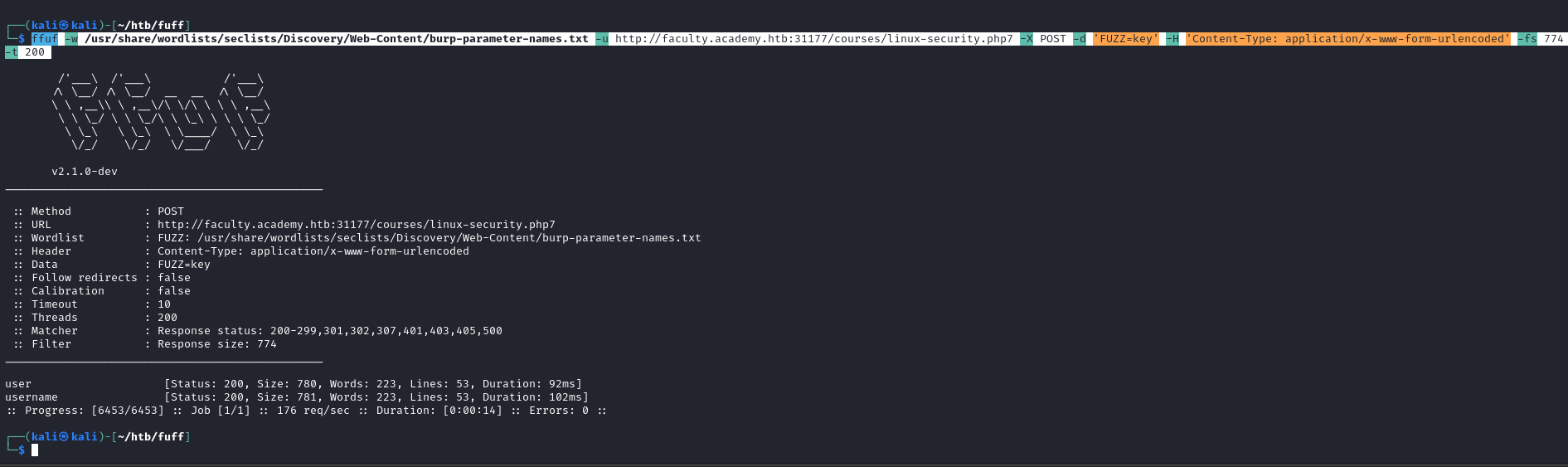
In the page from the previous question, you should be able to find multiple parameters that are accepted by the page. What are they?
Fuzzing get parameters using a word list on the page we find user
ffuf -w /usr/share/wordlists/seclists/Discovery/Web-Content/burp-parameter-names.txt -u http://faculty.academy.htb:31177/courses/linux-security.php7?FUZZ=key -fs 774 -t 200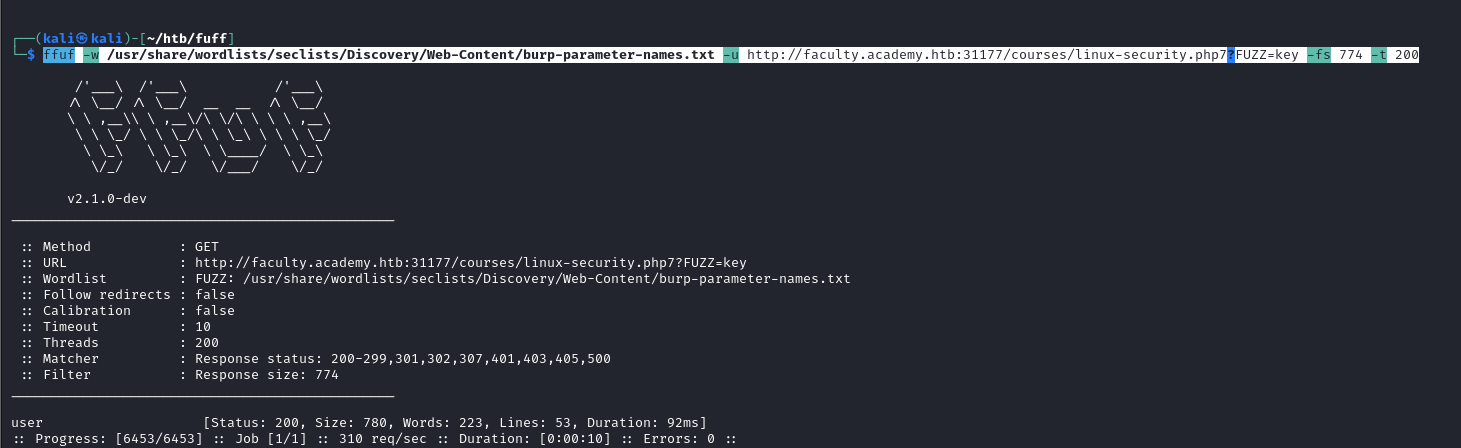
Attempting to access the site, now I get
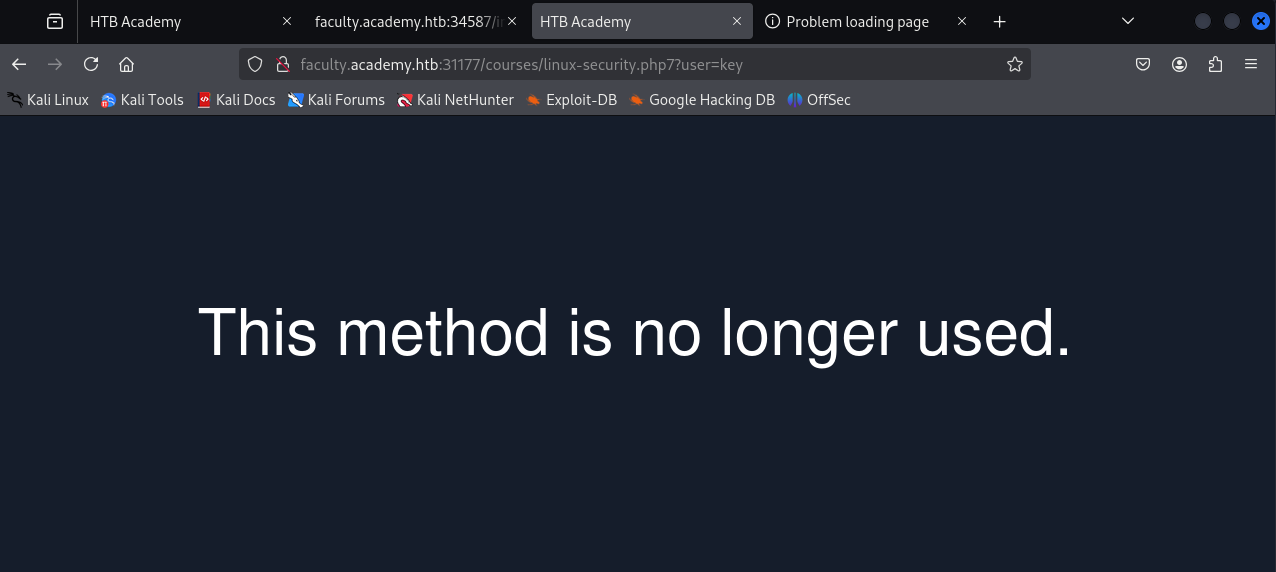
The question calls for multiple and fuzzing get request only found one parameter. So I fuzz post request too. Doing so I find user and username. So we have our multiple options now.
ffuf -w /usr/share/wordlists/seclists/Discovery/Web-Content/burp-parameter-names.txt -u http://faculty.academy.htb:31177/courses/linux-security.php7 -X POST -d 'FUZZ=key' -H 'Content-Type: application/x-www-form-urlencoded' -fs 774 -t 200
