Attacking Common Applications Skills Assessment 3
Introduction
During our penetration test our team found a Windows host running on
the network and the corresponding credentials for the Administrator. It
is required that we connect to the host and find the hardcoded password for the MSSQL service.
target: 10.129.95.200
RDP to target with username "Administrator" and password "xcyj8izxNVzhf4z"
What is the hardcoded password for the database connection in the MultimasterAPI.dll file?
Connecting to the machine
xfreerdp3 /u:Administrator /p:xcyj8izxNVzhf4z /v:10.129.95.200Finding the file theyre talking about
open powershell and navigate to the root C:\ (or you could specify this in the command using “
-Path "C:\"
the below command will recursively search a windows machine for a file:
gci -recurse -filter "MultimasterAPI.dll" -File -ErrorAction SilentlyContinue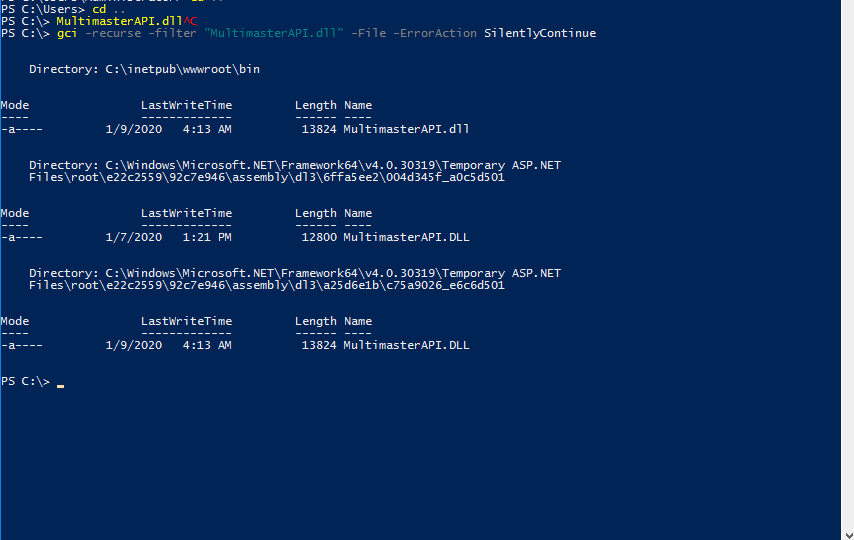
based on the first one being in the webroot I think I will start my investigation into the files with that one.
Funnily enough when launching dnspy from the tools directory on the machine it opens up to MultimasterAPI.dll as the file so I guess I didn’t need to look for it
Clicking through the file to try and get an understanding of the file and what its doing I did find the hard coded credentials in a connection string.
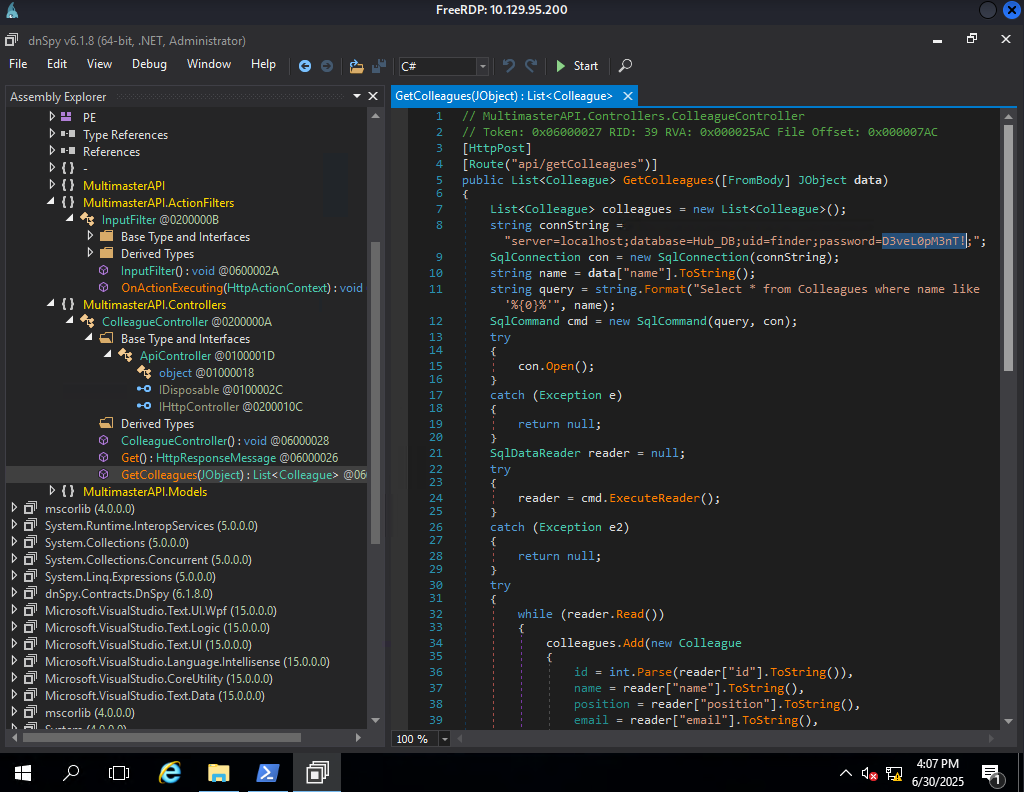
Because I stumbled upon the answer, looking into things a bit more for it appears you can use ctrl+shift+k to search assemblies to parse the DLL for things that may be of interest. If the hard coded credentials happen to be specifically stored in a string you can filter for that too.