Try fuzzing the parameters you identified for working values. One of them should return a flag. What is the content of the flag?
I initially attempted just the ids list of numbers 1-1000 and that didn’t find anything, then the fact that one of the parameters was named username made me think to use a list of actual usernames.
Skimming through seclists I found one named names.txt at the following path on kali
/usr/share/wordlists/seclists/Usernames/Names/names.txtffuf -w /usr/share/wordlists/seclists/Usernames/Names/names.txt -u http://faculty.academy.htb:31177/courses/linux-security.php7 -X POST -d 'username=FUZZ' -H 'Content-Type: application/x-www-form-urlencoded' -fs 781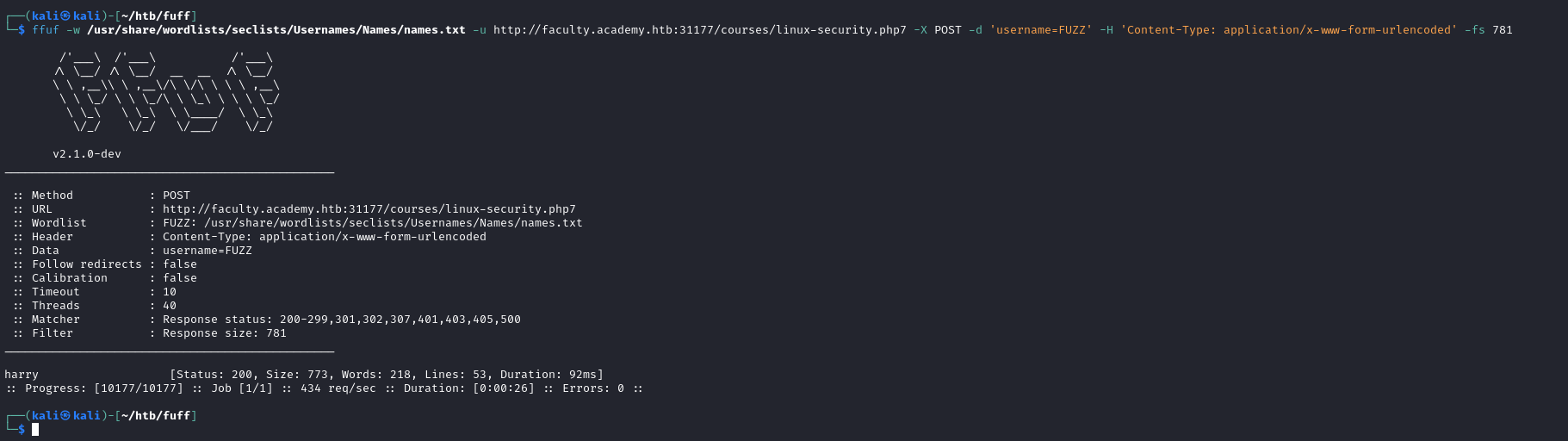
From that I found harry
Then I sent a curl post request using harry as the value in the username parameter and got the flag
curl http://faculty.academy.htb:31177/courses/linux-security.php7 -X POST -d 'username=harry' -H http://faculty.academy.htb:31177/courses/linux-security.php7